 What is XWorm V7.4 Cracked?
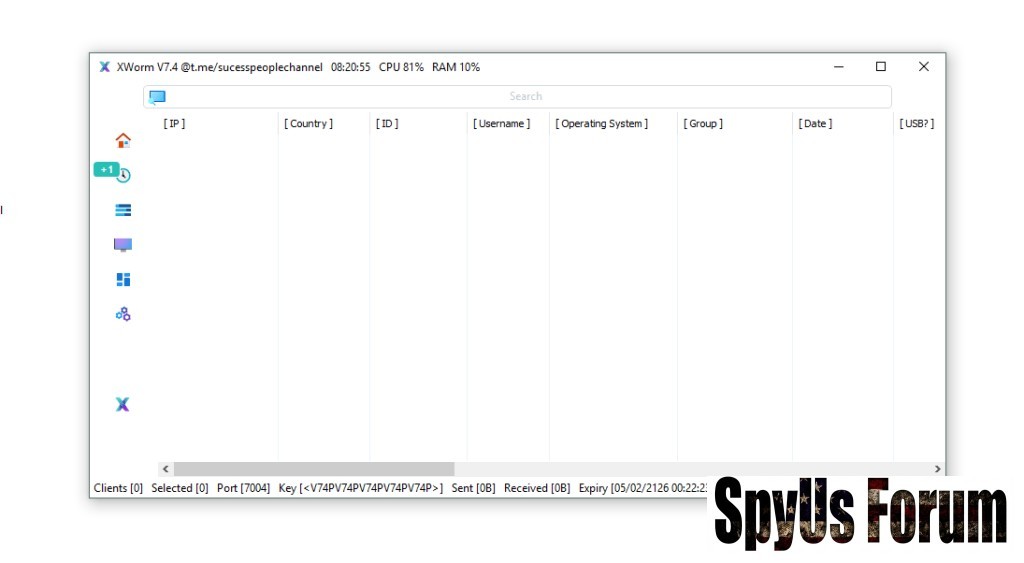
What is XWorm V7.4 Cracked?XWorm V7.4 Cracked refers to an unauthorized modified version of a Remote Access Trojan (RAT) that removes licensing restrictions.
Table of Contents
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
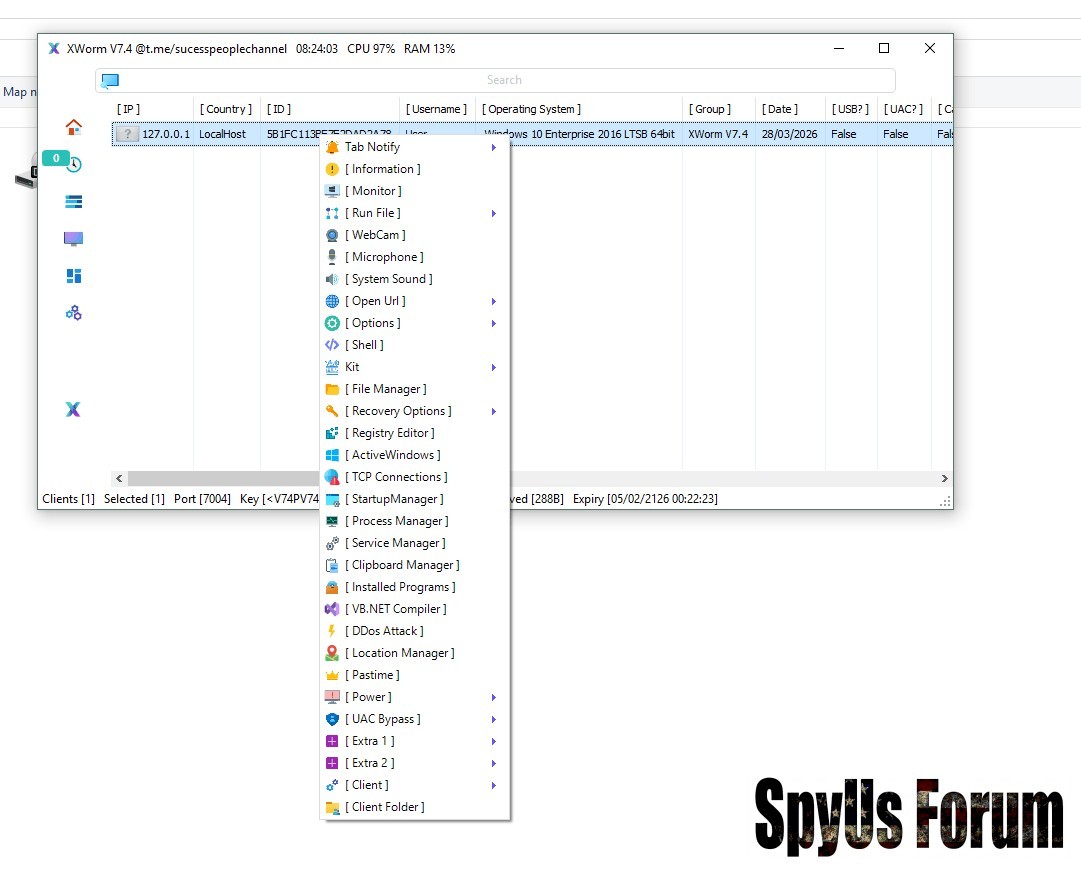
Core Capabilities:
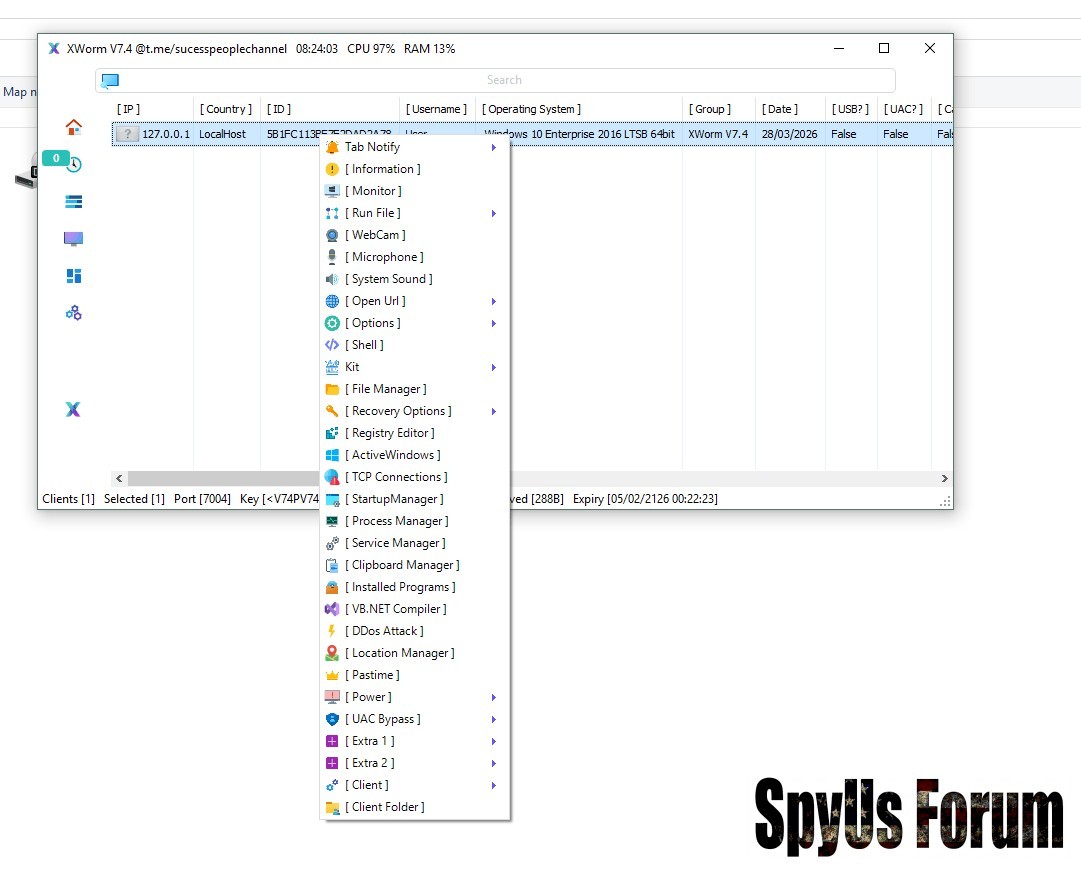
- Remote access to systems
- User surveillance tools
- Credential and data theft
- Financial manipulation (crypto theft)
- Security evasion
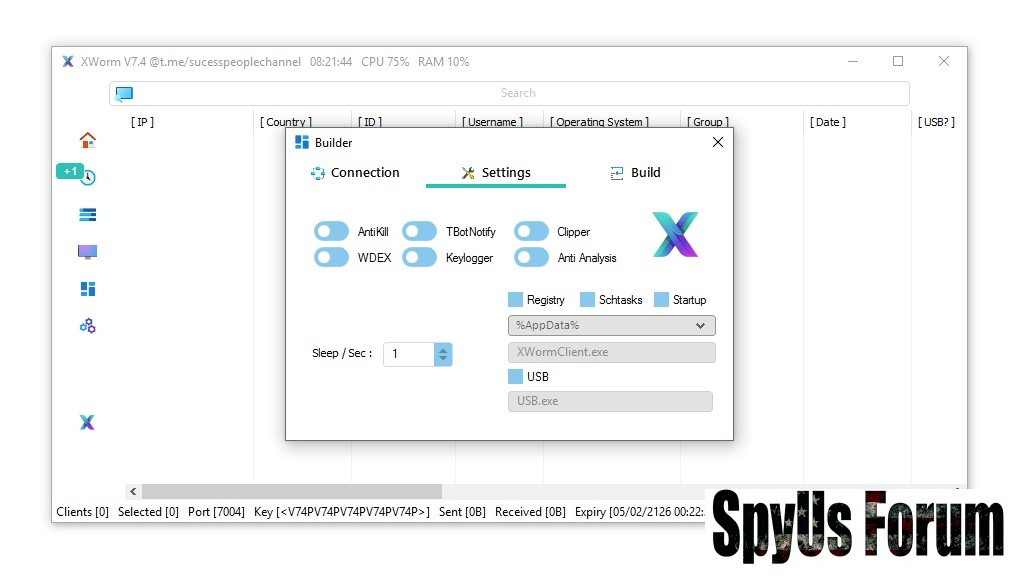
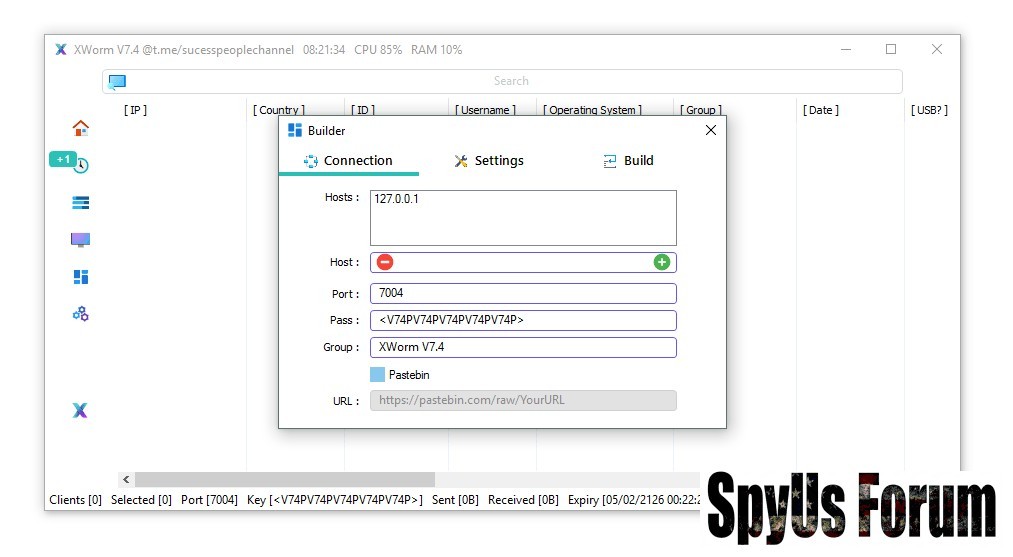
Builder Overview XWorm V7.4 Cracked
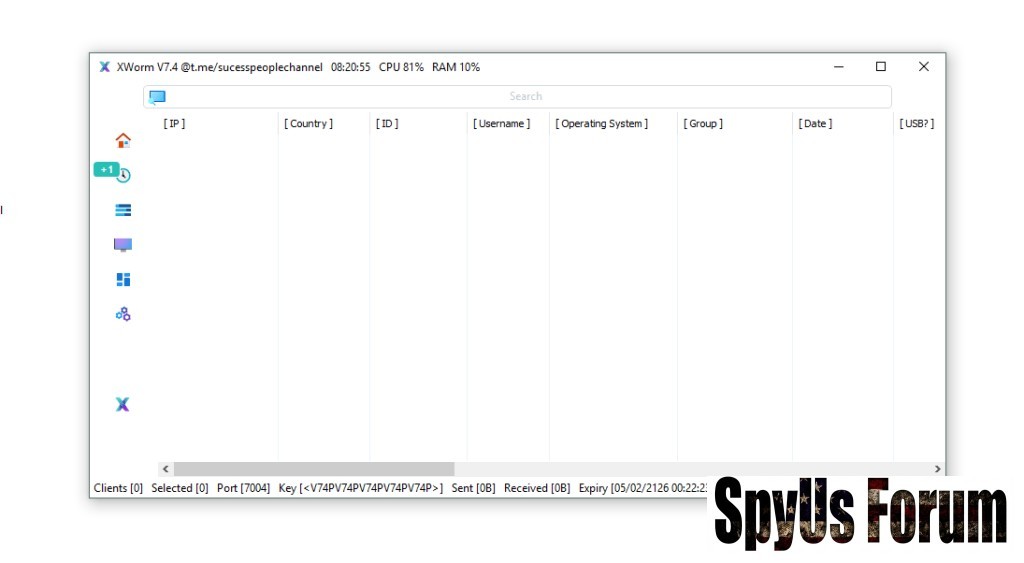 Connection Settings
Connection Settings- Host Configuration
Defines where the infected device connects.
Enables attacker communication with victims. - Port Setup (e.g., 7004)
Communication channel for data transfer. - Connection Key
Used to identify and control victims. - Victim Grouping
Organizes infected systems for easier control.
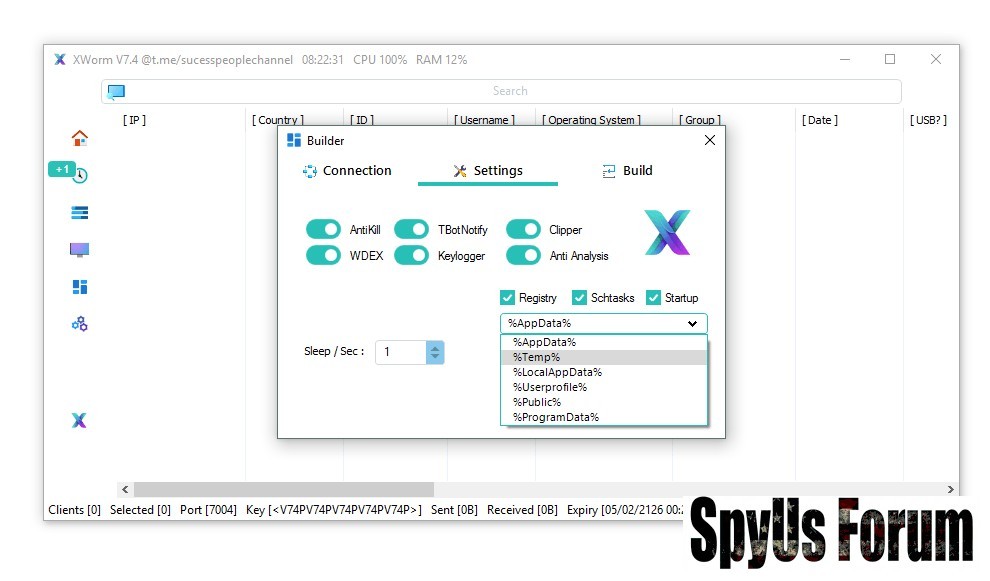
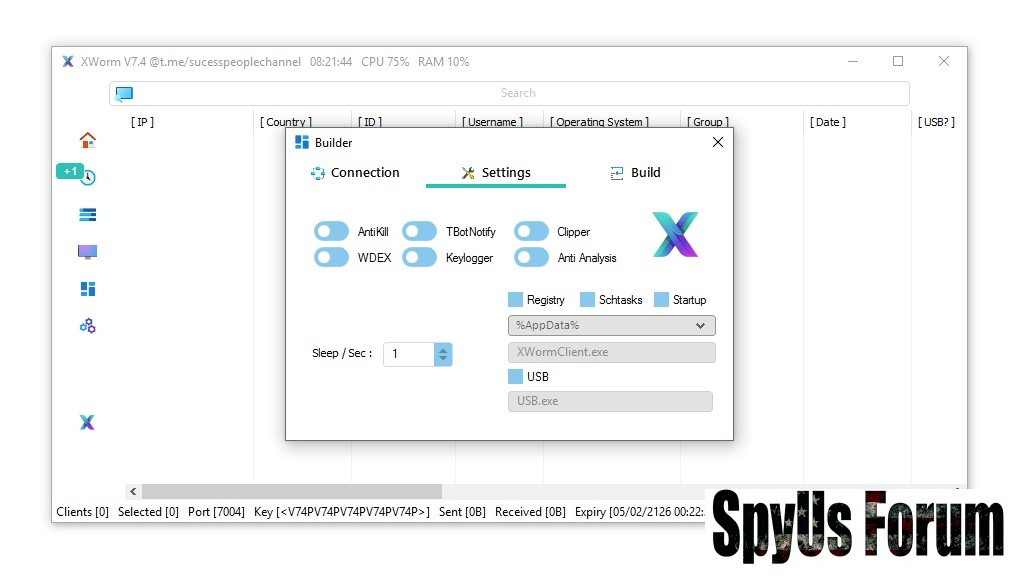
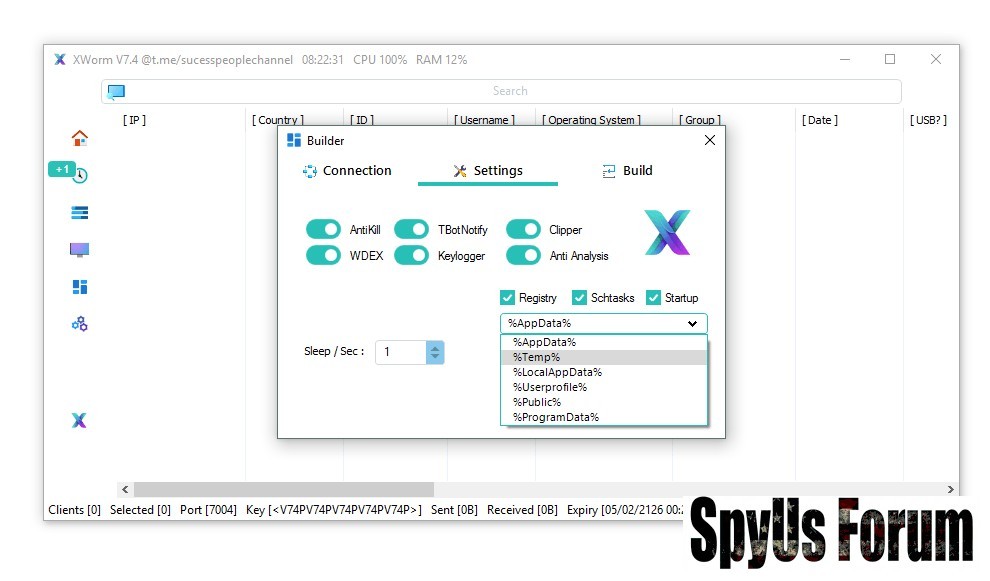
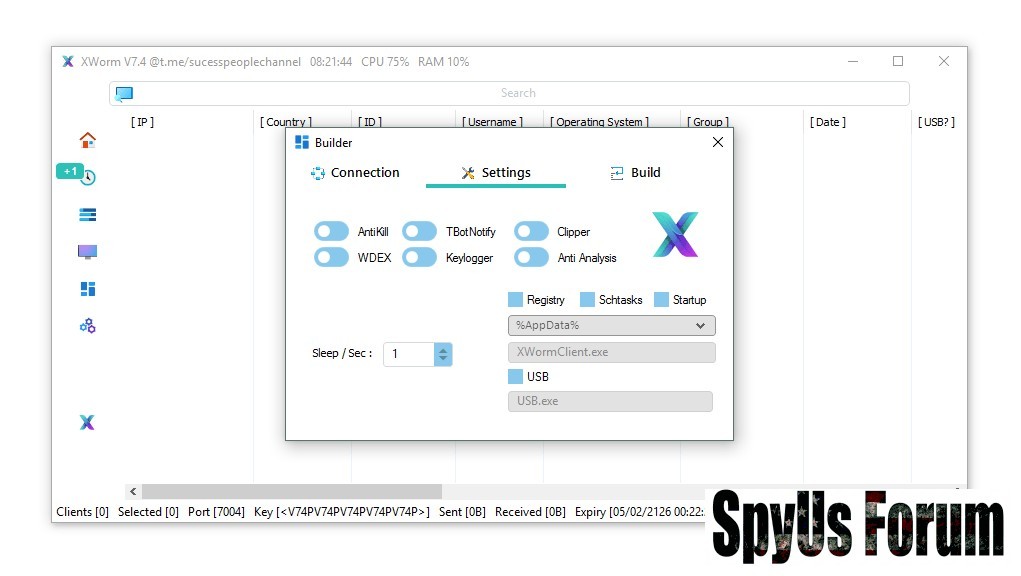
- Registry Auto-Start
Runs malware on system startup. - Scheduled Tasks
Re-executes malware automatically. - Startup Folder Injection
Ensures execution after login.
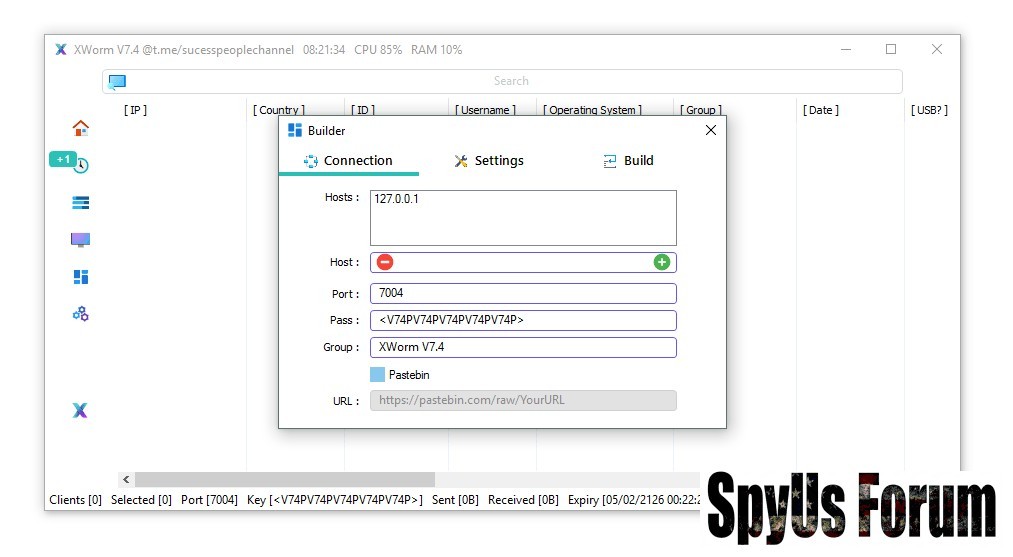
- %AppData% → hidden storage
- %Temp% → temporary but often ignored
- %LocalAppData% → blends with apps
- %ProgramData% → shared system data
- %UserProfile% → user-level persistence
- USB Spread Feature
Infects other devices via USB drives
 Surveillance & Monitoring
Surveillance & Monitoring- Webcam Access
Turns on camera remotely
Used for spying and recording users - Microphone Recording
Captures surrounding audio
Records private conversations - System Audio Capture
Records internal device sound
Includes calls, media, and playback - Keylogger
Records all keystrokes
Steals passwords, OTPs, and messages - Active Window Tracking
Monitors active apps and tabs
Detects sensitive activities - Location Tracking
Estimates user location via IP
Helps identify target region
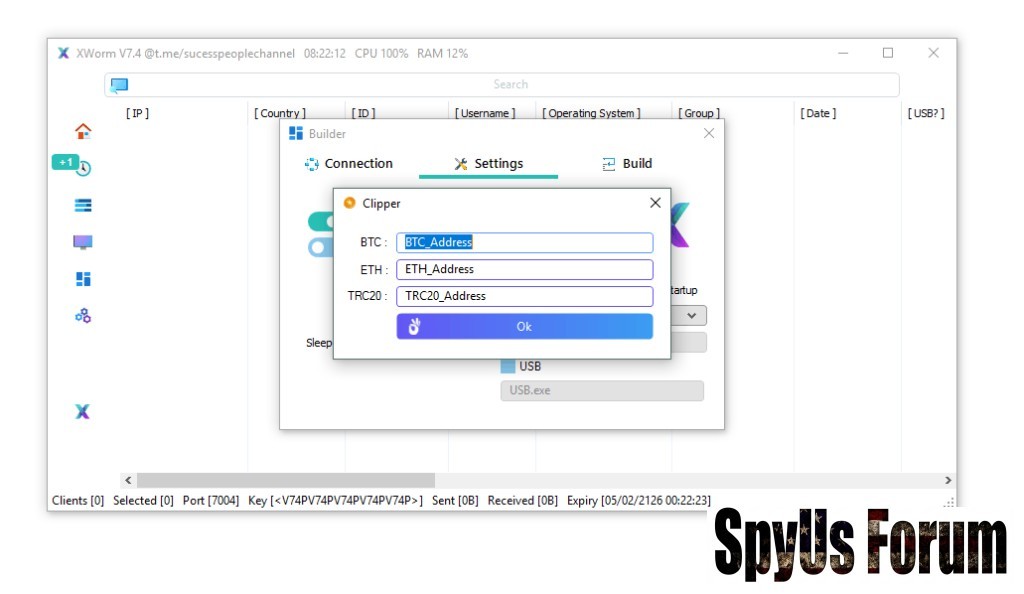
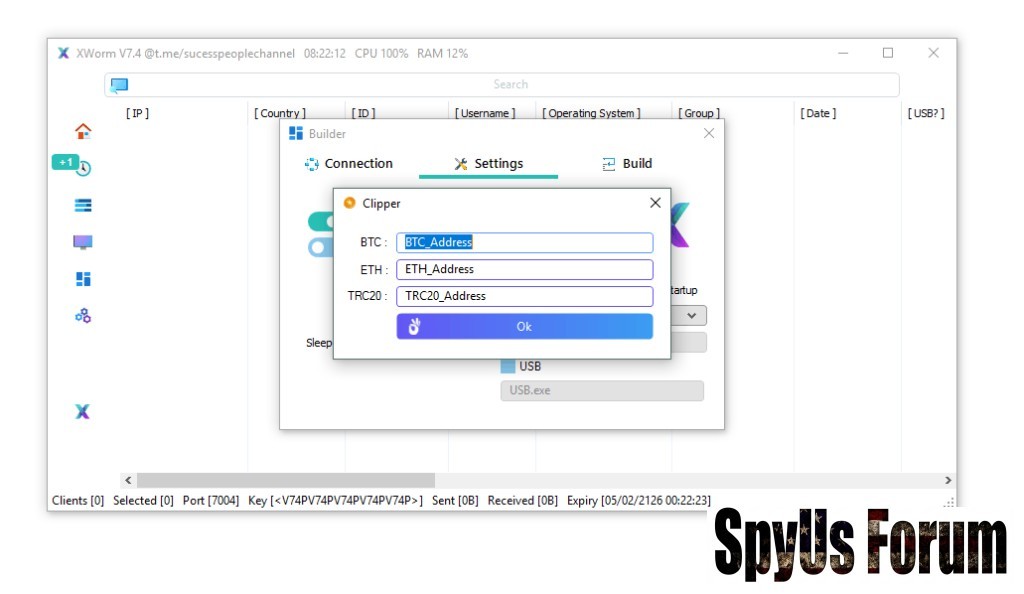
- Clipboard Hijacking (Clipper)
Replaces crypto wallet addresses
Redirects transactions to attacker
- File Manager
Full access to files
View, delete, or steal data - Registry Editor
Modify system settings
Used for persistence and control - Process Manager
Control running programs
Can disable - Service Manager
Manage background services
Maintains hidden activity - DDoS Feature
Uses system to attack websites
Turns device into botnet - UAC Bypass
Skips security prompts
Gains admin privileges - Power Control
Shutdown or restart system
Used to disrupt or hide actions
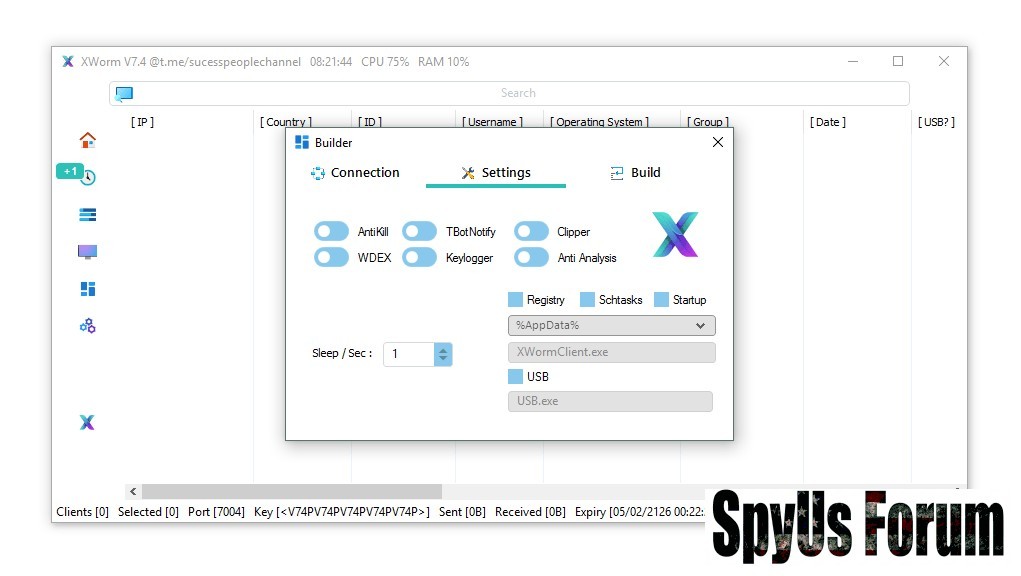
- AntiKill Protection
Prevents termination
Hard to remove manually - Anti-Analysis
Detects sandbox/VM
Avoids detection - Exclusion
Bypasses security tools
Runs undetected
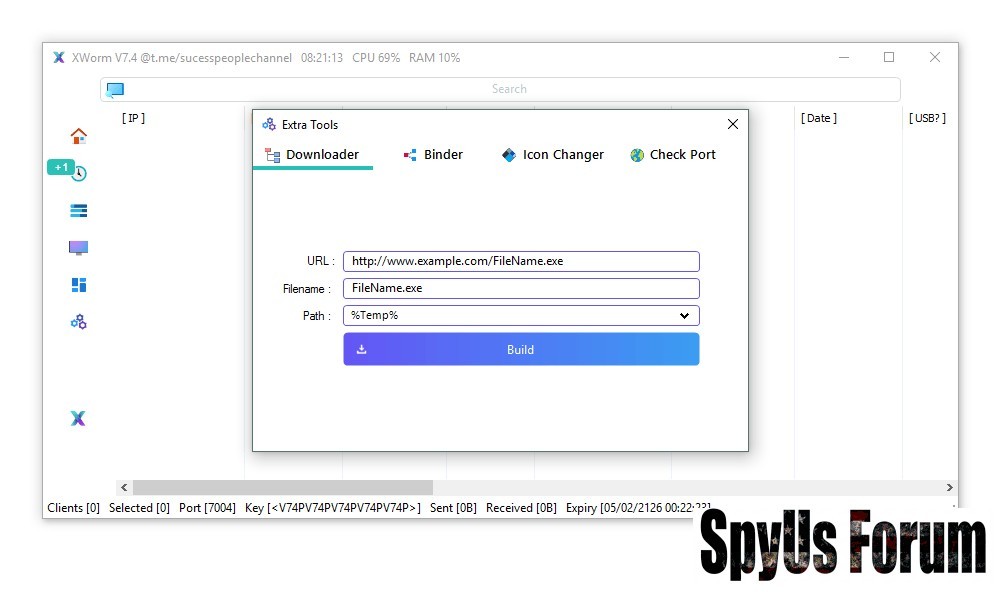
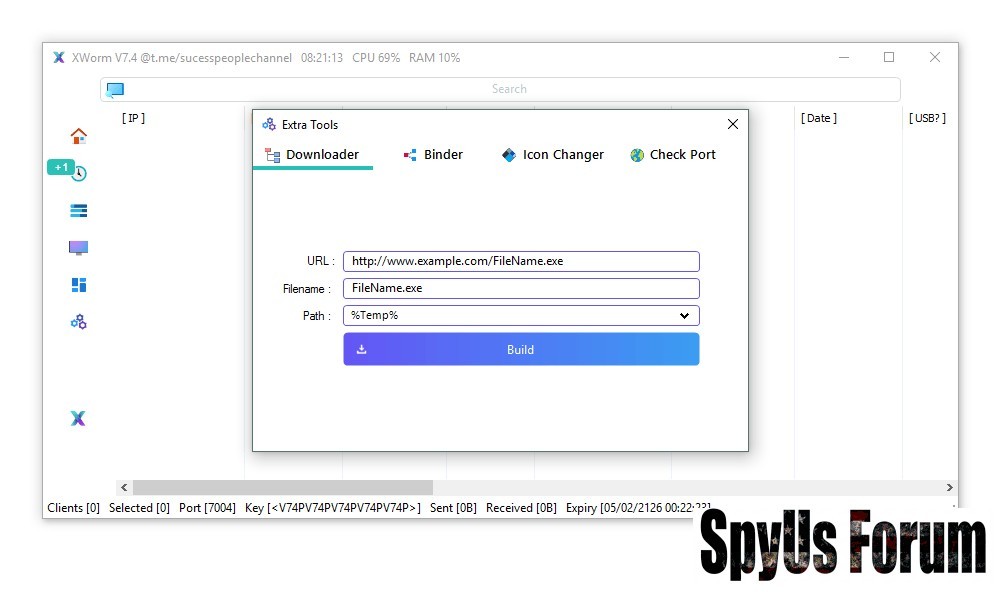
- File Binder
Combines malware with legit files
Tricks users into installing - Icon Changer
Makes files look safe
Increases trust - Downloader
Installs more malware
Expands attack - Built-in Compiler
Generates malware easily
No technical skill required
Using or downloading cracked malware introduces additional dangers:
- Hidden backdoors (even attacker can be attacked)
- Embedded spyware
- No updates or security control
- Legal consequences
Why XWorm V7.4 Cracked is More Dangerous
- Freely available in underground sources
- No license restrictions
- Often modified with extra malicious code
- Increases cybercrime accessibility
Avoid cracked downloads
Do not open unknown files
Use trusted antivirus tools
Disable unknown USB devices
Keep system updated
Download XWorm V7.4 Cracked
Conclusion
XWorm V7.4 Cracked is not just a cybersecurity threat—it is a high-risk malicious tool that can harm both victims and those who use it.
The cracked nature makes it even more unpredictable and dangerous.
Staying informed and avoiding such software is the best defense.
FAQs
What is XWorm V7.4 Cracked?
It is an unauthorized modified version of a Remote Access Trojan without licensing restrictions.
Is XWorm V7.4 Cracked safe to use?
No, it is unsafe, illegal, and may contain hidden malware.
How does it spread?
Through malicious downloads, attachments, and USB devices.
Can it harm the user who installs it?
Yes, cracked versions may include hidden spyware or backdoors.
How to stay safe?
Avoid cracked software and use updated security tools.
Attachments
-
 55c775f43d48aebc617cac60ae7fd2b2.jpg50 KB · Views: 0
55c775f43d48aebc617cac60ae7fd2b2.jpg50 KB · Views: 0 -
 20576ca4dbbea22090eba0bef61a1530.jpg71.4 KB · Views: 0
20576ca4dbbea22090eba0bef61a1530.jpg71.4 KB · Views: 0 -
 846bc94f1fac75b1133c58b40e097c3a.jpg77.5 KB · Views: 0
846bc94f1fac75b1133c58b40e097c3a.jpg77.5 KB · Views: 0 -
 40f96d2d0af12ab198432a0b542ef22e.jpg76.2 KB · Views: 0
40f96d2d0af12ab198432a0b542ef22e.jpg76.2 KB · Views: 0 -
 e8b4e1260014a6d334f456206e1fbbdf.jpg72.4 KB · Views: 0
e8b4e1260014a6d334f456206e1fbbdf.jpg72.4 KB · Views: 0 -
 e49ae13ce460b2e8cfc9be114b3cef3d.jpg81.2 KB · Views: 0
e49ae13ce460b2e8cfc9be114b3cef3d.jpg81.2 KB · Views: 0 -
 069088fa68c3d601c08d584505406a8d.jpg76.2 KB · Views: 0
069088fa68c3d601c08d584505406a8d.jpg76.2 KB · Views: 0 -
 5ccce781b357d7c7a738fdf4f4ca498c.jpg122.6 KB · Views: 0
5ccce781b357d7c7a738fdf4f4ca498c.jpg122.6 KB · Views: 0

