 What is Skuld Stealer 2026?
What is Skuld Stealer 2026?Table of Contents
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
-
You must be registered for see links
-
You must be registered for see links
The project has attracted attention in the cybersecurity community because its source code is publicly available, allowing attackers to customize and deploy the malware in different cyber campaigns.
 Since Skuld Stealer 2026 is developed using Go (Golang), the compiled binaries are usually large and harder to analyze. This characteristic can help attackers evade certain security detection techniques.
Since Skuld Stealer 2026 is developed using Go (Golang), the compiled binaries are usually large and harder to analyze. This characteristic can help attackers evade certain security detection techniques.Skuld Stealer 2026 falls under the category of infostealer malware, which is commonly used to steal digital credentials, online accounts, and financial information.
Key Features of Skuld Stealer
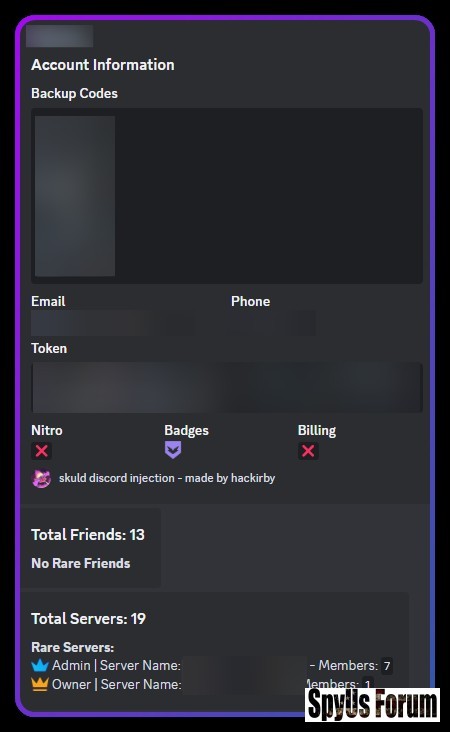
Skuld Stealer 2026 contains several powerful modules that allow it to collect different types of sensitive information from infected systems.
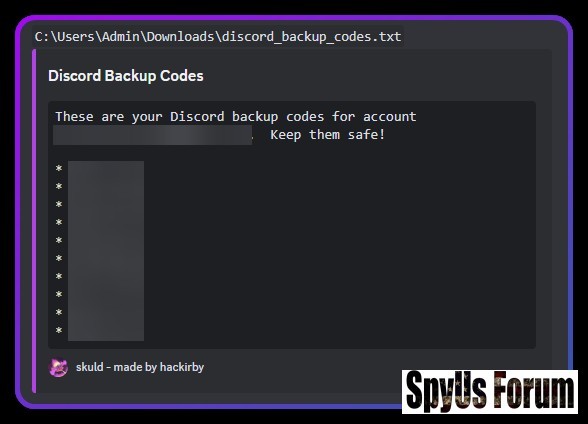
Credential Theft
One of the primary functions of Skuld Stealer 2026 is stealing stored login credentials from .
 Data Collected
Data Collected- Saved browser passwords
- Usernames and login credentials
- Email account details
- Autofill and form data
 Capabilities
Capabilities- Captures authentication tokens
- Sends stolen tokens to attacker servers
- Enables instant account hijacking
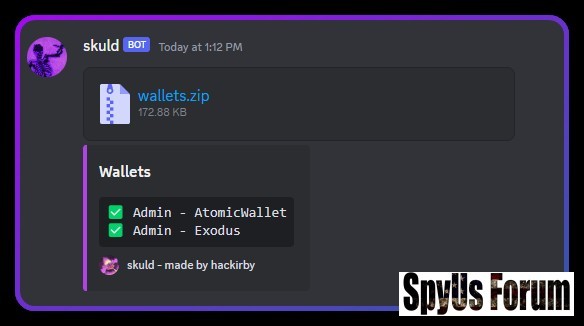
Skuld Stealer 2026 is also capable of targeting local cryptocurrency wallet files stored on a system.
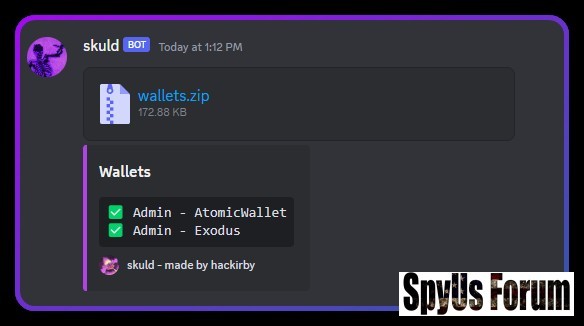 Wallet Data Collected
Wallet Data Collected- Wallet configuration files
- Private keys and wallet credentials
- Local wallet storage information
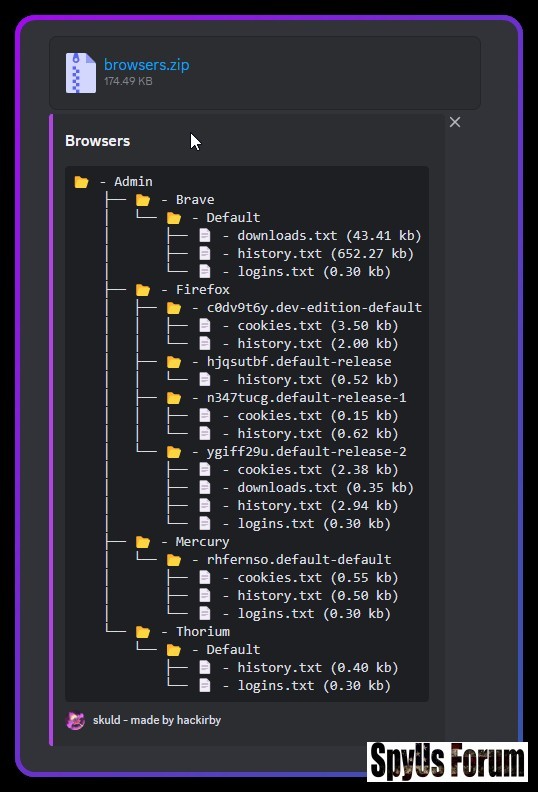
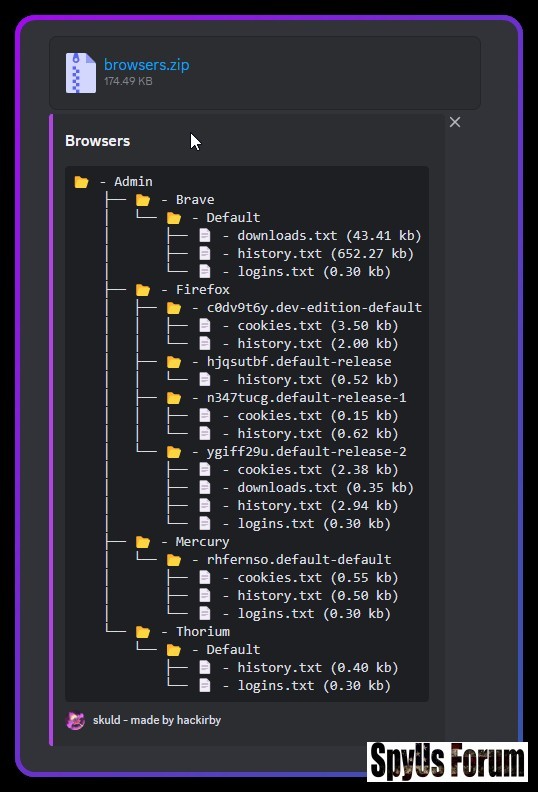
Browser Data Extraction
The malware scans installed web browsers and extracts sensitive information.
 Browser Data Stolen
Browser Data Stolen- Cookies and session tokens
- Browsing history
- Stored login credentials
- Autofill personal data
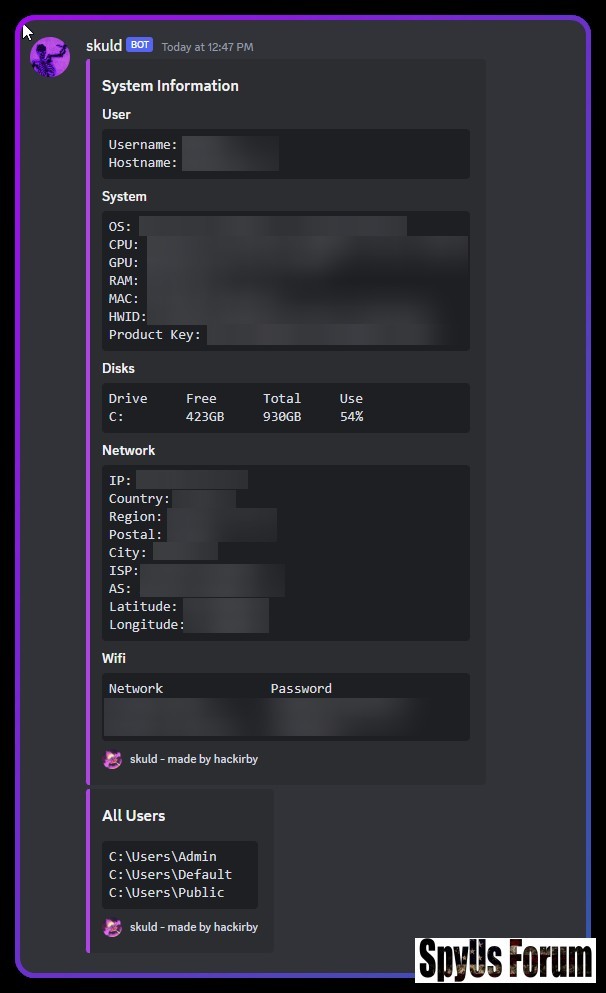
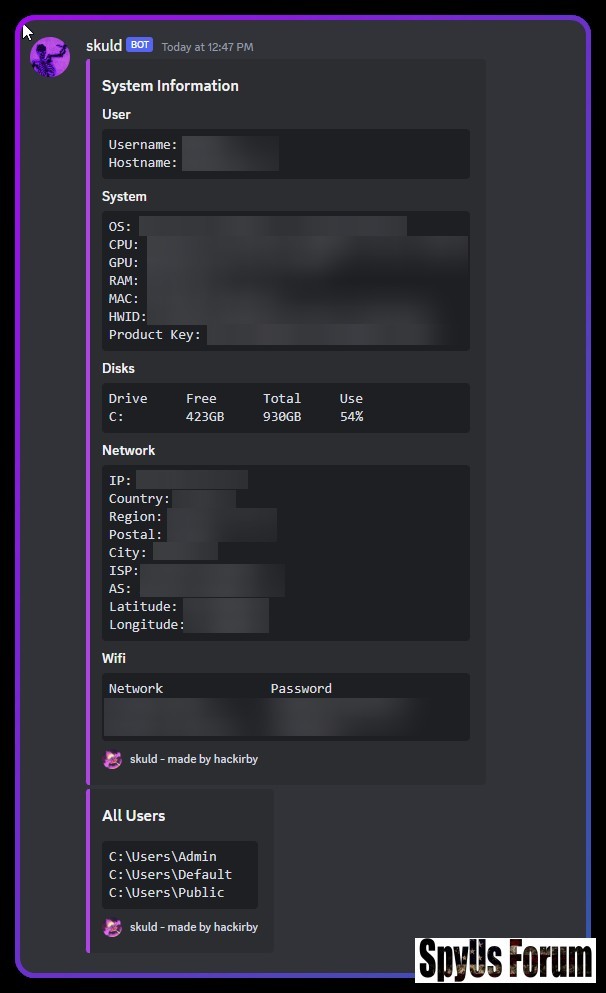
System Information Collection
Skuld Stealer 2026 also collects detailed information about the victim’s device.
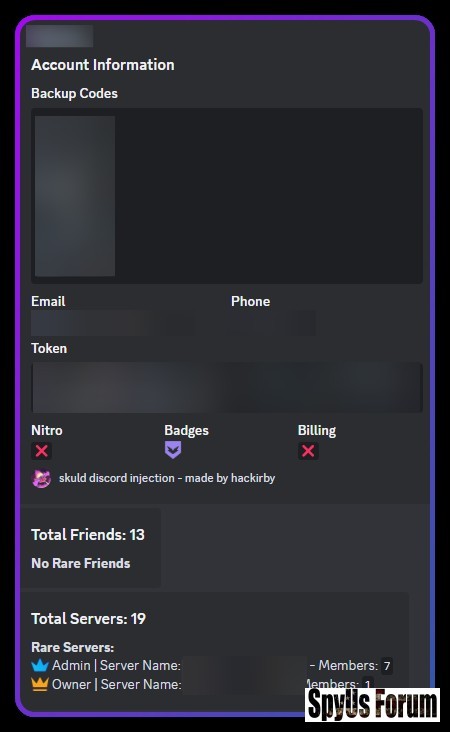 System Data Collected
System Data Collected- CPU information
- GPU details
- RAM size
- Operating system version
- Network and IP details
How Skuld Stealer Works
Skuld Stealer 2026 usually operates using a multi-stage attack process.
Initial Execution
When the malware is executed on a victim’s system, it loads configuration settings and begins scanning the system for valuable information.
Security Bypass
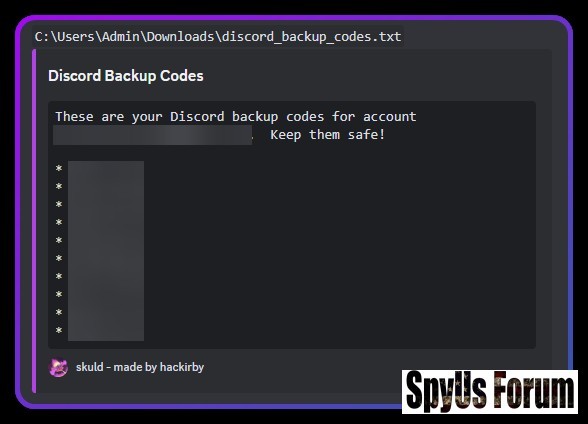
Skuld Stealer 2026 attempts to bypass certain security protections such as:
- Basic detection
- Client modifications designed to protect tokens
- Login credentials
- Email changes
- Password updates
- Two-factor authentication events
After collecting data, Skuld Stealer 2026 compiles the stolen information and transmits it to attacker-controlled infrastructure.
The data is usually formatted and sent automatically once the collection phase is complete.
Technical Architecture of Skuld Stealer
Skuld Stealer 2026 is developed using Golang, a modern programming language known for producing large compiled binaries.
Advantages for Malware Developers
- Fast execution speed
- Large compiled binaries
- Difficult static analysis
- Cross-platform compatibility
Skuld Stealer 2026 typically includes several functional modules.
Core Modules
- Anti-Virtual Machine detection
- Browser credential extractor
- Cryptocurrency wallet collector
- System information module
Cybersecurity Risks of Skuld Stealer
Infostealers like Skuld Stealer 2026 pose serious threats to both individuals and organizations.
Major Security Risks
- Account hijacking
- Cryptocurrency theft
- Email account compromise
- Identity theft
- Loss of sensitive personal data
How to Protect Against Skuld Stealer
Preventing infostealer infections requires good cybersecurity practices.
Security Recommendations
Protection Tips
- Avoid downloading suspicious or cracked software
- Keep operating systems and browsers updated
- Use reliable antivirus security solutions
- Enable multi-factor authentication on accounts
- Monitor unusual login activity
Skuld Stealer 2026 vs Other Info Stealers
MalwareLanguageMain Target
Skuld Stealer 2026Golang
RedLine StealerC++Browser credentials
Raccoon StealerC++Cryptocurrency wallets
Luna GrabberPython
The increasing use of Golang-based malware indicates a shift toward modern programming frameworks in cybercrime.
Download Skuld Stealer
Final Thoughts
Because the malware is modular and easily customizable, it can be adapted for various cybercrime operations. Understanding its functionality is essential for improving detection strategies and strengthening cybersecurity defenses.
Attachments
-
 05200b80bc3a07c60519ca7ff93c0293.jpg75.5 KB · Views: 0
05200b80bc3a07c60519ca7ff93c0293.jpg75.5 KB · Views: 0 -
 163ceafd949d7304b439225423d8ff71.jpg96 KB · Views: 0
163ceafd949d7304b439225423d8ff71.jpg96 KB · Views: 0 -
 fca57c9ca4a24de2d4c57819dd7b6ad3.jpg36.4 KB · Views: 0
fca57c9ca4a24de2d4c57819dd7b6ad3.jpg36.4 KB · Views: 0 -
 6d250aba4f5fb556edcb94f9c7848f08.jpg28.9 KB · Views: 0
6d250aba4f5fb556edcb94f9c7848f08.jpg28.9 KB · Views: 0 -
 a0bcdb2f38cec0d04ce210bdf27a8c55.jpg38.5 KB · Views: 0
a0bcdb2f38cec0d04ce210bdf27a8c55.jpg38.5 KB · Views: 0 -
 e773a480bc425bb6bdd794f2b625847f.jpg43.2 KB · Views: 0
e773a480bc425bb6bdd794f2b625847f.jpg43.2 KB · Views: 0 -
 bb60d64571caf1fe974257e3ca287fb1.jpg39.5 KB · Views: 0
bb60d64571caf1fe974257e3ca287fb1.jpg39.5 KB · Views: 0

