 G-700 RAT V6.1.5 – A Dangerous Android Malware Explained
G-700 RAT V6.1.5 – A Dangerous Android Malware ExplainedIn today’s digital era, cyber threats are no longer limited to computers. Smartphones have become a primary target, and tools like G-700 RAT V6.1.5 are proof of how advanced and accessible malware has become.
Table of Contents
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
Although promoted as a “remote administration tool,” this software is actually a powerful Remote Access Trojan (RAT) designed to secretly control Android devices. It allows attackers to monitor, steal data, and manipulate devices without the user’s knowledge.
What is G-700 RAT V6.1.5?
G-700 RAT V6.1.5 is a malicious Android-based spying tool that gives full remote control of a device to an attacker.
 Key Purpose:
Key Purpose:- Spy on mobile activity
- Steal sensitive data
- Access camera & microphone
- Intercept banking information
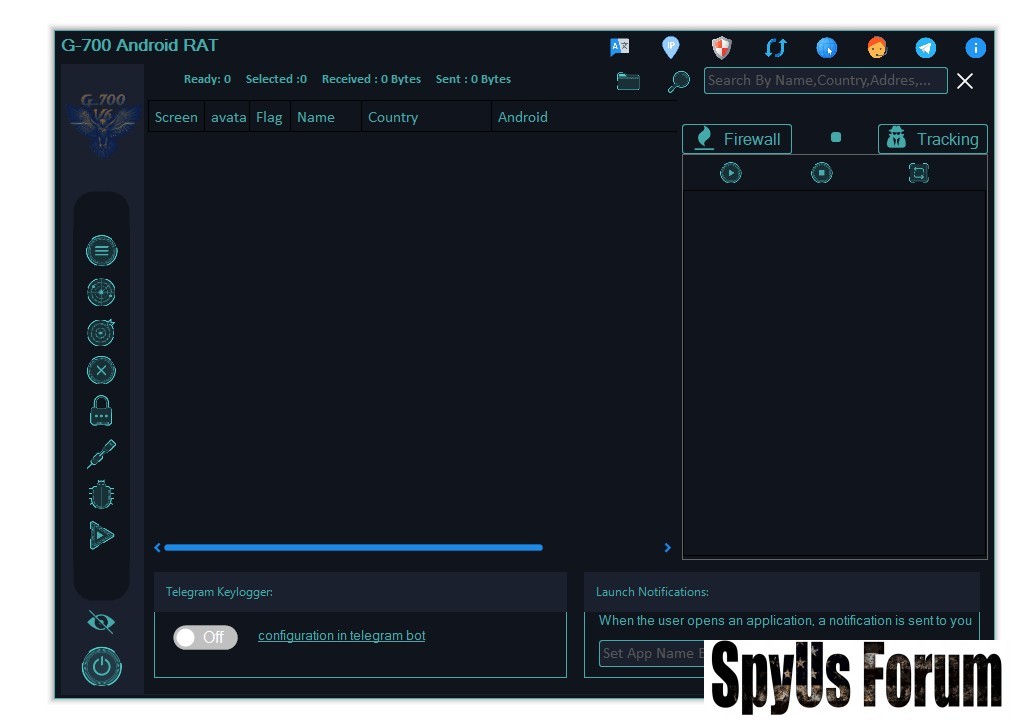
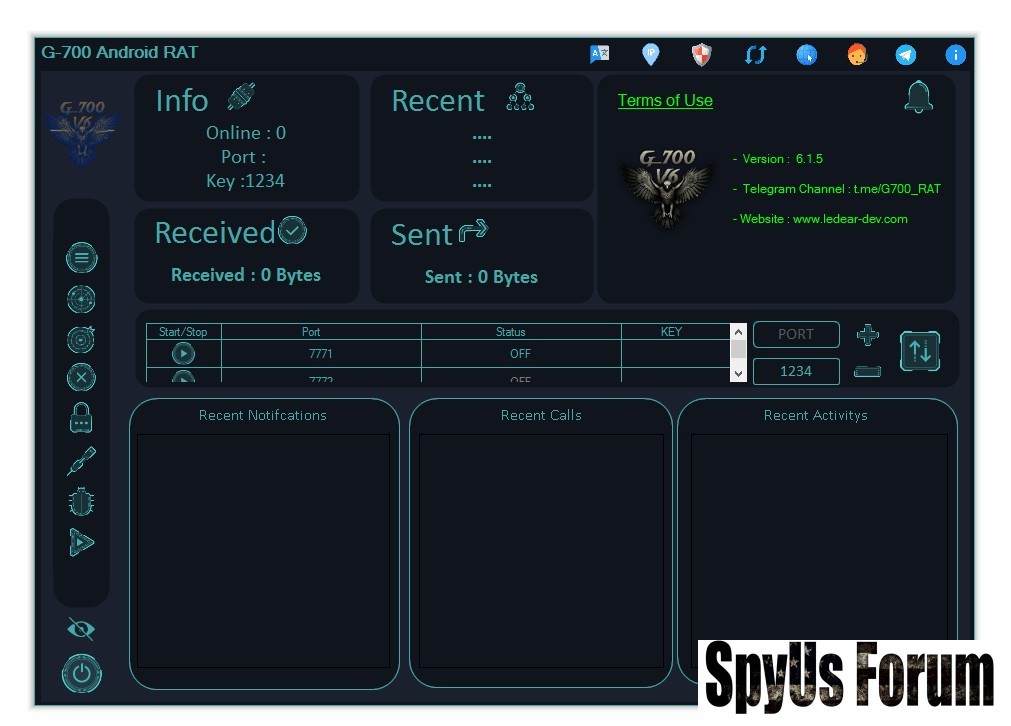
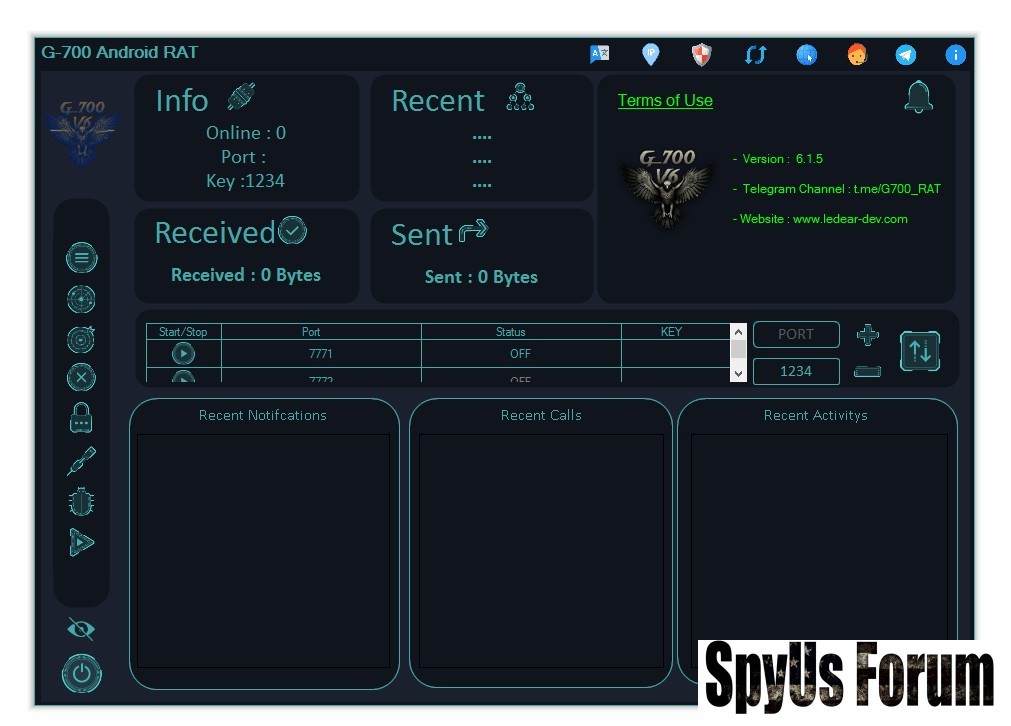
G-700 RAT V6.1.5 Control Panel Overview
The control panel acts as the main dashboard where attackers manage infected devices.
 Dashboard Features:
Dashboard Features:- Connection Status: Shows online devices and server port
- Access Key: Ensures only the attacker can control devices
- Data Transfer: Tracks sent and received data
- Victim List: Displays device name, country, and Android version
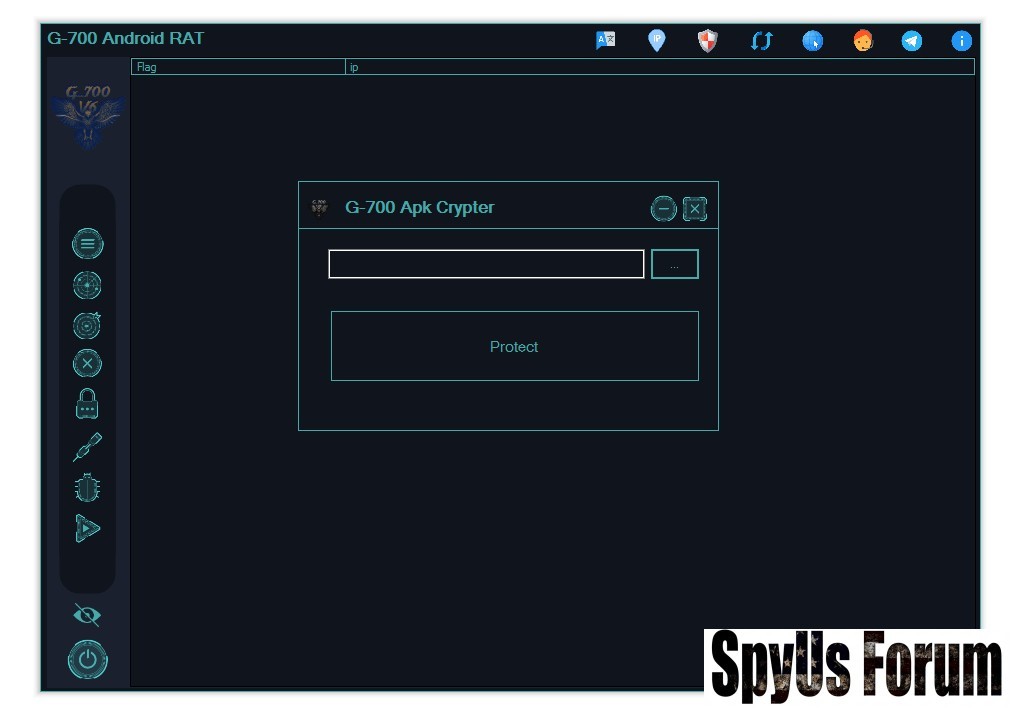
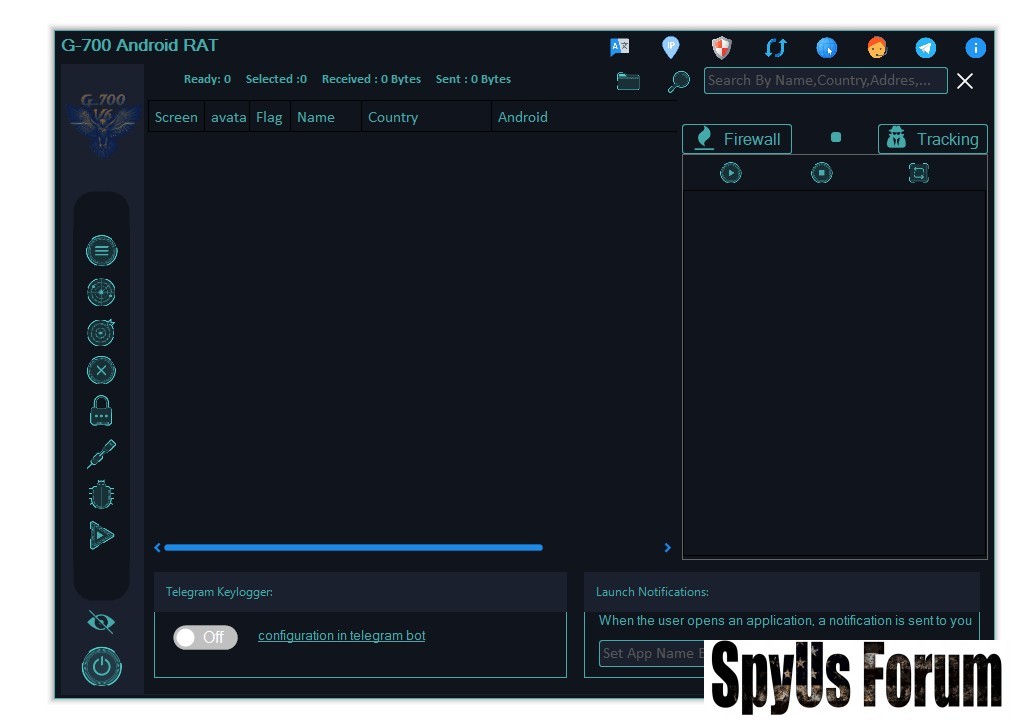
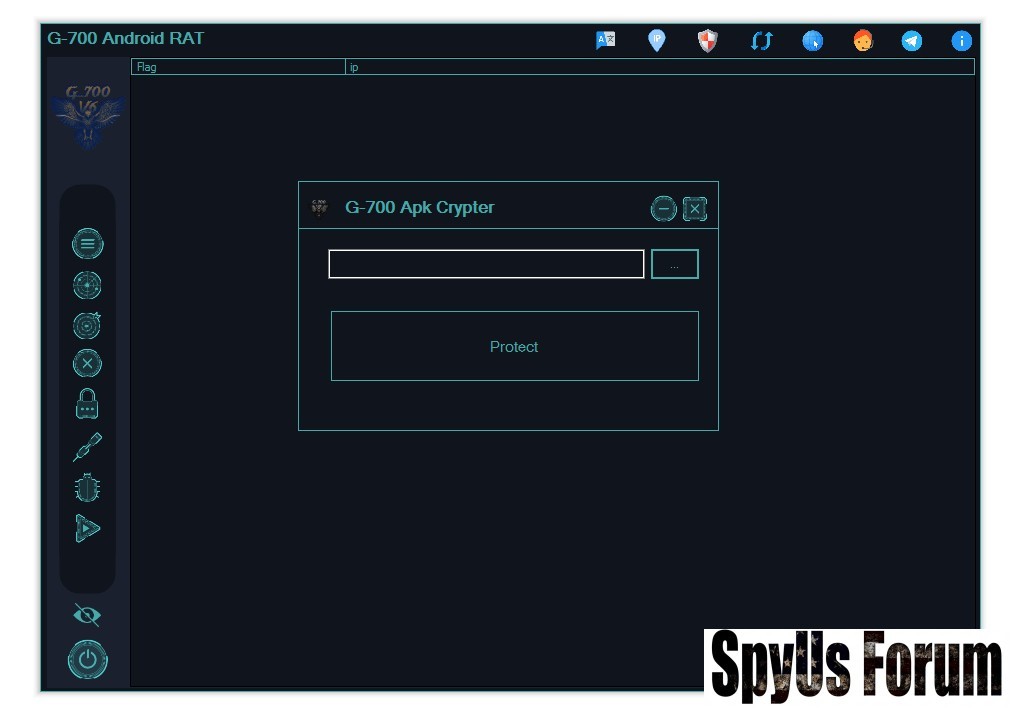
APK Builder & cr¥pt3r – Malware Creation Tools
One of the most dangerous aspects of G-700 RAT is its ability to create customized malware apps.
APK cr¥pt3r (Evasion Tool)
The cr¥pt3r helps malware avoid detection by antivirus software.
 Functions:
Functions:- Changes malware signature
- Bypasses security detection
- Makes malware harder to identify
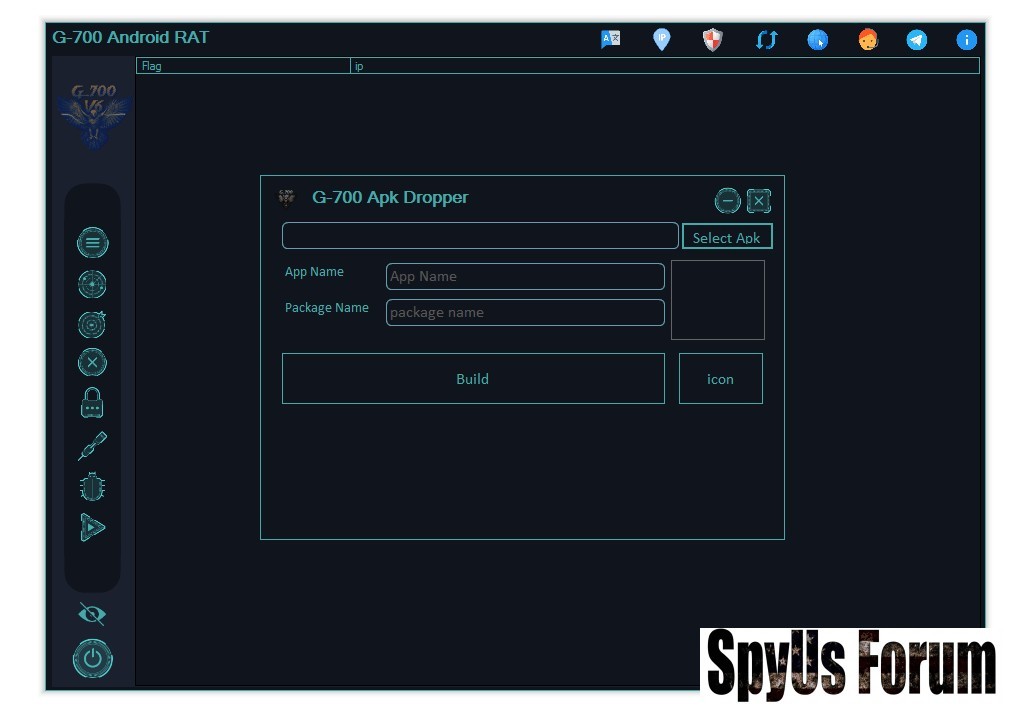
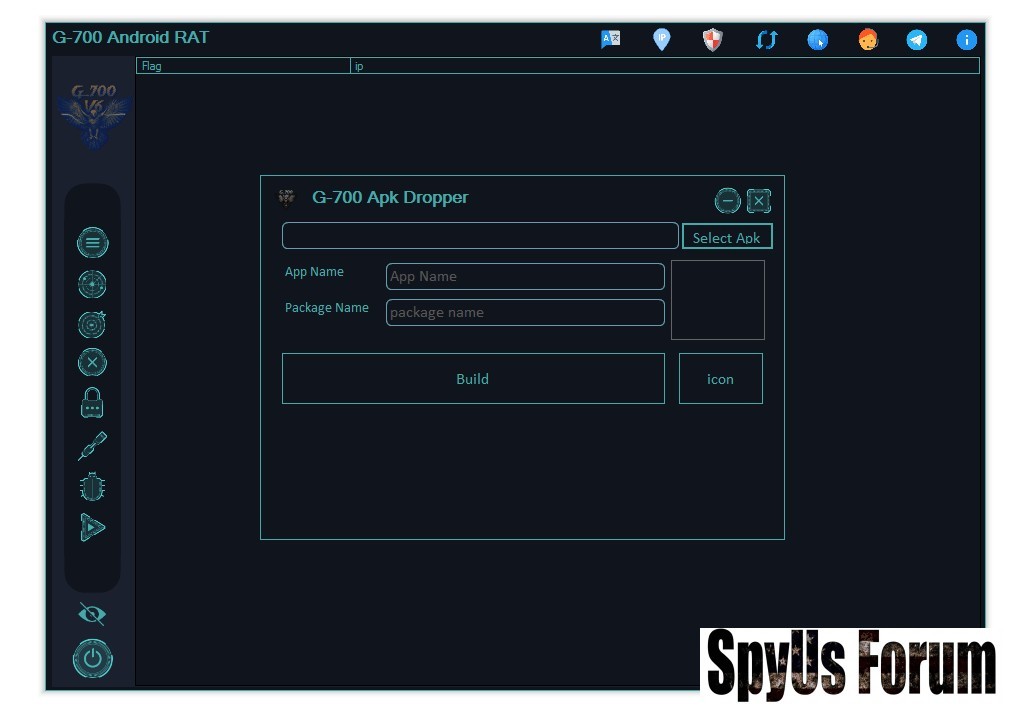
APK Dropper (Disguise Tool)
The Dropper is used to trick users into installing malware.
 Features:
Features:- Fake app names (e.g., system apps)
- Real-looking icons
- Creates installable APK files
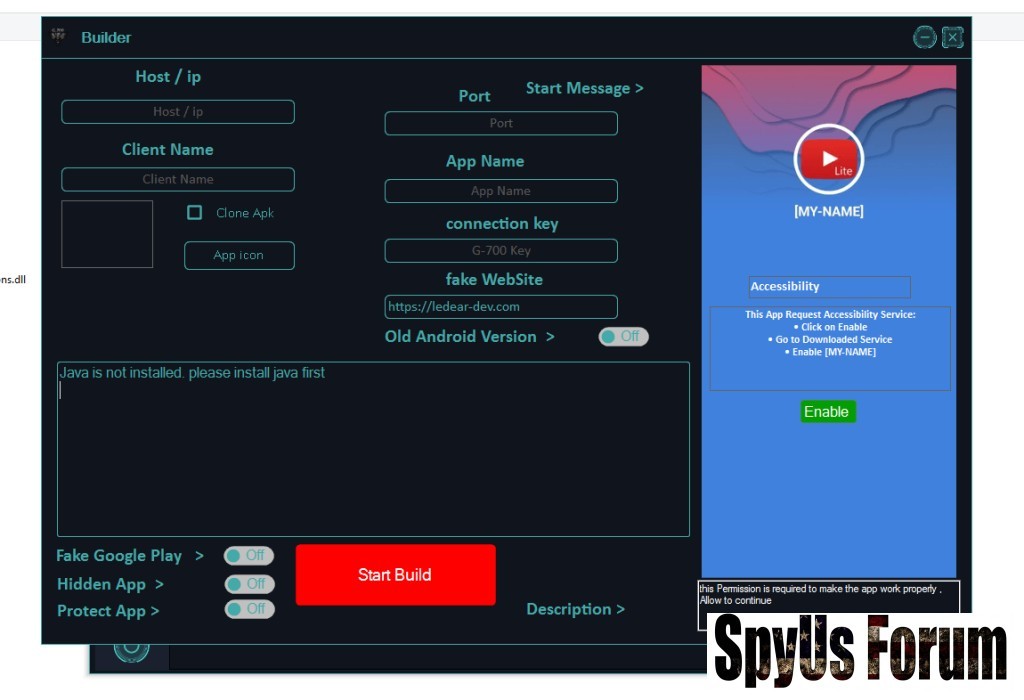
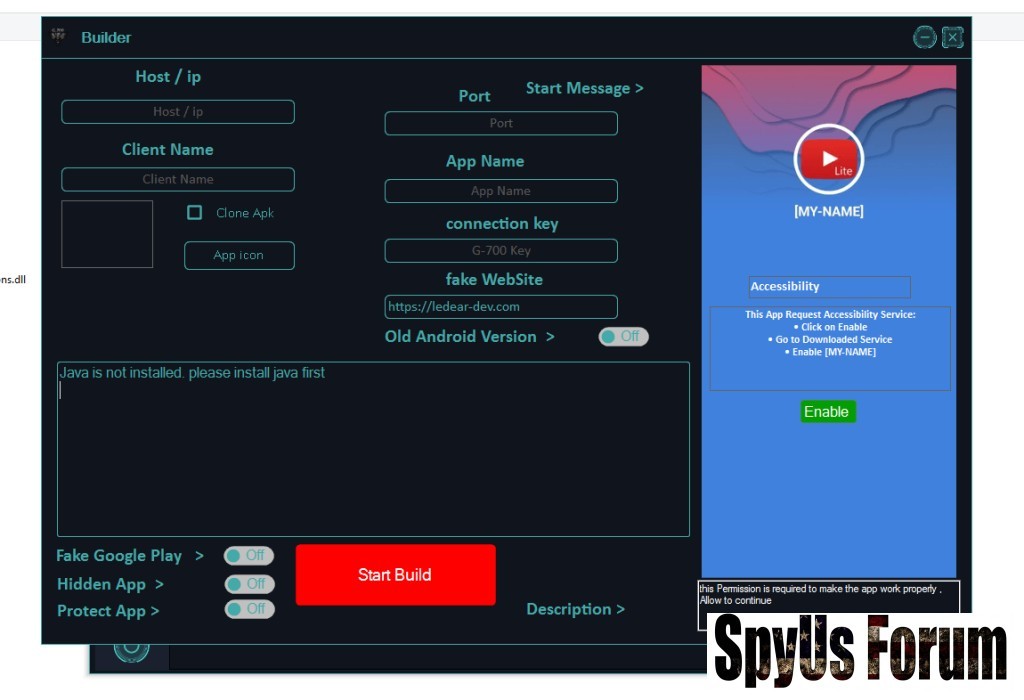
Builder Configuration
Attackers can fully customize how the malware behaves.
Options Include:
- Host/IP & Port connection
- Unique connection key
- Fake website redirection
- Custom start message
Advanced Features of G-700 RAT
Accessibility Exploit (Full Device Control)
This is the most dangerous feature.
What it does:
- Reads screen content
- Performs automatic clicks
- Grants permissions secretly
- Accesses banking apps
Telegram Keylogger
G-700 RAT uses Telegram bots to send stolen data.
Captured Data:
- Keystrokes (passwords)
- Screenshots
- Clipboard data
- OTP & 2FA codes
Real-Time App Monitoring
Attackers get alerts when specific apps are opened.
Example:
- Banking apps
- Crypto wallets
Hidden & Persistent Operation
The malware is designed to stay undetected.
Features:
- Fake system app identity
- Hidden icon after install
- Anti-uninstall protection
How G-700 RAT Spreads
This malware mainly relies on social engineering.
Common Methods:
- Cracked or modded apps
- Fake download links
- Phishing messages
- Third-party installations
Risks & Damage to Victims
If a device is infected, the consequences can be severe.
Major Risks:
- Financial theft
- Identity theft
- Contact data misuse
- Privacy invasion
How to Protect Yourself
Follow these essential steps to stay safe:
Security Tips:
- Disable unknown app installations
- Check Accessibility settings regularly
- Avoid suspicious APK files
- Watch battery drain & overheating
- Keep security features enabled
Download G-700 RAT V6.1.5
Conclusion
G-700 RAT V6.1.5 represents a new level of cyber threat where powerful hacking tools are easily accessible. Its combination of stealth, control, and simplicity makes it extremely dangerous.
With features like keylogging, remote control, and real-time monitoring, this malware can completely compromise a smartphone. Users must remain cautious, avoid untrusted apps, and always monitor app permissions.
Staying informed is the first step toward staying safe.
FAQs (Frequently Asked Questions)
What is G-700 RAT V6.1.5 used for?
It is used to remotely control Android devices, steal data, and monitor user activity without permission.
Is G-700 RAT dangerous?
Yes, it is highly dangerous as it can access personal data, banking information, and even control your device.
How does G-700 RAT infect phones?
It spreads through fake apps, phishing links, and downloads from untrusted sources.
Can G-700 RAT steal bank details?
Yes, it can intercept OTPs, passwords, and monitor banking apps.
How can I remove G-700 RAT?
You should uninstall suspicious apps, disable accessibility permissions, and use trusted security tools.