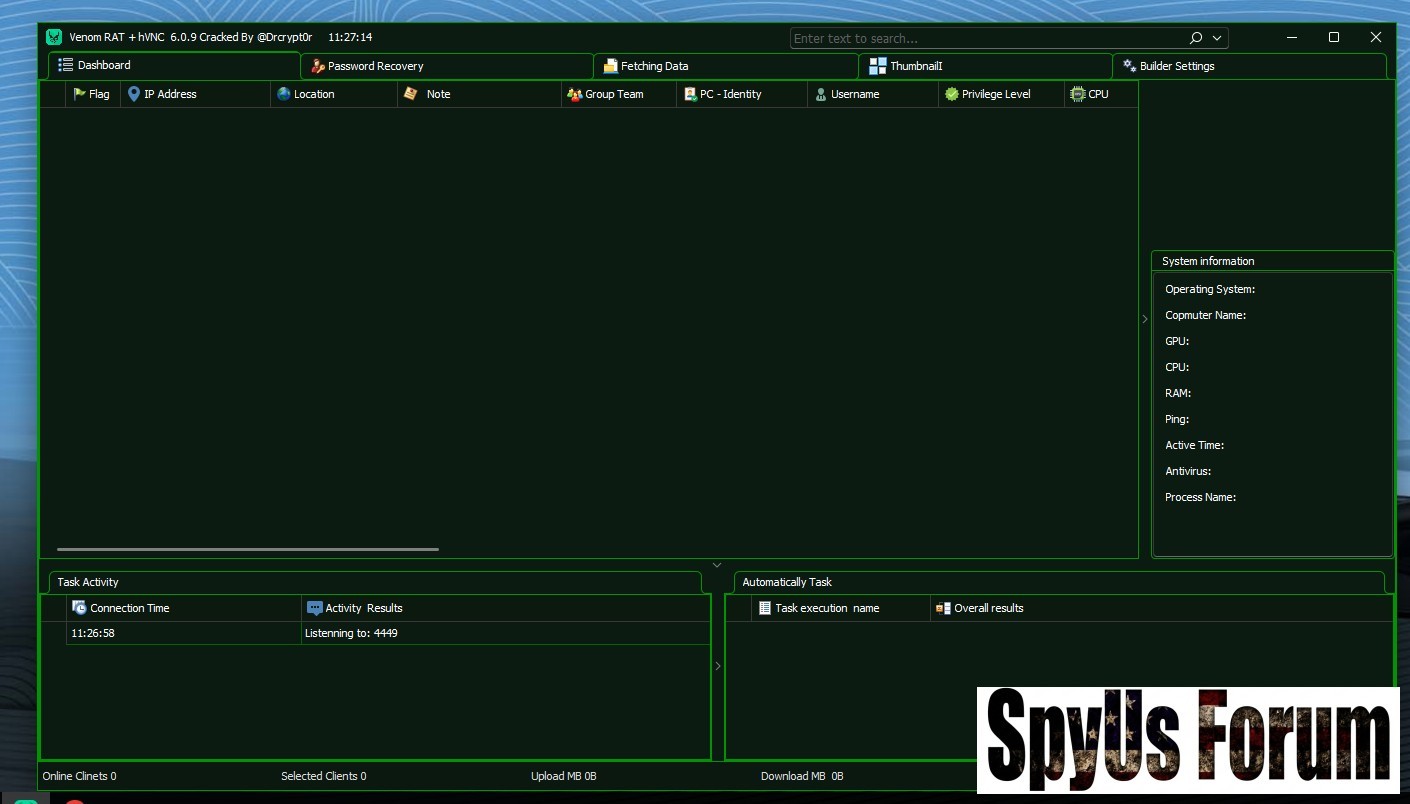
 Venom Pro 6.0.9 RAT Cracked
Venom Pro 6.0.9 RAT CrackedThe rise of Remote Access Trojans (RATs) has significantly reshaped the modern cyber threat landscape. Among the most discussed tools in underground forums is Venom RAT 6.0.9 Cracked, a leaked version of a once-private remote administration tool bundled with powerful hVNC (Hidden Virtual Network Computing) capabilities.
Table of Contents
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
This article provides a deep technical and cybersecurity-focused analysis. Our goal is awareness, not promotion.
What Is Venom Pro 6.0.9 RAT Cracked?
Venom RAT is a Remote Access Trojan (RAT) that allows attackers to control compromised systems remotely. The “cracked” version removes licensing protections, allowing unrestricted access.
 Why it’s dangerous:
Why it’s dangerous:- Accessible to low-skilled attackers
- Rapid global distribution
- Slow detection adaptation
- Victim systems highly exposed
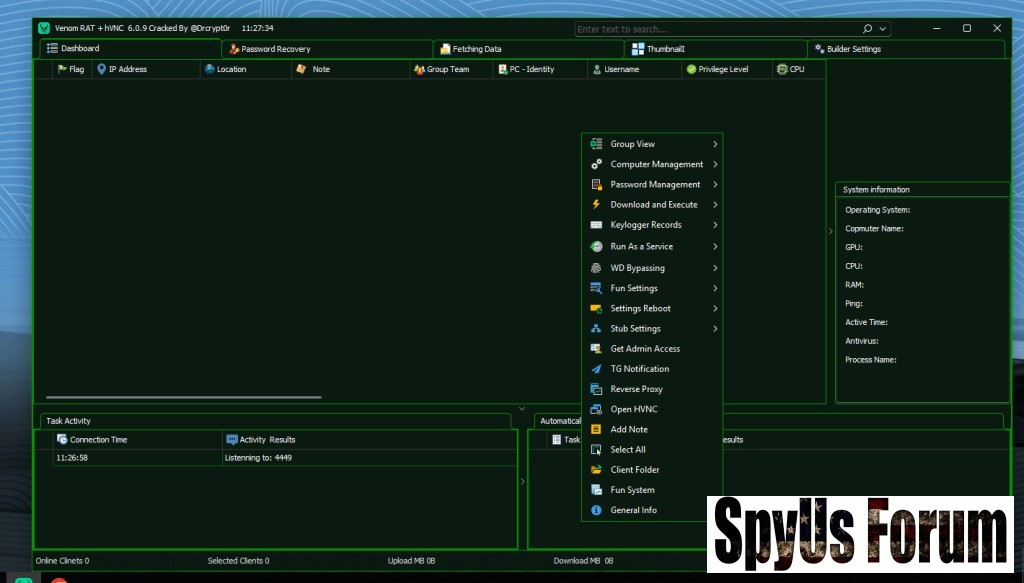
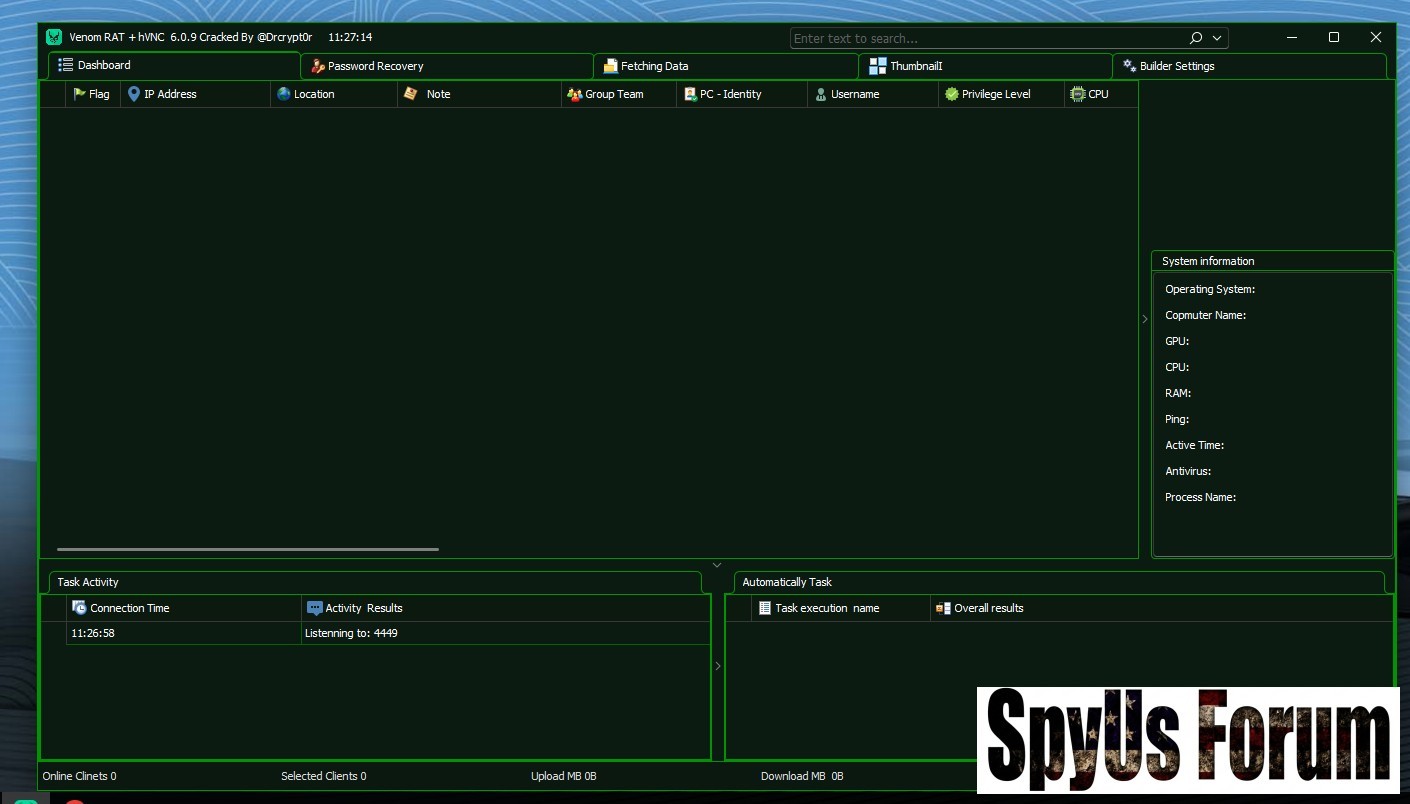
Command-and-Control (C2) Infrastructure
Venom RAT operates on a client-server model:

- C2 Server (Attacker Panel): Control dashboard
- Stub (Payload): Installed on victim machines
- Reverse Connection: Outbound from victim to attacker
Network Configuration Options:

- Custom server IP or DNS
- Configurable listening port (commonly 4449)
- Reverse TCP connection
- Startup registry modifications
- Installation in %AppData%
- Mutex to prevent duplicates
- Anti-VM detection
- Windows Defender bypass
- UAC pr!v!l3g3 3sc@l@t!0n
- Process respawn (anti-kill protection)
- Registry manipulation
- Delayed execution
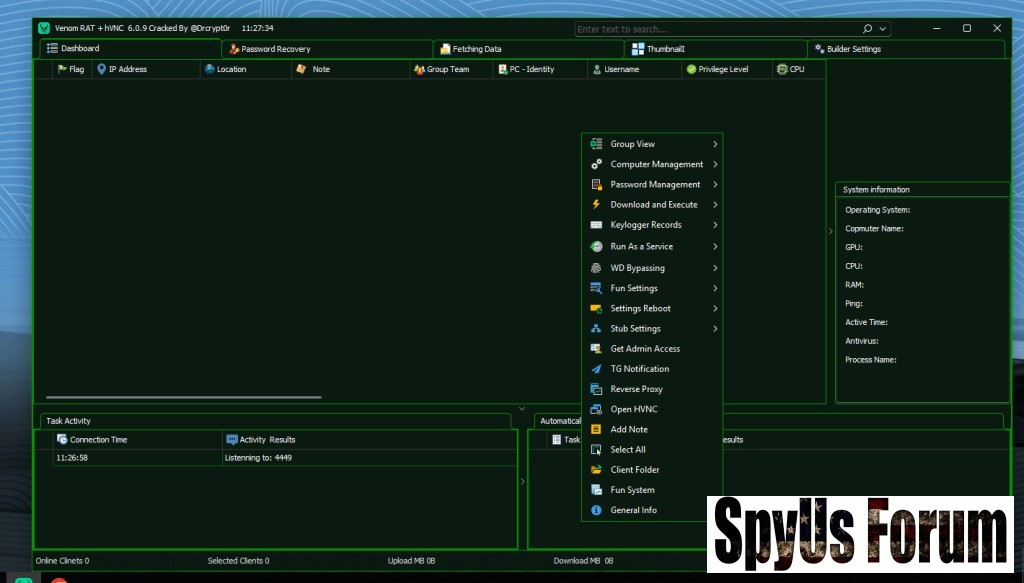
hVNC creates a hidden Windows desktop session invisible to the victim.
 Key benefits for attackers:
Key benefits for attackers:- Victim cannot see mouse or windows
- Full GUI desktop access in parallel session
- Hidden browsers (Chrome, Firefox, Edge, Brave, IE)
- Stealthy file system and PowerShell control
- Reverse connection bypassing firewalls
- Supports WebGL for complex web apps
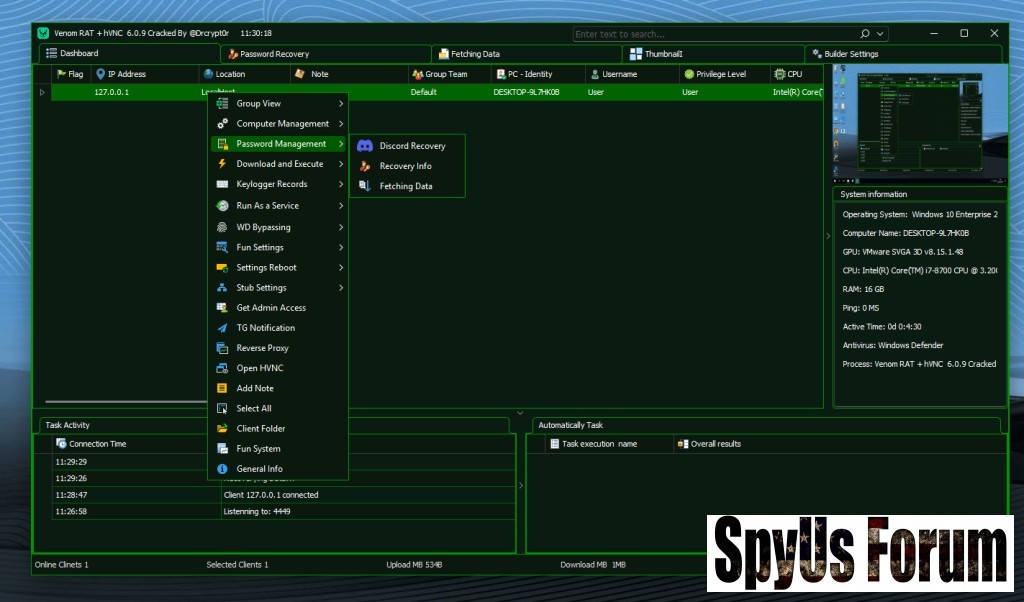
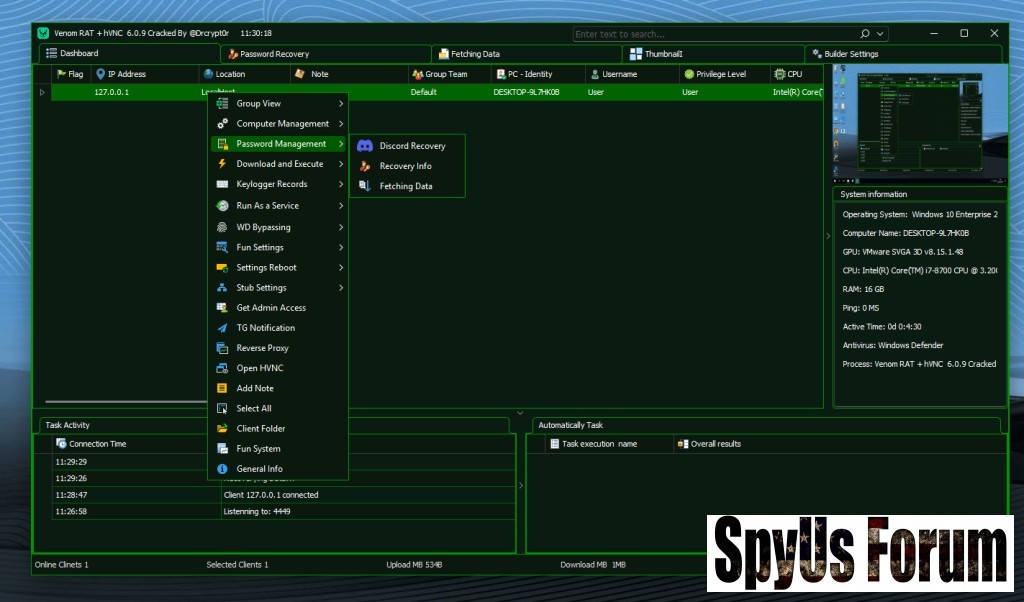
Browser Credential Extraction:

- Google Chrome
- Mozilla Firefox
- Microsoft Edge
- Opera, Brave, Vivaldi, Yandex, Comodo Dragon, Torch Browser
- Saved passwords
- Cookies & browsing history
- Autofill & login data
- FileZilla FTP credentials
- Email client logins (Outlook, Thunderbird)
- Cryptocurrency wallets
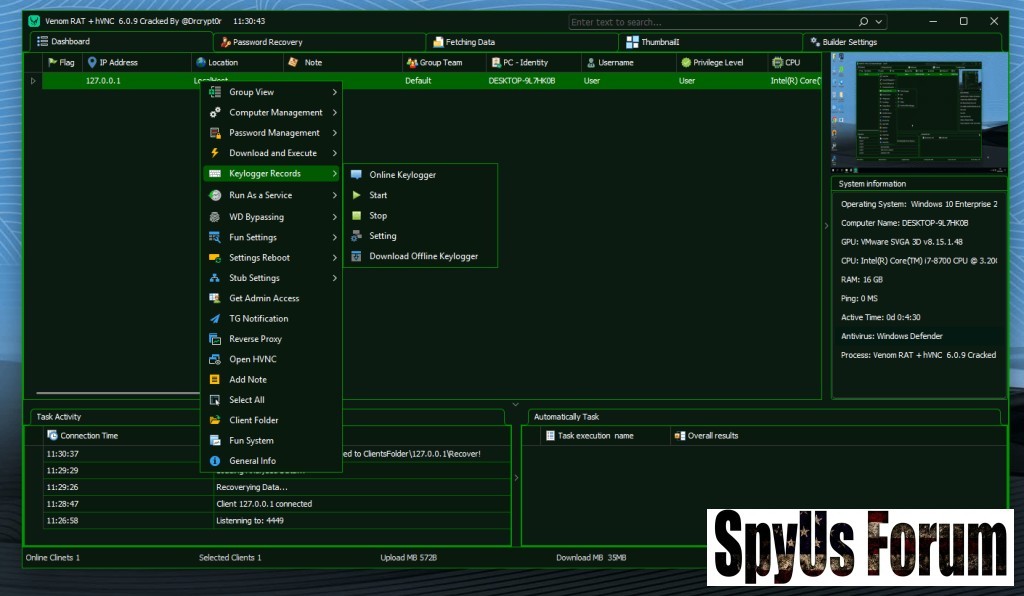
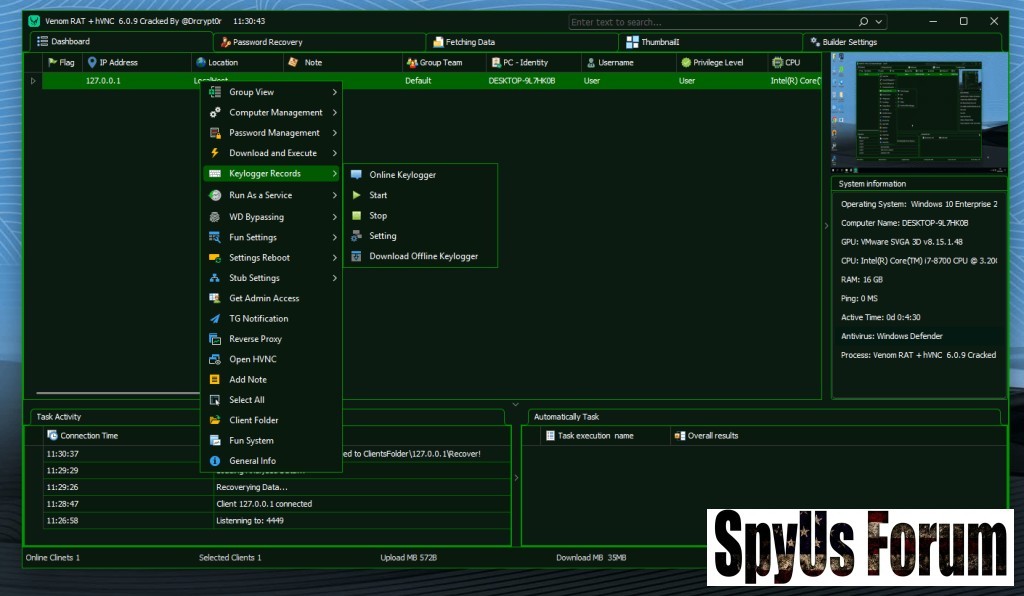
 Keylogging:
Keylogging:- Online and offline keylogging
- Password capture
- Live audio
- Webcam capture
- Screenshots
- Remote file browsing
- Hidden CMD execution

- Memory-based payload execution
- Injection into legitimate processes
- Shellcode export for fileless persistence
- Evades and application whitelisting
- Harder to detect using signature-based methods
- Monitors clipboard for crypto addresses (BTC, ETH, LTC, BCH)
- Replaces addresses with attacker’s wallet
- Leads to irreversible financial loss

- Auto-password recovery on connection
- Scheduled command execution
- Remote updates
- Bulk deployment

- Auto-copy to USB drives
- Hides files and folders
- Creates autorun triggers for new systems
Combination of:
- hVNC stealth access
- Credential harvesting
- Financial theft modules
- Surveillance tools
- Anti-detection mechanisms
- Free global distribution
- Rapid repackaging
- High adoption among novice threat actors
For General Users:
- Avoid cracked
- Enable antivirus/Windows Defender
- Use two-factor authentication
- Avoid unknown attachments
- Disable USB autorun
- Monitor outbound traffic anomalies
- Enable endpoint detection & response (EDR)
- Restrict PowerShell usage
- Enforce least privilege policies
- Monitor registry startup keys
- Behavioral detection rules
- Track hidden desktop session creation
- Monitor suspicious clipboard processes
- Implement memory scanning tools
Final Thoughts: Knowledge Is Power
Venom Pro 6.0.9 RAT Cracked illustrates the sophistication of modern RATs. By analyzing hVNC hidden sessions, password harvesting, and stealth features, defenders can:
- Build stronger detection systems
- Educate users
- Harden endpoints
- Prevent data and financial loss
Attachments
-
 068400ce0201306be8442ee2214532c9.jpg89.1 KB · Views: 0
068400ce0201306be8442ee2214532c9.jpg89.1 KB · Views: 0 -
 794b21cd2a3b9a0986a5787ca292ea7e.jpg108.5 KB · Views: 0
794b21cd2a3b9a0986a5787ca292ea7e.jpg108.5 KB · Views: 0 -
 612dbc7d1816c2044aea841c67faef7f.jpg109.9 KB · Views: 0
612dbc7d1816c2044aea841c67faef7f.jpg109.9 KB · Views: 0 -
 b8c3cc6fea50b7050744f414e262f679.jpg121.7 KB · Views: 0
b8c3cc6fea50b7050744f414e262f679.jpg121.7 KB · Views: 0 -
 76411f50e440b0c6bda0845f71283aec.jpg118.8 KB · Views: 0
76411f50e440b0c6bda0845f71283aec.jpg118.8 KB · Views: 0 -
 33a399980edca9957ab7fa3e9d038872.jpg115.3 KB · Views: 0
33a399980edca9957ab7fa3e9d038872.jpg115.3 KB · Views: 0 -
 7ce6afabfc5a58567821cdd279fc9050.jpg114.9 KB · Views: 0
7ce6afabfc5a58567821cdd279fc9050.jpg114.9 KB · Views: 0 -
 5dad0449642d0b6b883aa8210d8b2067.jpg117.5 KB · Views: 0
5dad0449642d0b6b883aa8210d8b2067.jpg117.5 KB · Views: 0 -
 353ae20197f689c8050d9e7c9f2765a9.jpg115.3 KB · Views: 0
353ae20197f689c8050d9e7c9f2765a9.jpg115.3 KB · Views: 0 -
 1fa65dae9284a52fb3850fae116b6c06.jpg110.5 KB · Views: 0
1fa65dae9284a52fb3850fae116b6c06.jpg110.5 KB · Views: 0 -
 df5447afcae24bcbfd2d190b1547afb0.jpg132.6 KB · Views: 0
df5447afcae24bcbfd2d190b1547afb0.jpg132.6 KB · Views: 0

