 Introduction: The Rising Threat of SpyNote X Pro v7.2.0.0 Cracked Malware
Introduction: The Rising Threat of SpyNote X Pro v7.2.0.0 Cracked MalwareThe Android malware ecosystem continues to evolve, and one of the most persistent threats is SpyNote. The version widely promoted online as SpyNote X Pro v7.2.0.0 Cracked is being circulated across underground forums and suspicious download portals.
Table of Contents
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
Despite being marketed as a “monitoring solution,” this is in reality a Remote Access Trojan (RAT) that allows attackers to fully control infected devices. This article provides a cybersecurity-focused breakdown of its capabilities, infection techniques, and risks.
What Is SpyNote X Pro v7.2.0.0 Cracked?
SpyNote is a well-known Android Remote Access Trojan (RAT) that enables cybercriminals to remotely monitor, spy on, and manipulate compromised smartphones.
Once installed:
- The attacker gains full administrative-style control
- The victim’s device becomes a remote surveillance tool
- Sensitive data can be stolen silently
This dramatically increases the number of potential attackers.
How SpyNote X Pro v7.2.0.0 Cracked Spreads
Unlike legitimate apps, SpyNote does not typically spread via official stores like Google Play Store without heavy obfuscation.
 Instead, attackers rely on social engineering.
Instead, attackers rely on social engineering.Phishing Websites
Fraudulent websites mimic trusted platforms and trick users into downloading malicious APK files disguised as games, utilities, or updates.
sm!sh!ng (SMS Phishing)
Victims receive text messages containing malicious download links disguised as:
- Banking alerts
- Package delivery notifications
- Media player updates
- Security warnings
The “builder” includes a binding feature that merges the RAT with legitimate apps. When users install the visible app, the malicious payload installs silently in the background.
Core Capabilities of SpyNote X Pro v7.2.0.0 Cracked
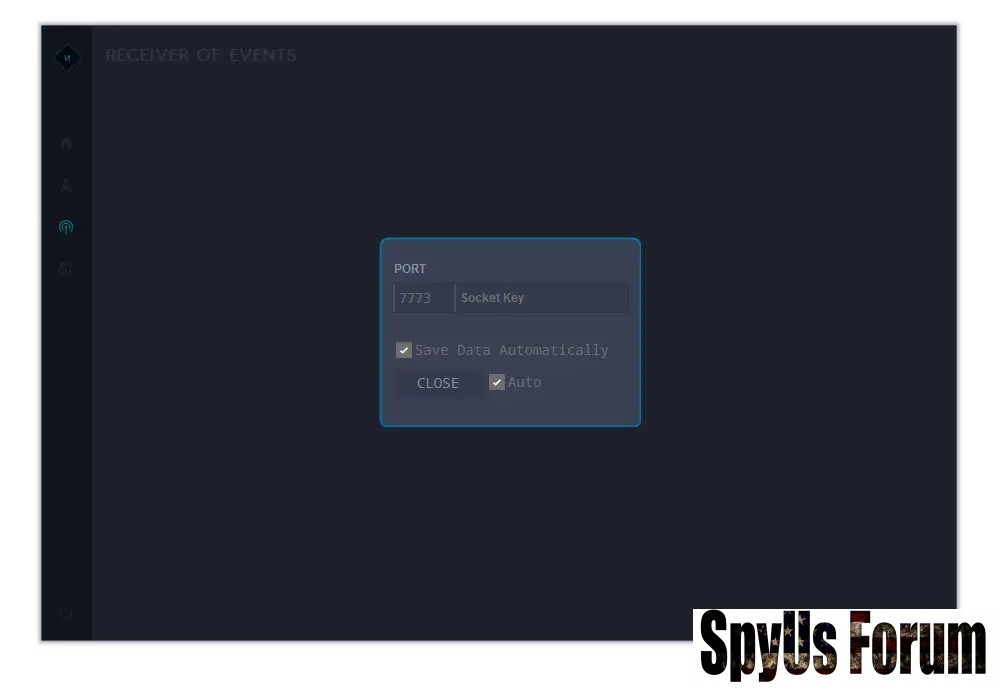
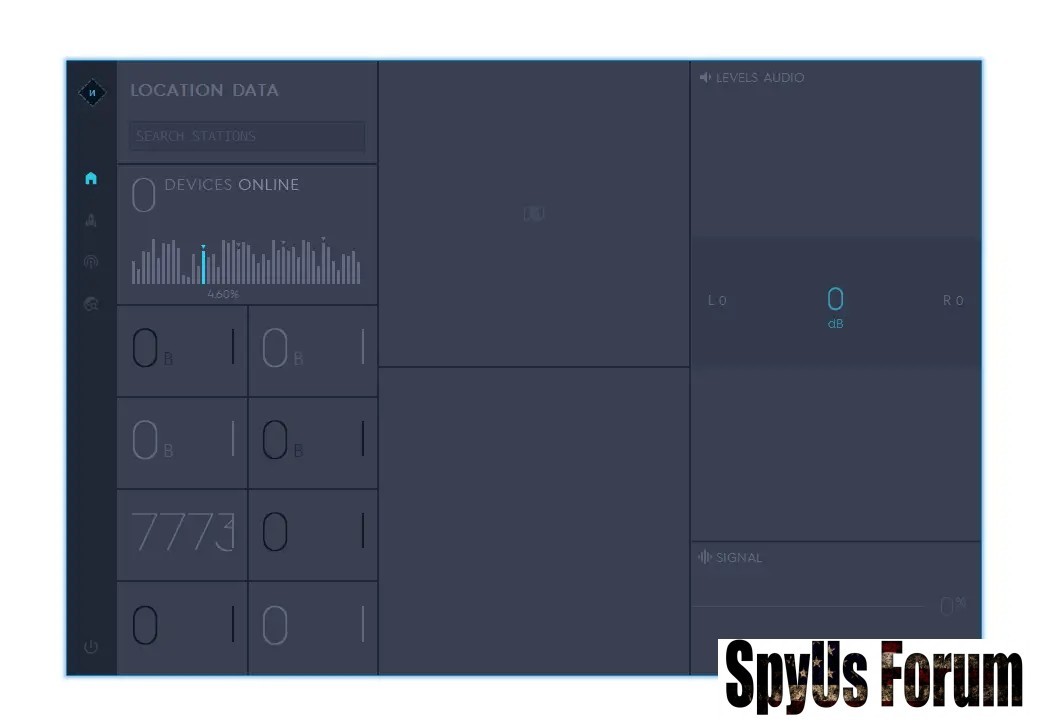
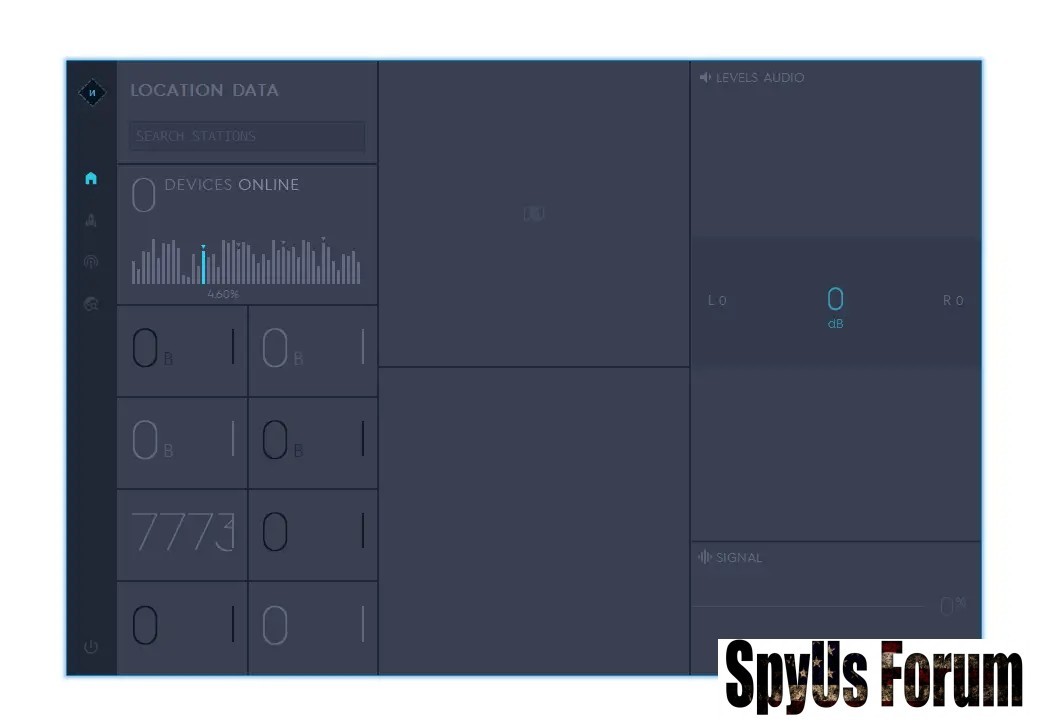
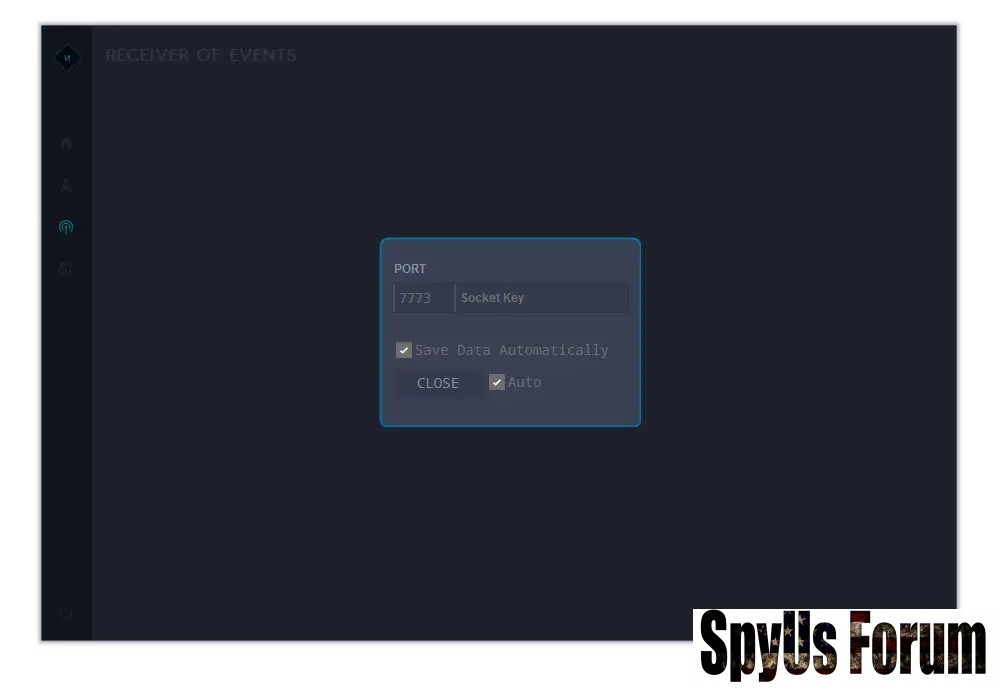
SpyNote is essentially a mobile surveillance suite controlled via a command-and-control (C2) server.
 1. Live Surveillance Features
1. Live Surveillance Features- Listen to live microphone audio
- Capture photos and record videos remotely
- Continuous GPS location tracking
- Record calls
- Read and send SMS messages
2. Data Theft & Credential Harvesting
SpyNote is built to extract valuable data.
- Full file system access
- Download files from victim device
- Keystroke logging (password theft)
- Capture banking credentials and 2FA codes
3. Persistence & Evasion Techniques
Modern versions use advanced stealth strategies.
Hidden Application Icon
The launcher icon is removed, making detection difficult.
Abuse of Accessibility Services
SpyNote requests Android accessibility permissions, allowing it to:
- Auto-grant additional permissions
- Read on-screen text
- Block attempts to uninstall
- Simulate screen taps
Persistent Background Services
If terminated, the malware automatically restarts using broadcast receivers.
4. Remote Control & Device Manipulation
The misleadingly named “Fun Panel” allows attackers to:
- Display fake messages for phishing
- Trigger device vibrations or actions
- Remotely install additional APKs
- Deploy ransomware or additional spyware
Why “No Root Required” Makes It More Dangerous
Older Android spyware required root access, which limited infections to technically modified devices.
SpyNote X Pro v7.2.0.0 Cracked works without root access.
That means:
- Any standard Android device can be infected
- No advanced technical modifications are required
- Users only need to grant permissions (often unknowingly)
Consequences of SpyNote Infection
An infected device can lead to catastrophic outcomes:
Financial Loss
Banking credentials and authentication codes can be stolen.
Identity Theft
Personal data may be used to impersonate victims.
Physical Stalking
Real-time GPS tracking enables location monitoring.
Blackmail & Extortion
Private recordings and images may be used for coercion.
How to Protect Yourself from Android RATs
To prevent infection:
- Only download apps from official app stores
- Disable “Install from Unknown Sources”
- Carefully review permission requests
- Avoid clicking SMS links from unknown senders
- Install reputable mobile security software
- Keep Android OS updated
- Disconnect from the internet
- Backup essential files
- Perform a factory reset
- Change all passwords from a secure device
Final Thoughts: A Serious Mobile Security Threat
SpyNote X Pro v7.2.0.0 Cracked is not a harmless utility — it is a professional-grade Android surveillance tool used for malicious purposes.
Its powerful spying capabilities, stealth persistence mechanisms, and publicly distributed cracked builders make it a significant cybersecurity threat.
For security researchers, analyzing such malware is essential for improving detection systems. For everyday users, awareness and cautious app installation habits are the best defense.