 Medusa RAT 2026: Complete Malware Analysis, Features, and Security Risks
Medusa RAT 2026: Complete Malware Analysis, Features, and Security RisksIntroduction: Understanding Medusa RAT 2026
Medusa RAT 2026 is a next-generation Android Remote Access Trojan (RAT) that operates as a Malware-as-a-Service (MaaS) platform. It enables attackers to create customized malicious applications, distribute them efficiently, and remotely control infected devices.
Table of Contents
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
Unlike traditional malware, this system provides a complete ecosystem that simplifies cyberattacks, making it accessible even to low-skilled threat actors.
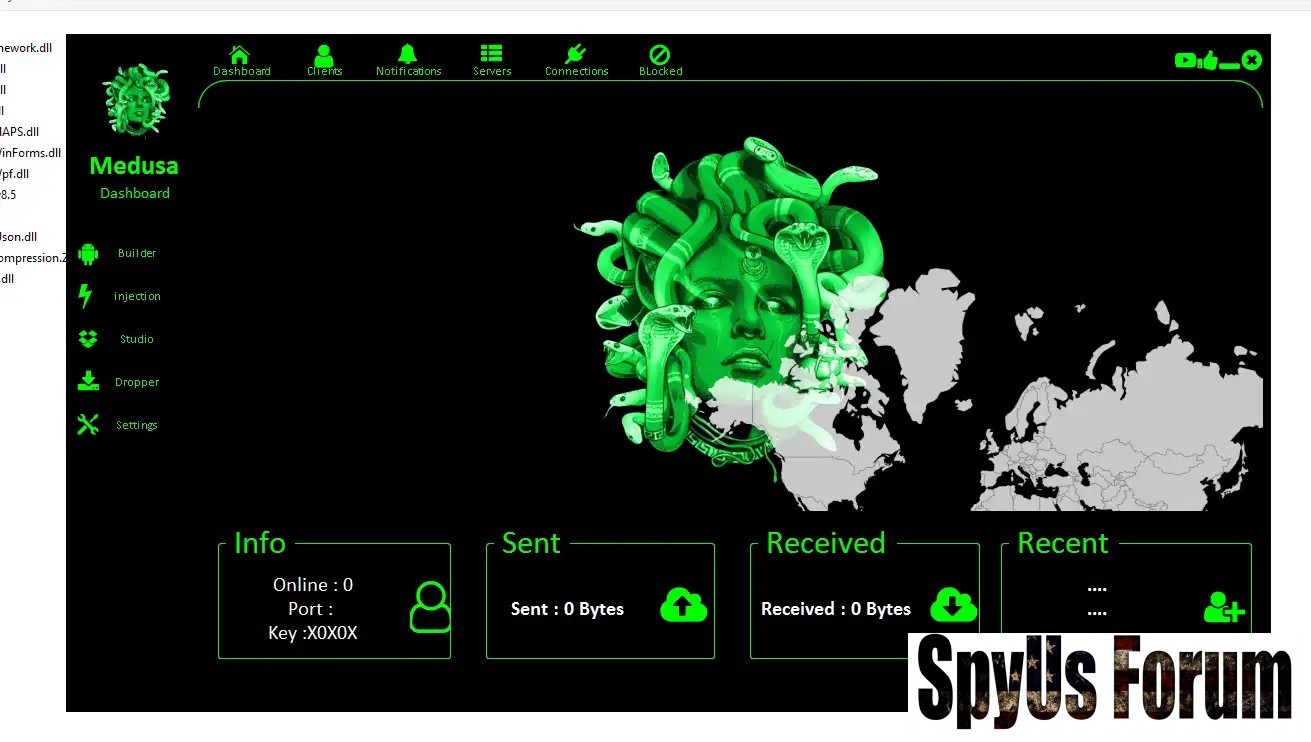
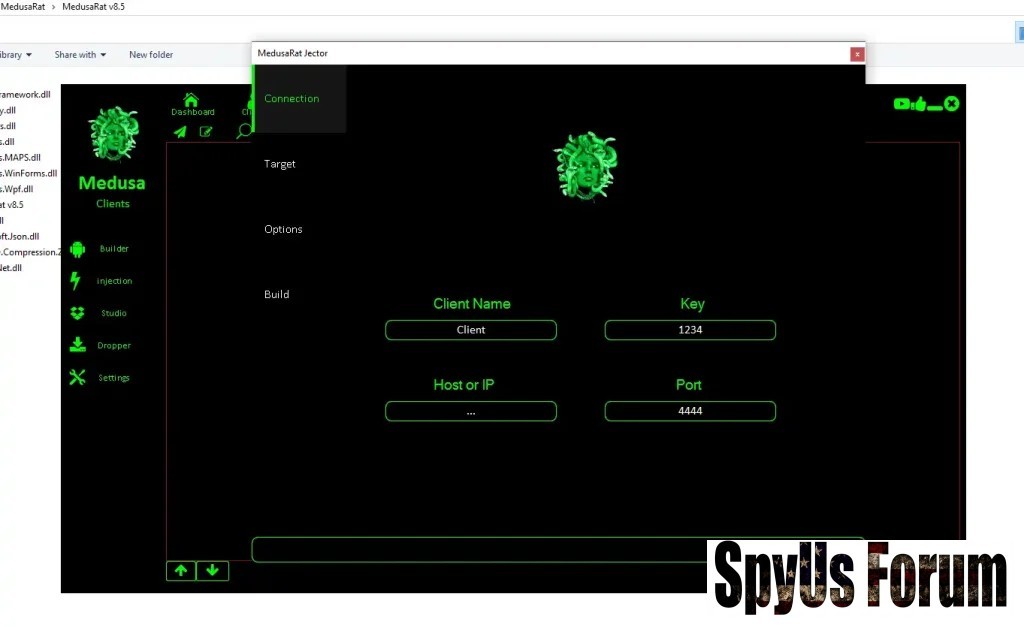
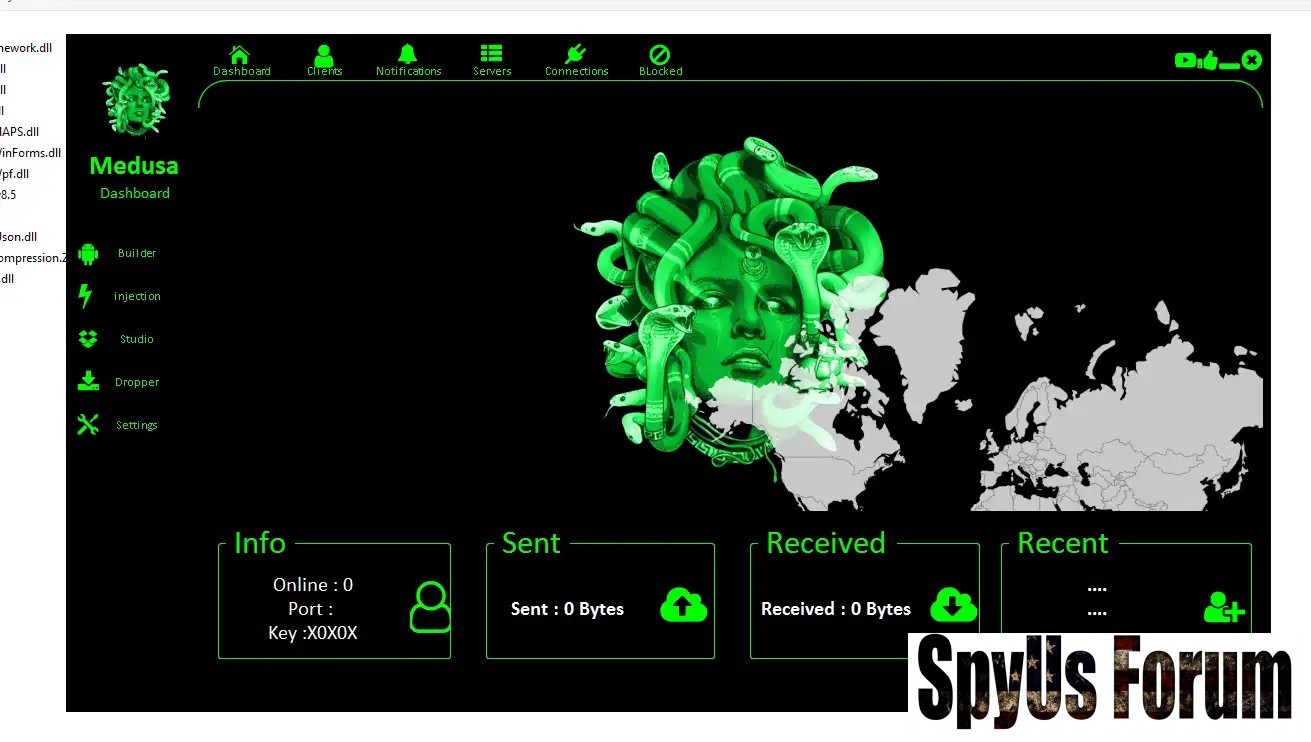
Core Architecture of Medusa RAT 2026
The platform is built with multiple integrated modules that streamline malware creation and deployment.
Builder Engine
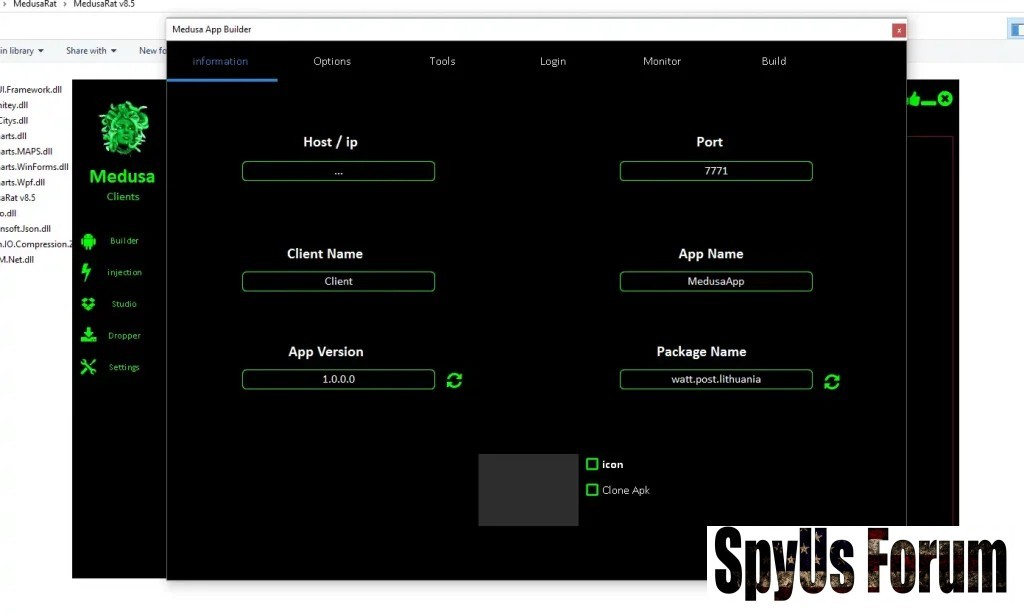
- APK Compilation System:
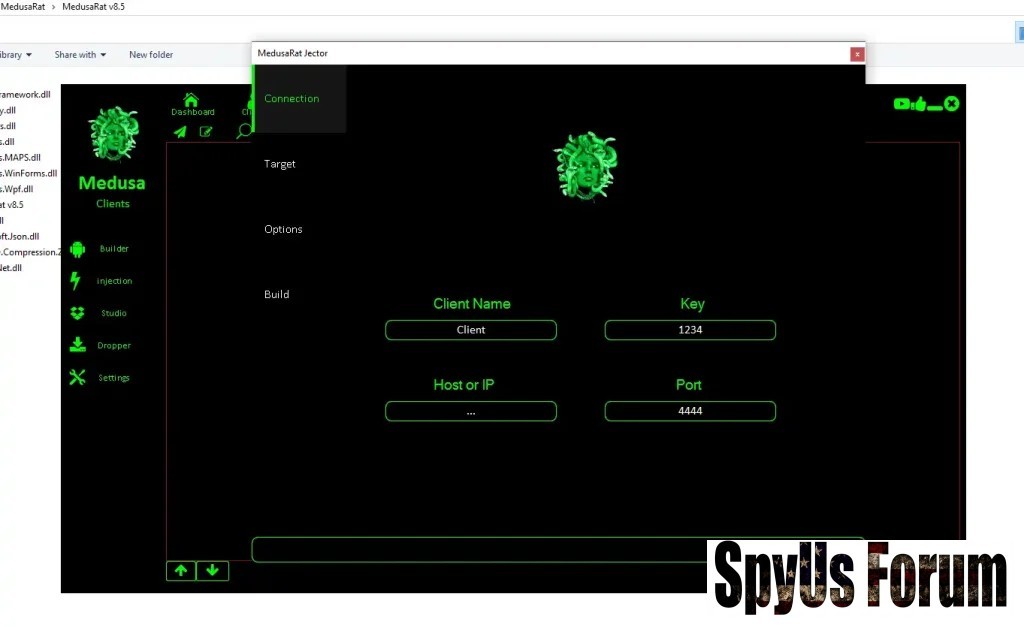
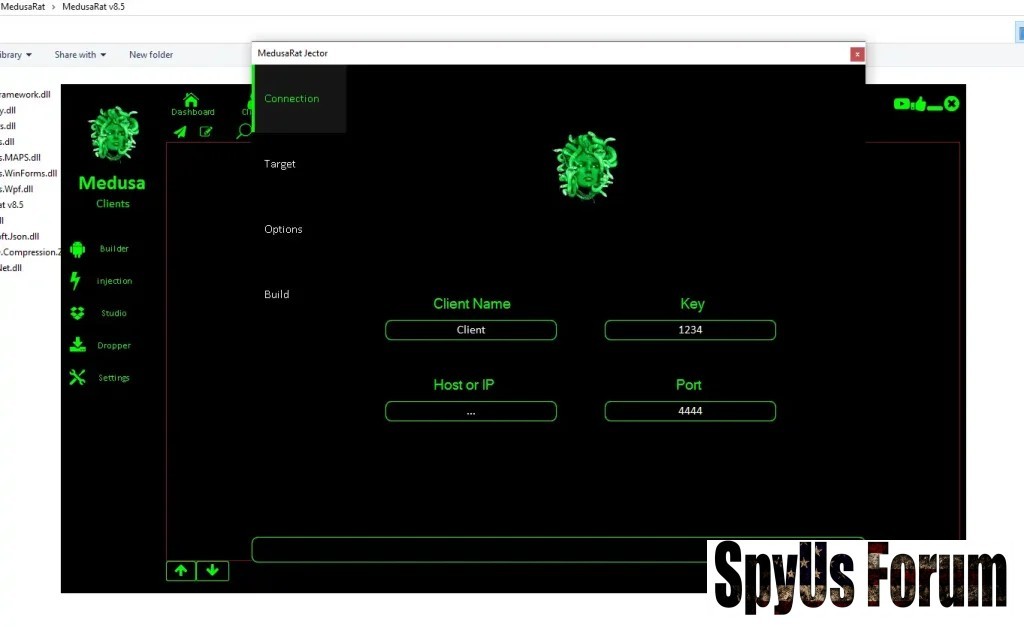
The builder converts raw malicious code into a fully functional Android APK file. Attackers can define behavior such as background execution, startup persistence, and communication protocols. This makes the malware adaptable for different attack scenarios. - C2 Server Configuration:
The system allows attackers to specify command-and-control (C2) server details, including IP address and port. This connection acts as a communication bridge, enabling real-time data exfiltration and remote commands.
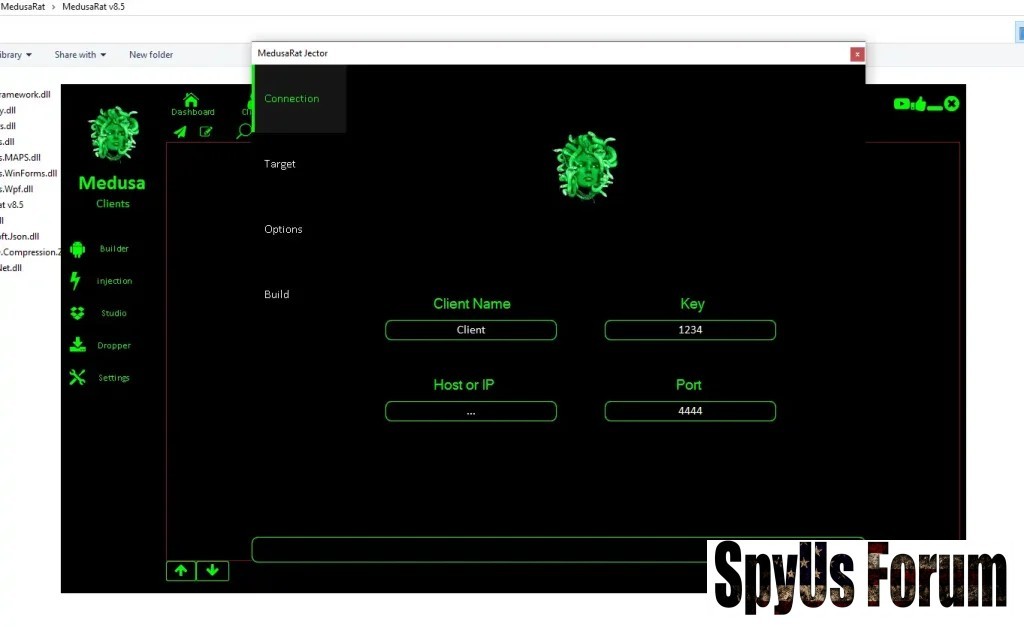
- c0d3 !nj3ct!0n into Legitimate Apps:
Attackers embed malicious payloads into trusted applications like banking or messaging apps. This significantly increases the chances of successful installation because users are less likely to suspect modified apps. - Security Bypass Techniques:
By injecting code into already trusted apps, the malware bypasses many traditional security filters and app verification systems, making detection more difficult.

- APK Decompilation & Editing:
This feature allows attackers to reverse-engineer existing apps, analyze their structure, and modify their behavior. It opens the door for deep customization of malicious payloads. - Re-signing and Repackaging:
After modification, apps are recompiled and digitally signed, making them appear legitimate and installable on Android devices without raising warnings.

- Lightweight Initial Payload:
The dropper APK is a small application designed to avoid detection during installation. It does not contain the full malicious code initially. - Dynamic Payload Download:
Once installed, the dropper connects to a remote server to download the complete malware. This approach helps evade static analysis tools and improves stealth.
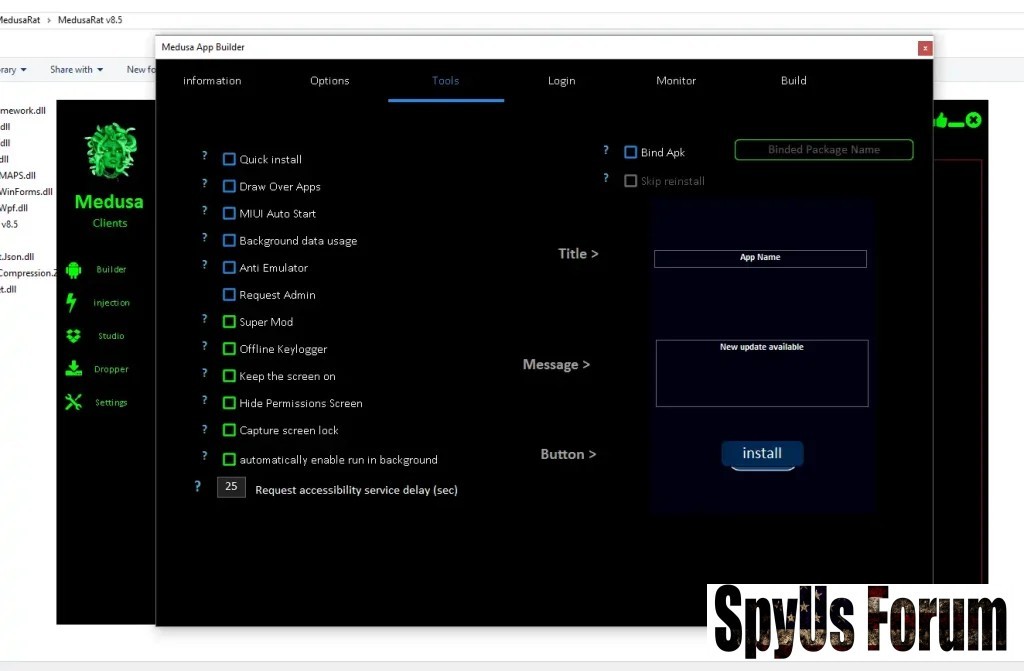
- Behavior Customization:
Attackers can configure how the malware behaves, including persistence techniques, data collection frequency, and communication intervals. - Permission Management:
The system allows fine control over requested permissions, enabling attackers to request only what is necessary to avoid suspicion.
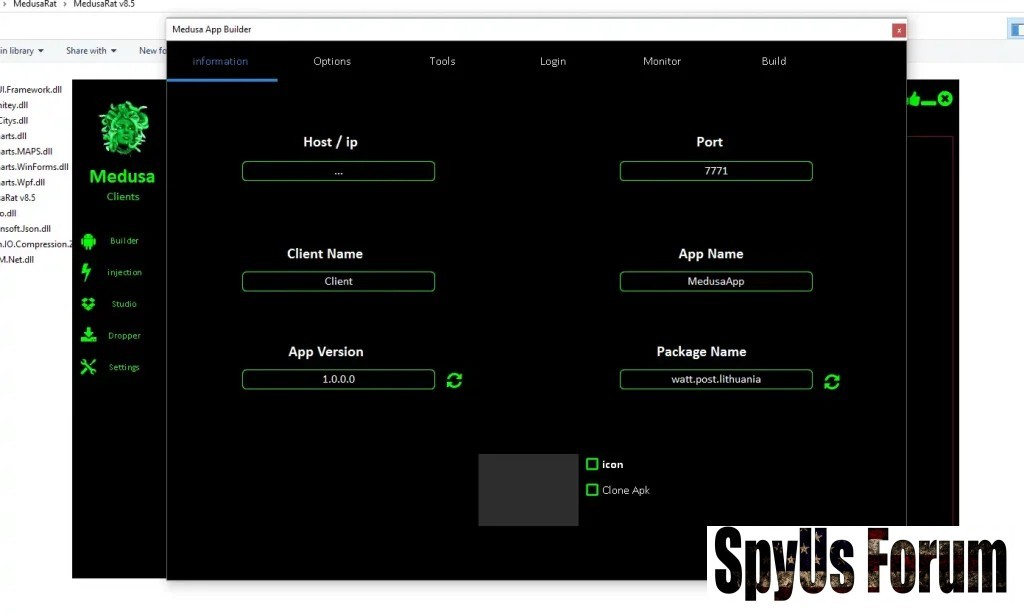
App Identity sp00f!ng
- Fake App Branding:
Attackers can assign misleading app names such as “System Update” or “Security Tool.” This increases trust and encourages installation. - Custom Icons & Package IDs:
Visual elements and identifiers are modified to closely resemble legitimate applications, making detection by users extremely difficult.
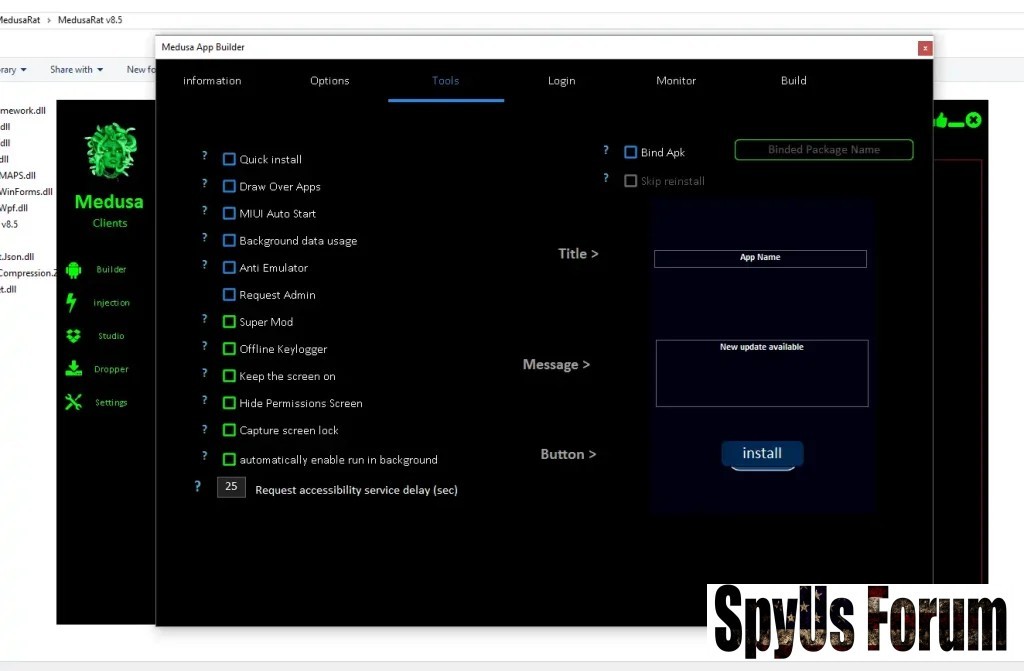
- Anti-Emulator Protection:
The malware detects whether it is running in a virtual or sandbox environment. If detected, it stops execution to avoid analysis by security researchers. - Background Stealth Execution:
It runs silently without user awareness, consuming minimal system resources to avoid suspicion.
- Continuous Data Capture:
The keylogger records every keystroke even when the device is offline. This ensures no data is lost during network interruptions. - Delayed Data Synchronization:
Once internet connectivity is restored, all collected data is automatically transmitted to the attacker’s server.
Persistence & pr!v!l3g3 3sc@l@t!0n

- Device Administrator Access:
The malware requests elevated privileges, making it extremely difficult to uninstall. It can block removal attempts and maintain long-term control. - Auto-Start Functionality:
It automatically launches on device reboot, ensuring continuous operation without user interaction.
- Suppressed Permission Prompts:
The malware can bypass or hide Android permission dialogs, allowing it to access sensitive data without explicit user consent. - Unauthorized Data Access:
This includes access to SMS messages, contacts, storage, and other personal data, significantly increasing privacy risks.
- Fake Login Interfaces:
The malware overlays fake login screens on top of legitimate apps, tricking users into entering sensitive credentials. - Credential & OTP Theft:
It captures banking details, login credentials, and two-factor authentication codes in real time.

- Microphone Monitoring:
The malware can remotely activate the microphone to record conversations or ambient sounds, effectively turning the device into a surveillance tool. - Screen Capture & Recording:
It continuously captures screenshots or records screen activity, allowing attackers to monitor user behavior and sensitive transactions. - Call Recording:
Incoming and outgoing calls are recorded and uploaded, providing attackers with access to private communications. - Automated Interaction Tools:
Features like auto-clickers simulate user actions, helping bypass biometric or manual authentication systems.
- File System Access:
Attackers can browse, download, upload, or delete files from the device, giving them full control over stored data. - SMS & Contact Extraction:
The malware collects SMS messages (including OTPs) and entire contact lists, which can be used for further phishing attacks. - Remote Command Execution:
A built-in shell allows attackers to execute system-level commands, enabling deep control over the device. - Device Manipulation:
Features include remote locking, clipboard hijacking (useful for cryptocurrency theft), and forced redirection to malicious websites.
CategoryCapabilityRisk Level
PersistenceAdmin access, auto-start Critical
EvasionHidden permissions, injection Critical
Data TheftKeylogger, SMS, contacts High
SurveillanceMic, screen, calls High
ControlRemote shell, overlays Severe
Why Medusa RAT 2026 Is a Global Cyber Threat
Medusa RAT 2026 represents a major shift in cybercrime:
- Lower technical barrier for attackers
- Scalable malware deployment
- Advanced evasion and persistence
- High-value data targeting (banking, credentials)
How to Protect Your Device from Medusa RAT 2026
- Avoid Unknown APKs:
Only install apps from official stores like Google Play to reduce risk exposure. - Disable Unknown Sources:
Prevent unauthorized app installations from third-party sources. - Keep Updated:
Regular updates patch security vulnerabilities that malware exploits. - Use Mobile Security Tools:
Install reputable solutions that detect behavioral threats. - Monitor Permissions:
Regularly review app permissions and revoke unnecessary access.
Conclusion
Medusa RAT 2026 is a highly sophisticated malware framework that combines ease of use with powerful attack capabilities. Its modular design, stealth features, and deep system access make it one of the most dangerous mobile threats in 2026.
Proactive security measures, awareness, and cautious app installation habits remain the best defense against such evolving cyber threats.
Frequently Asked Questions (FAQs)
What is Medusa RAT 2026 used for?
Medusa RAT 2026 is used by cybercriminals to remotely control Android devices, steal sensitive data, and monitor user activity without consent.
How does Medusa RAT infect devices?
It typically spreads through malicious APK files, phishing links, or repackaged legitimate apps downloaded from third-party sources.
Can Medusa RAT bypass Android security?
Yes, it uses advanced techniques such as permission hiding, c0d3 !nj3ct!0n, and anti-emulator detection to bypass security systems.
Is Medusa RAT detectable by antivirus software?
Advanced mobile security tools can detect it, especially those using behavioral analysis, but basic antivirus apps may fail to identify it.
How can I remove Medusa RAT from my phone?
Removing it may require revoking admin privileges, uninstalling suspicious apps, or performing a factory reset in severe cases.
Attachments
-
 1d3f393f9745a4473b6fe9959ea13182.jpg66.8 KB · Views: 0
1d3f393f9745a4473b6fe9959ea13182.jpg66.8 KB · Views: 0 -
 d4e7028f309d6a6643ab786ef0015591.jpg64.2 KB · Views: 0
d4e7028f309d6a6643ab786ef0015591.jpg64.2 KB · Views: 0 -
 ead63c527a7e1418682582aaa5944149.jpg69.9 KB · Views: 0
ead63c527a7e1418682582aaa5944149.jpg69.9 KB · Views: 0 -
 758d52b3a0c26ae06fdfb7a026440ca0.jpg63.8 KB · Views: 0
758d52b3a0c26ae06fdfb7a026440ca0.jpg63.8 KB · Views: 0 -
 f2de9643413a81eeaf4e177d7f0db652.jpg79.2 KB · Views: 0
f2de9643413a81eeaf4e177d7f0db652.jpg79.2 KB · Views: 0 -
 fafdc6d62c1d2d6dfe959aac88ad3533.jpg61 KB · Views: 0
fafdc6d62c1d2d6dfe959aac88ad3533.jpg61 KB · Views: 0 -
 1ed66593d13816d04071127102d959a9.jpg66 KB · Views: 0
1ed66593d13816d04071127102d959a9.jpg66 KB · Views: 0 -
 4d2209adb50c892cbd03e7f3bd6de2aa.jpg64.2 KB · Views: 0
4d2209adb50c892cbd03e7f3bd6de2aa.jpg64.2 KB · Views: 0 -
 d0792df129bfe8a36d79bcf0fbc6c256.jpg145 KB · Views: 0
d0792df129bfe8a36d79bcf0fbc6c256.jpg145 KB · Views: 0

