 Phemedrone Stealer 2026 – Complete Malware Analysis, Features, Architecture & Cybersecurity Risks
Phemedrone Stealer 2026 – Complete Malware Analysis, Features, Architecture & Cybersecurity RisksIntroduction to Phemedrone Stealer 2026
In recent years, information-stealing malware (infostealers) has become one of the most common threats in the cybersecurity landscape. These malware families are specifically designed to extract valuable digital data from infected systems and transmit it to remote servers controlled by attackers.
Table of Contents
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
Phemedrone Stealer 2026 is one such advanced infostealer that has gained attention due to its lightweight architecture, memory-based data collection, and wide data-harvesting capabilities.
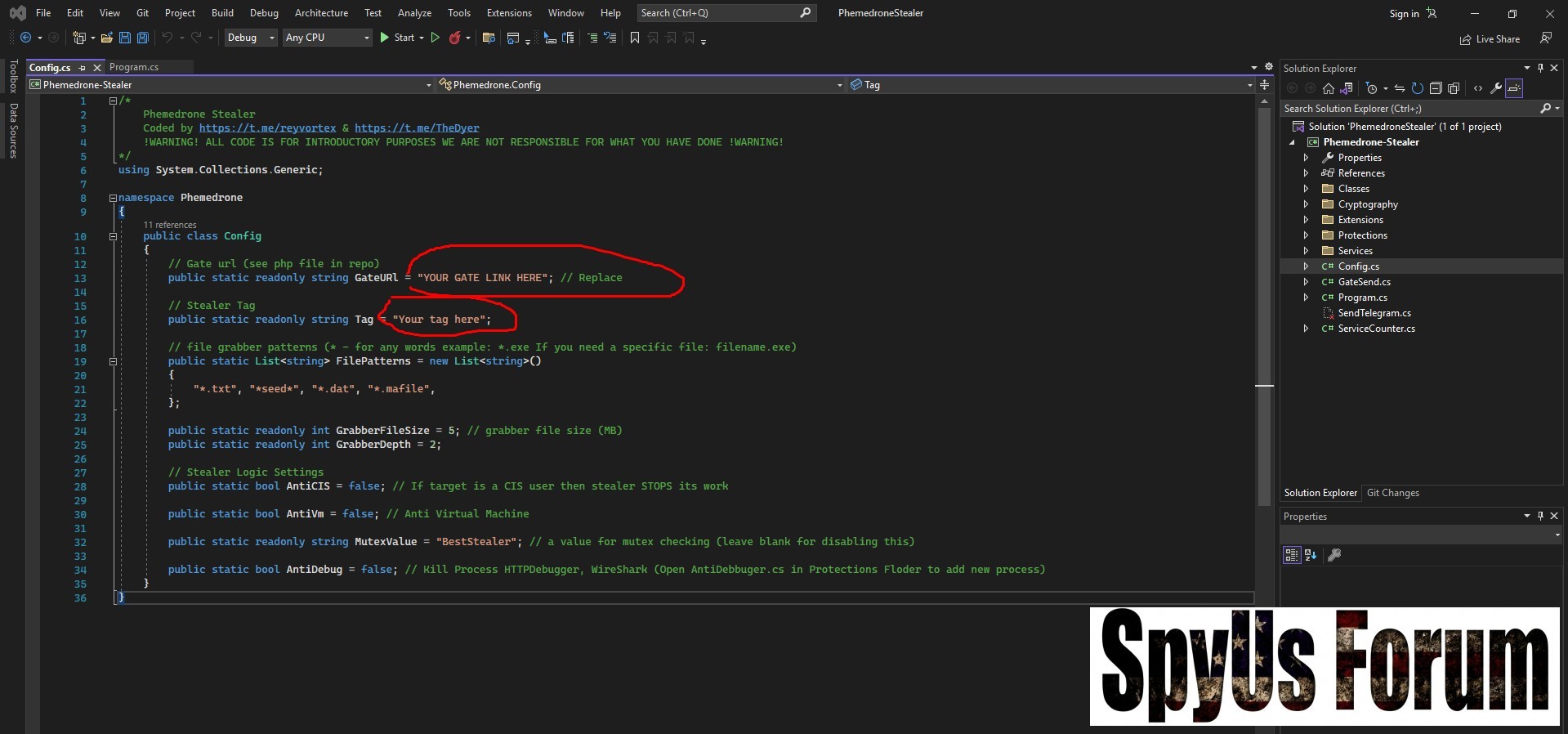
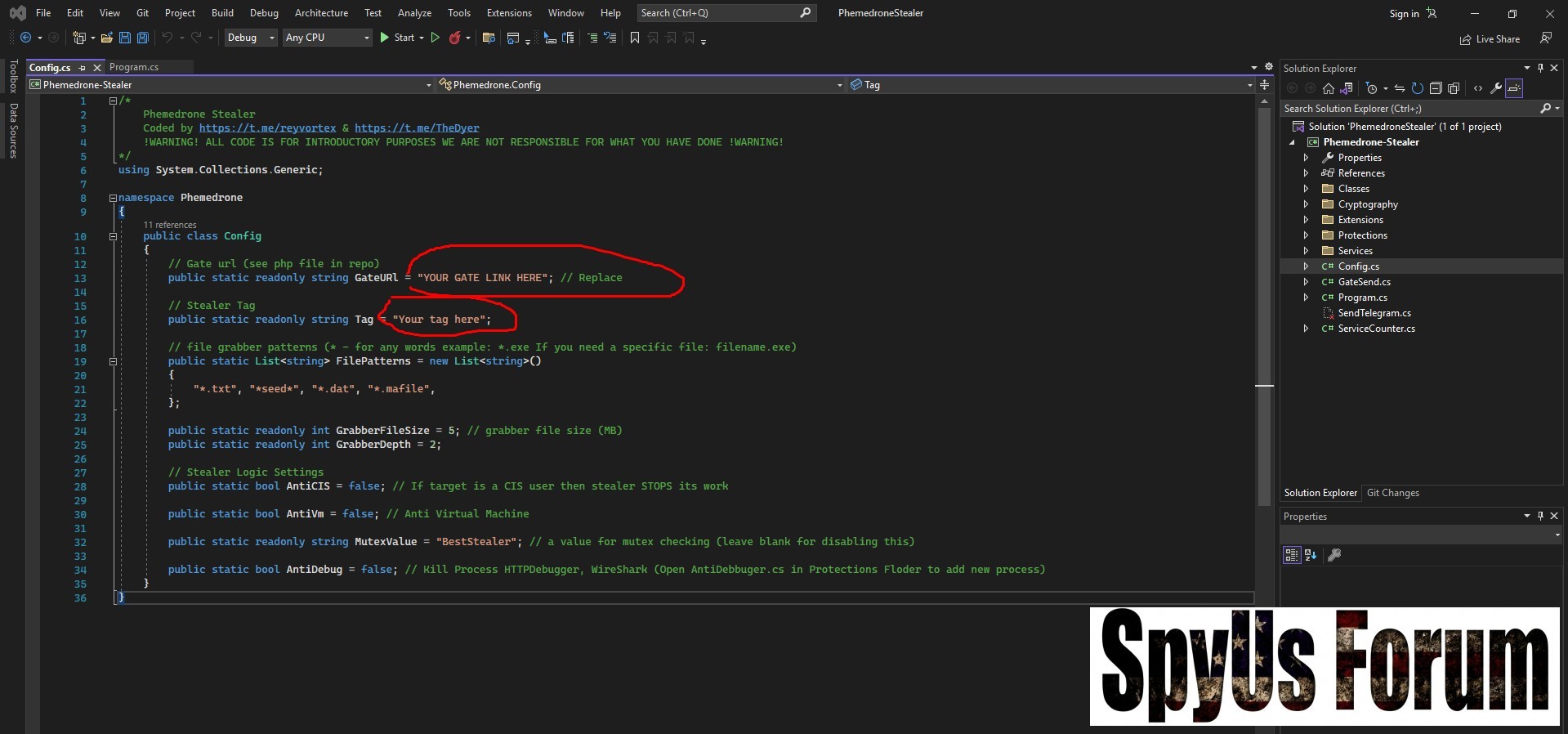
Developed in C#, this malware operates without external dependencies and uses an HTTP-based log system to send stolen information. Its design allows attackers to collect sensitive data such as:
• Browser credentials
• Cookies and session tokens
• Credit card data
• Messaging platform sessions
• Cryptocurrency wallet information
• Sensitive files stored on the system
Understanding how Phemedrone Stealer 2026 works is important for security researchers, malware analysts, and cybersecurity professionals who aim to detect, analyze, and prevent such threats.
Educational Disclaimer
This article is provided strictly for cybersecurity education, research, and awareness purposes.
The information discussed here helps analysts and defenders understand how infostealer malware operates so they can improve security defenses.
Any misuse of this information for illegal activities is not supported and remains the responsibility of the individual involved.
What is Phemedrone Stealer 2026?
Phemedrone Stealer 2026 is a data-harvesting malware designed to extract confidential information from Windows systems.
Unlike many malware families that require multiple libraries or external dependencies, this stealer is designed to be simple, compact, and efficient.
Key characteristics
Written entirely in C#
No external libraries required
Lightweight executable file
Data collection performed directly in memory
Logs transmitted through HTTP
These features allow the malware to remain compact and easier to deploy across different systems.
Architecture of Phemedrone Stealer
The malware operates using a two-component architecture.
Stealer Stub
The stealer stub is the executable component that runs on the infected machine.
 Responsibilities
Responsibilities• Collect sensitive information from the system
• Search browser directories
• Extract stored credentials
• Gather system files
• Send logs to the remote server
This component performs the primary data-harvesting operations.
Log Gate System
The second component is a standalone PHP log gate.
 Function of the Log Gate
Function of the Log GateReceives stolen data through HTTP requests
Stores collected information in structured logs
Allows operators to view collected data
Because the log gate is independent, it can be customized or modified easily.
Core Features of Phemedrone Stealer 2026
The stealer includes a range of capabilities designed to maximize data collection while maintaining stealth.
Lightweight Malware Design
One of the defining features of Phemedrone Stealer 2026 is its small footprint.
Design Advantages
Stub size approximately 80 KB
No external libraries required
Compatible with 32-bit and 64-bit Windows systems
Faster deployment and execution
This minimalistic design allows the malware to run efficiently on many systems.
Memory-Based Data Collection
Modern infostealers often rely on in-memory operations to avoid leaving traces.
How it works
Instead of writing data to temporary files, the malware:
• Collects sensitive information in system memory
• Processes the data internally
• Sends logs directly to the remote server
Benefits for attackers
Reduced forensic artifacts
Fewer disk traces
Improved stealth during execution
HTTP Data Transmission
After collecting information, the malware sends logs to a remote server.
Log Transmission Process
Data is packaged into a structured format
Sent through HTTP communication
Received by the PHP log gate
Stored on the remote host
This allows attackers to collect and organize large amounts of data from multiple systems.
Anti-Analysis and Evasion Techniques
To avoid detection by security researchers and analysis environments, the malware includes several evasion mechanisms.
Anti-analysis features
Anti-CIS protection
Anti-Virtual Machine detection
Anti-Debugger checks
Mutex protection
These techniques prevent the malware from running in environments commonly used for malware analysis or sandbox testing.
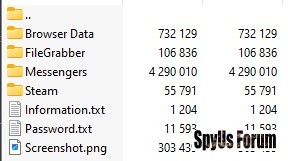
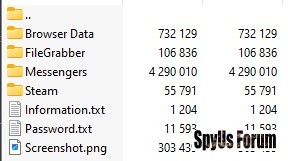
Configurable File Grabber
Another powerful component is the file grabbing module.
This feature allows operators to configure:
File extensions to target
Directory search depth
Specific folders to scan
Example targeted files
• Documents
• Configuration files
• Backup data
• Wallet backups
• Text files containing credentials
This allows attackers to collect valuable personal or corporate information.
Browser Data Extraction
store large amounts of sensitive information, making them prime targets for infostealers.
Chromium-Based Browser Targeting
Phemedrone Stealer searches for Chromium-based browsers installed on the system.
Examples include:
• Google Chrome
• Microsoft Edge
• Brave Browser
• Opera Browser
Extracted information
Cookies
Stored passwords
Autofill data
Stored credit cards
The malware uses dynamic path searching to locate browser profiles automatically.
Gecko-Based Browser Targeting
The malware also supports Gecko-based browsers.
Example
• Firefox-based browsers
Extracted data
Cookies
Login credentials
Autofill entries
This expands the malware’s ability to harvest data from different browser ecosystems.
Messaging Platform Session Theft
Another dangerous capability is session token extraction from popular platforms.
Targeted services
Why sessions are valuable
Session tokens allow attackers to:
• Access accounts without passwords
• Bypass login authentication
• Hijack active sessions
Cryptocurrency Wallet Targeting
Cryptocurrency wallets represent high-value targets for infostealers.
The malware scans systems for directories associated with known wallet applications and browser extensions.
Potential targets
Desktop crypto wallets
Browser wallet extensions
Authentication extensions
If successful, attackers may gain access to cryptocurrency assets or private keys.
Sensitive Browser Extension Harvesting
Modern browsers support extensions that store authentication data.
Phemedrone Stealer specifically searches for extensions containing sensitive information.
Examples of targeted extension types
• Cryptocurrency wallet extensions
• Authentication tools
• Security extensions
Such extensions may contain tokens, encrypted credentials, or session data.
Types of Data Collected by the Stealer
Phemedrone Stealer can harvest multiple categories of sensitive data.
Credentials
• Browser login credentials
• Saved passwords
• Autofill authentication data
Browser Data
• Cookies
• Session tokens
Financial Information
• Stored credit cards
• Cryptocurrency wallet data
Platform Sessions
Files
• Documents
• Configuration files
• Backup files
Security Risks and Potential Impact
Infostealers like Phemedrone Stealer 2026 pose significant cybersecurity risks.
Possible consequences
Identity theft
Financial fraud
Cryptocurrency loss
Account hijacking
Corporate data breaches
Because stolen data is sent silently to remote servers, victims often remain unaware until accounts or funds are compromised.
Prevention and Protection Strategies
Protecting systems from infostealers requires strong security practices.
Recommended protection methods
Use updated and endpoint security
Enable multi-factor authentication on accounts
Avoid downloading files from unknown sources
Keep operating systems and browsers updated
Monitor unusual network activity
Organizations should also deploy endpoint detection and response (EDR) systems to detect suspicious behavior.
Download Phemedrone Stealer 2026
Conclusion
Phemedrone Stealer 2026 demonstrates how modern infostealer malware has evolved to become more efficient, stealthy, and capable of harvesting large volumes of sensitive data.
With capabilities including:
• Browser credential extraction
• Messaging session theft
• Cryptocurrency wallet targeting
• File grabbing
• Anti-analysis protections
the malware highlights the importance of cybersecurity awareness and proactive defense strategies.
Studying such threats helps security professionals build stronger defenses against emerging cyber risks.
FAQ – Phemedrone Stealer 2026
What type of malware is Phemedrone Stealer 2026?
It is an information-stealing malware designed to collect sensitive data such as passwords, cookies, and cryptocurrency wallets.
Which programming language is used in Phemedrone Stealer?
The malware is written in C#, allowing it to run efficiently on Windows systems.
What data can Phemedrone Stealer steal?
It can collect:
• Browser passwords
• Cookies
• Credit cards
• Messaging sessions
• Cryptocurrency wallets
• Sensitive files
How does the malware send stolen data?
Collected information is sent to a remote server using HTTP communication through a PHP log gate.