 Introduction Remcos v3.8.0 Cracked
Introduction Remcos v3.8.0 CrackedRemcos v3.8.0 Cracked is an unauthorized version of the legitimate Remote Access Trojan (RAT) . While the official Remcos tool is marketed for legitimate remote administration, cracked versions are widely abused by cybercriminals. These cracked variants often come with no authentication or licensing, making them easier for attackers to distribute and exploit.
Table of Contents
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
Cracked versions are especially dangerous because they may contain additional malware, backdoors, or trojanized code, making them far riskier than official copies. This article explains the features, threats, distribution methods, detection techniques, and mitigation strategies for Remcos v3.8.0 Cracked.
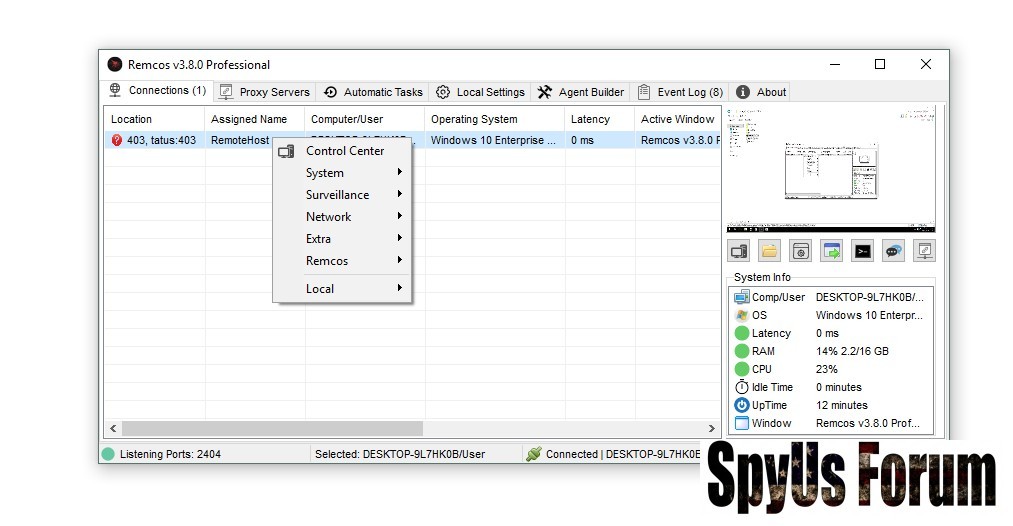
What is Remcos v3.8.0 Cracked?
Remcos Cracked is an illegal, pirated copy of the Remcos RAT. While it retains the full functionality of the legitimate version, cracked copies are more likely to be bundled with malicious payloads. Cybercriminals exploit these versions for:
- Full system access and control
- Credential theft and keylogging
- Data exfiltration
- Installing additional malware
Core Features of Remcos v3.8.0 Cracked
Although cracked, these versions often retain the features of official Remcos software:
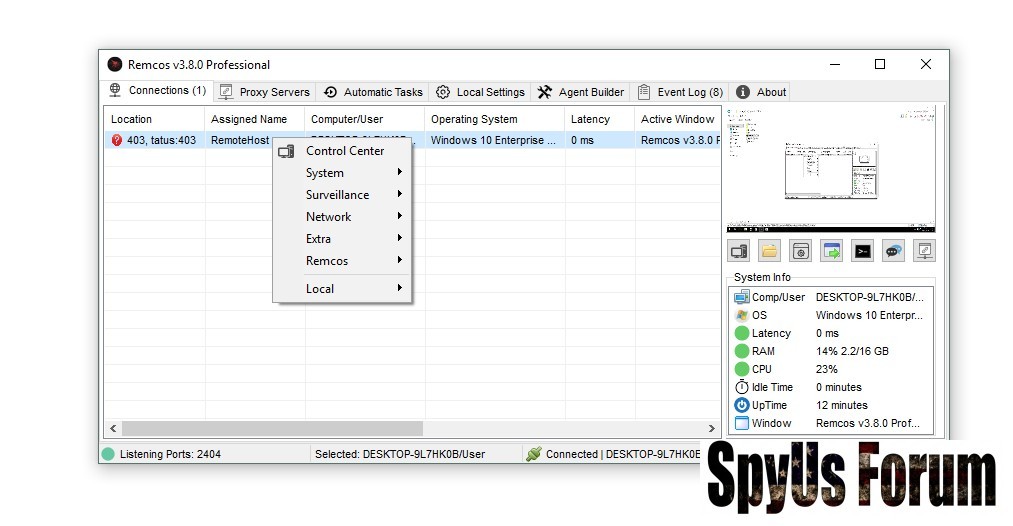
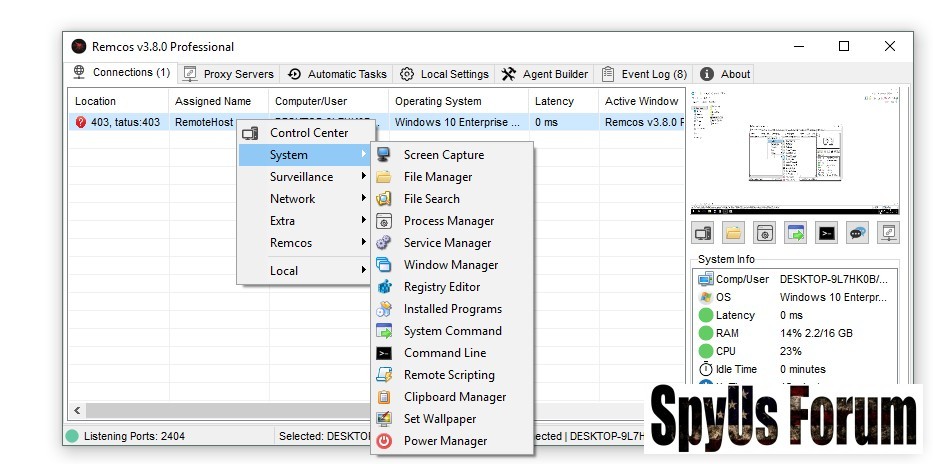
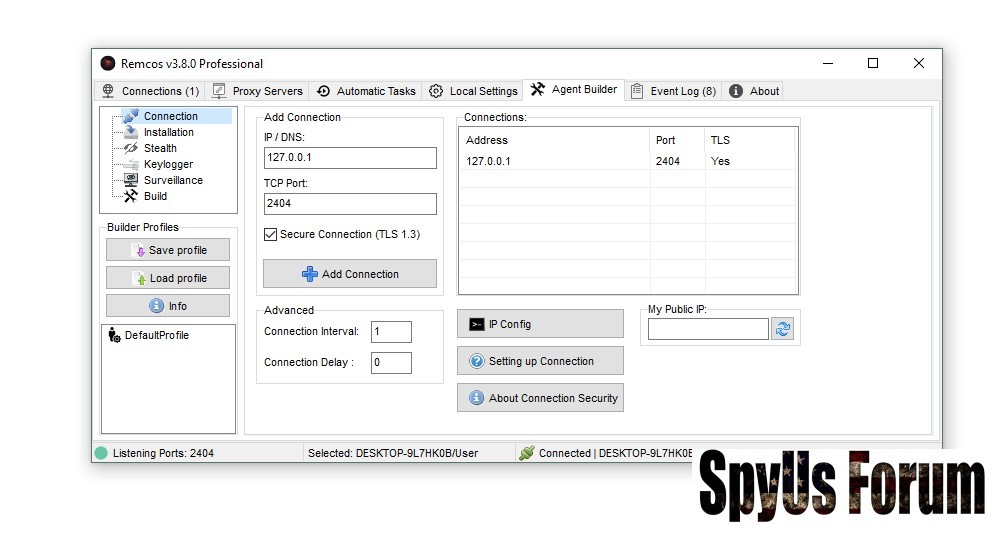
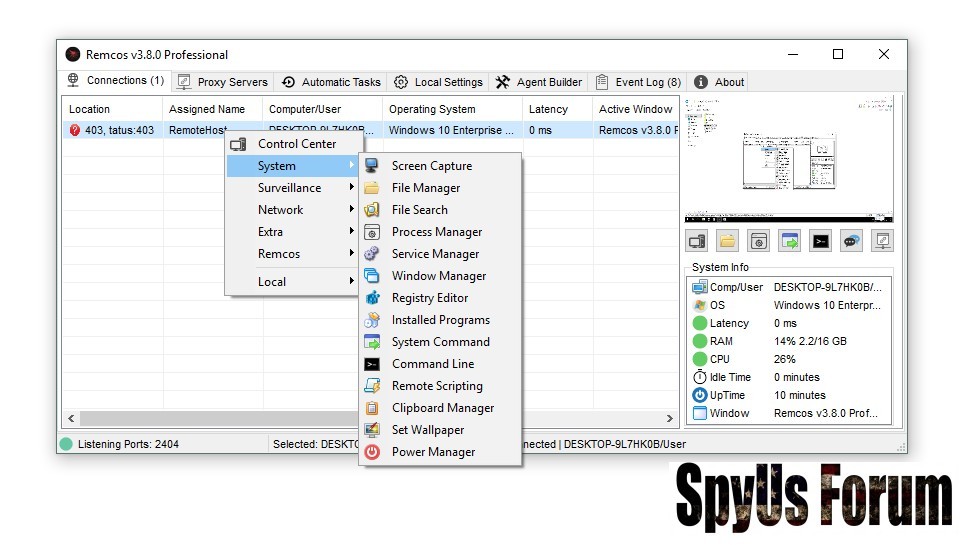
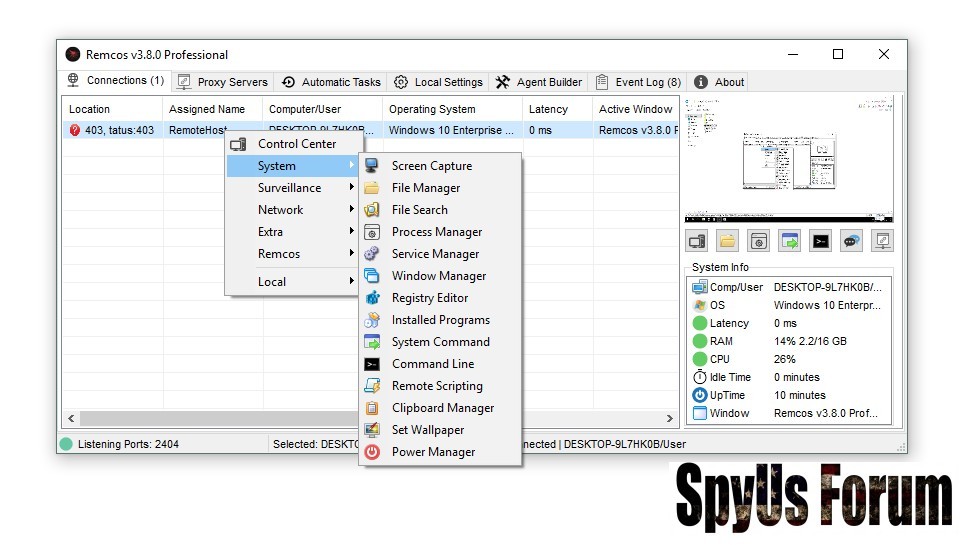
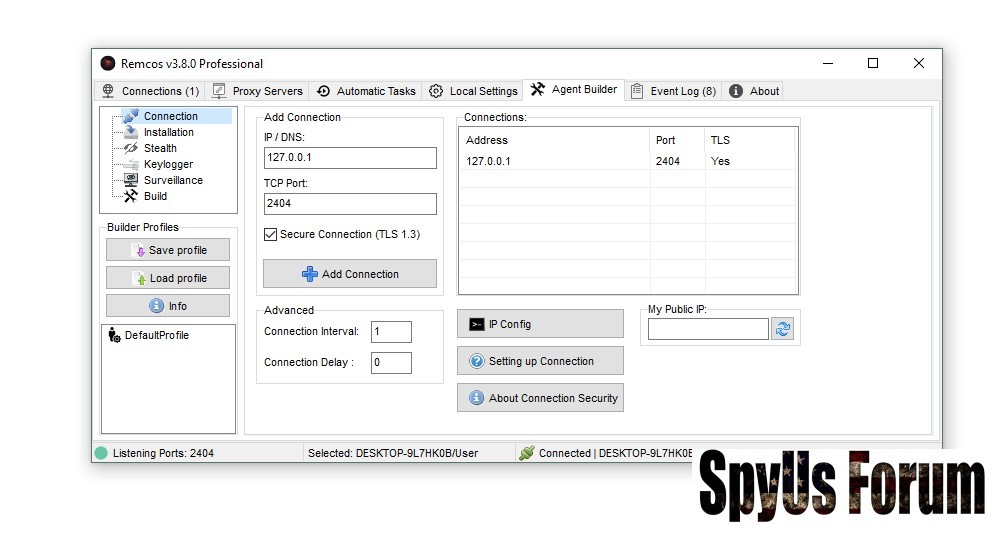
Remote Command and Control
 Feature: Allows attackers to execute commands on target machines remotely.
Feature: Allows attackers to execute commands on target machines remotely.Explanation: Cracked Remcos enables full remote administration, from running scripts to accessing system processes. In unauthorized hands, it becomes a tool for hijacking , stealing data, and controlling endpoints remotely.
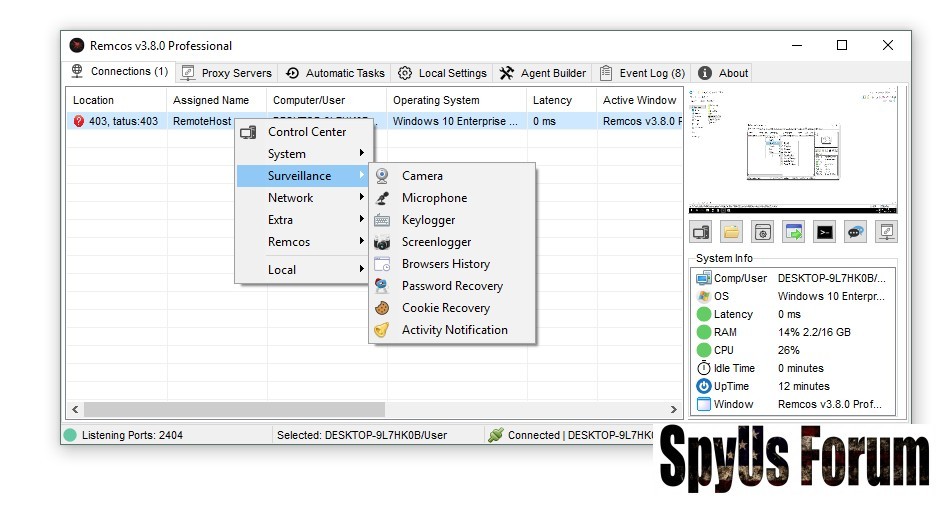
Surveillance and Keylogging
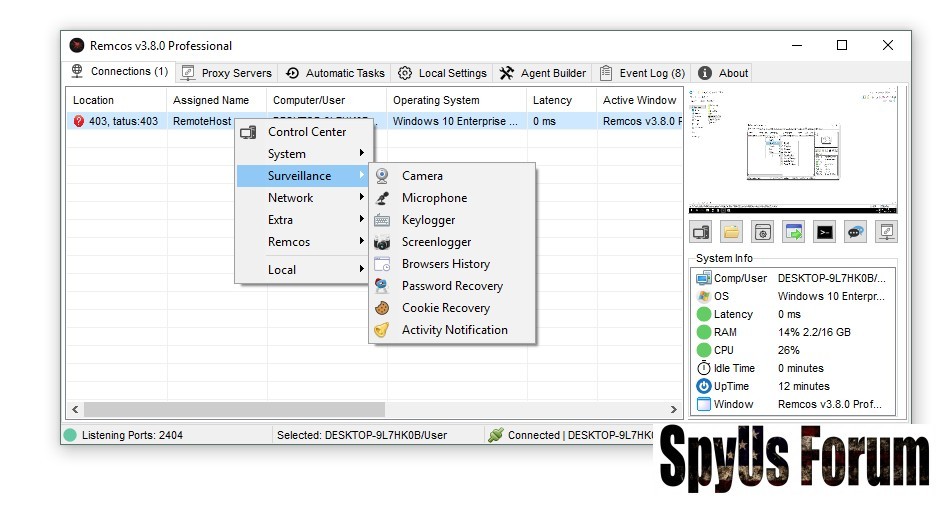 Feature: Captures keystrokes, screenshots, and webcam/microphone input.
Feature: Captures keystrokes, screenshots, and webcam/microphone input.Explanation: Attackers use this feature to monitor user activity, steal passwords, and spy on private communications. In cracked versions, additional malware may enhance spying capabilities.
File Management and Data Theft
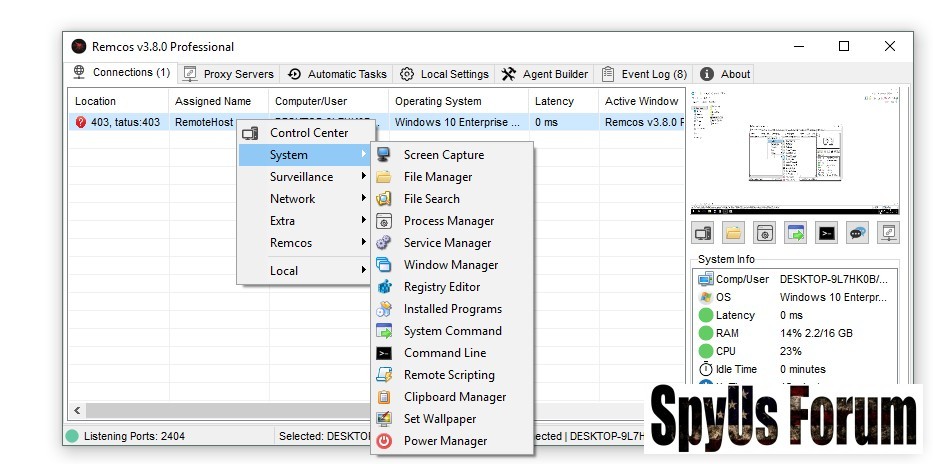 Feature: Upload, download, and modify files on the victim machine.
Feature: Upload, download, and modify files on the victim machine.Explanation: Cracked versions allow attackers to exfiltrate sensitive documents, certificates, and personal files. Unlike legitimate software, cracked copies often exfiltrate more aggressively or remain hidden on the system.
Persistence and pr!v!l3g3 3sc@l@t!0n
Feature: Remcos can maintain startup persistence and elevate privileges.
Explanation: Cracked variants often bypass security features, ensuring long-term presence and enabling attackers to retain access even after system reboots.
Stealth and Evasion
Feature: Conceals itself from and security tools.
Explanation: Cracked copies often include extra evasion mechanisms to avoid detection, such as process injection and in-memory execution. These features make detection harder and increase system compromise risk.
Distribution Methods
Cracked Remcos spreads through unauthorized channels and malicious tactics:
- Phishing Emails: Attachments disguised as cracks or keygens may install Remcos.
Explanation: Users are tricked into opening files that automatically execute the RAT. - Malicious Web Downloads: Fake “free Remcos v3.8.0 Cracked” sites host infected installers.
Explanation: Users downloading pirated software unknowingly expose their systems to malware. - Exploit and Loader Chains: Multi-stage attacks deploy cracked Remcos in memory without leaving traces.
Explanation: Advanced attackers use this to evade detection and quickly compromise systems. - Social Engineering: Fake CAPTCHAs or fake software activators trick users into enabling the malware.
Explanation: Exploits human error and curiosity to bypass security awareness.
Using Remcos v3.8.0 Cracked poses severe security risks:
- Credential theft and unauthorized account access
- Network compromise through lateral movement
- Data exfiltration and potential ransomware deployment
- Long-term espionage and backdoor persistence
Detection and Protection Strategies
Detecting cracked Remcos requires proactive security measures:
- Endpoint Monitoring: Track new processes, registry changes, and scheduled tasks.
Explanation: Behavior-based monitoring can identify suspicious activity even if antivirus fails. - Network Traffic Analysis: Look for unusual outbound connections or encrypted traffic.
Explanation: Cracked versions connect to attacker-controlled servers, which can be flagged by anomaly detection. - User Awareness: Train employees to avoid pirated software and suspicious downloads.
Explanation: Education prevents human-driven infection vectors. - Patch Management: Keep all systems updated to reduce exploit risk.
Explanation: Exploits used to deploy cracked are often patched in official updates. - Incident Response: Isolate infected devices, reset credentials, and perform forensic analysis.
Explanation: Quick response reduces damage and prevents lateral network spread.
Using cracked software is illegal and can expose users to:
- Civil lawsuits or criminal prosecution
- Malware infection and data theft
- Network compromise and liability
Best Practices
- Install trusted EDR solutions to monitor suspicious behavior.
- Educate users about risks of pirated software and phishing.
- Keep software and systems updated to prevent exploits.
- Monitor network traffic for unusual activity.
- Perform regular backups to mitigate data loss from malware.
Conclusion
Remcos v3.8.0 Cracked is a high-risk pirated version of a legitimate remote administration tool. Its features make it attractive for attackers, including remote control, keylogging, data theft, and persistence mechanisms. Cracked variants are far more dangerous than official versions, often bundling additional malware.
Organizations and individuals must avoid cracked software, implement layered security, train users, and proactively monitor endpoints to prevent compromise.
FAQs about Remcos v3.8.0 Cracked
Q1: Is using Remcos v3.8.0 Cracked legal?
A: No. Using cracked software is illegal and carries significant cybersecurity risks.
Q2: Can antivirus detect cracked Remcos?
A: Detection is difficult due to stealth features; behavioral monitoring and EDR are recommended.
Q3: How does Remcos v3.8.0 Cracked spread?
A: Through phishing, malicious downloads, exploit chains, and social engineering techniques.
Q4: Are cracked versions more dangerous than official versions?
A: Yes. Cracked versions often include additional malware and lack safety updates.
Q5: How can I protect my system?
A: Avoid pirated software, use endpoint protection, train users, update systems, and monitor network traffic.