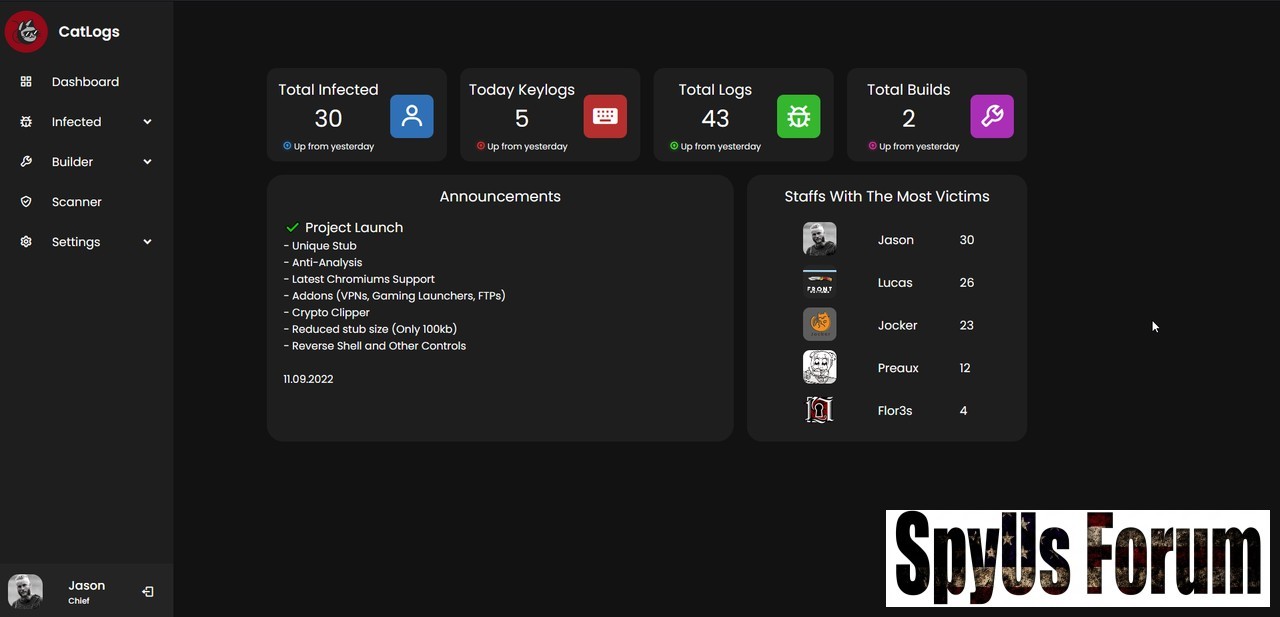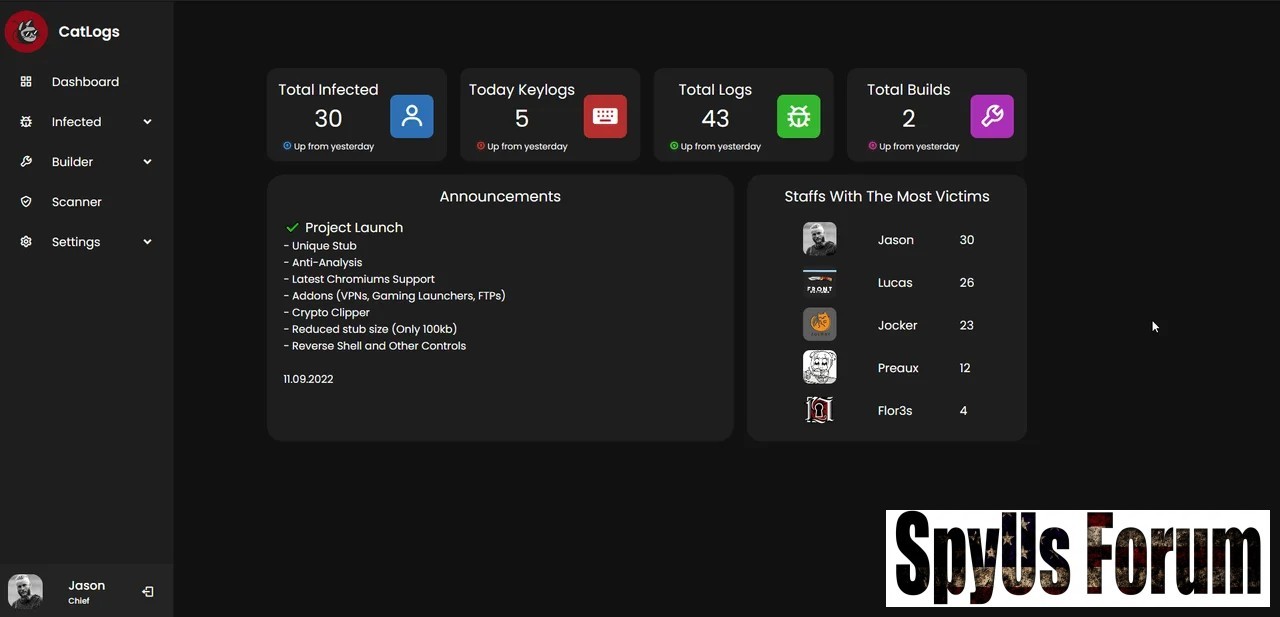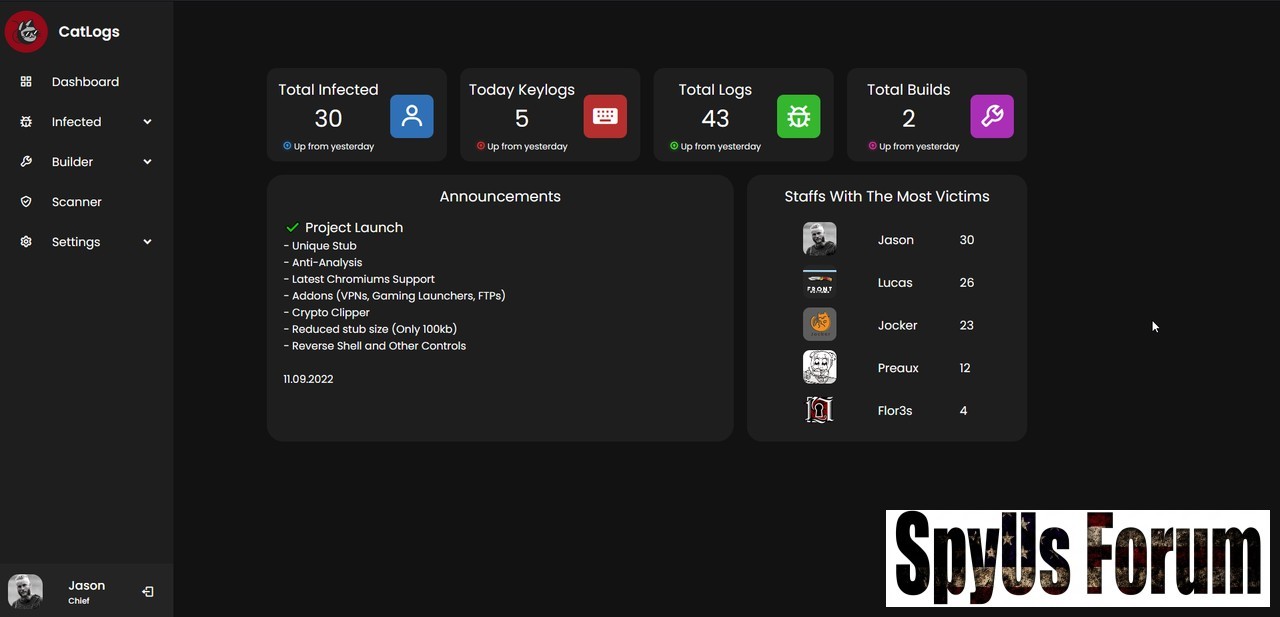
CatLogs Advanced HTTP Based Stealer 2024
The ever-evolving landscape of cybersecurity continues to challenge individuals, businesses, and organizations worldwide. As technology advances, so do the tactics employed by malicious actors seeking to compromise data, privacy, and network security. One such threat that has garnered attention in recent years is CatLogs, an HTTP-based virus that poses a significant danger to online users. In this article, we will delve into the world of CatLogs, exploring its origins, modus operandi, and steps for prevention and mitigation.
Understanding CatLogs Advanced HTTP Based Stealer 2024
CatLogs is a relatively new class of malware that leverages the Hypertext Transfer Protocol (HTTP) to propagate and execute malicious code on a victim’s device. While HTTP is a standard protocol for transmitting data over the internet, CatLogs exploits its weaknesses to infiltrate systems, compromise user data, and often serve as a gateway for further cyberattacks. The name “CatLogs” is derived from its ability to stealthily log user activity while remaining hidden, much like a cat stalking its prey.
Modus Operandi
Infection: CatLogs Advanced HTTP Based Stealer 2024 typically infects a user’s device through deceptive methods, such as phishing emails, malicious downloads, or compromised websites. Once a user unknowingly interacts with the infected content, the malware gains entry into the system.
Communication with Command and Control (C2) Servers: CatLogs Advanced HTTP Based Stealer 2024 establishes a connection with remote C2 servers using HTTP requests. These servers serve as the central control point for the malware’s operators, allowing them to send commands and exfiltrate sensitive data.
Information Gathering: Once inside the victim’s system, CatLogs begins its nefarious activities. It collects a wide range of information, including keystrokes, login credentials, personal data, and browsing history, all while remaining hidden from the user’s view.
Data Exfiltration: CatLogs Advanced HTTP Based Stealer 2024 regularly sends the stolen data to the C2 servers via HTTP requests, encrypting it to evade detection by security measures.
Additional Payload Delivery: In some cases, CatLogs may serve as a delivery mechanism for other malware or ransomware, further compromising the victim’s system.
Requirements:
You must be registered for see links
(Run ‘npm i’ on CatLogs folder to get all the required Nodes Libraries)
You must be registered for see links
Features:
Browser Logins and Cookies Stealer
Ransomware (Encrypt/Decrypt with Custom Key)
RAT (Shell/System Commands)
Clipper (BTC/ETH)
System Informations
Keylogger
Anti-Analysis (Sandboxie, Virtual Machines, HoneyPots)
VPNs, Gaming Launchers, VOIP, Clients Recovery
91kb Payload Stub
Easy to Setup and Launch
Can be used with any CashCrypter that supports .NET (4.6) Payloads
Turn off any kind of AVs in the hosting system to prevent issues
You must be registered for see links
You must be registered for see links
Download Links:
Download Link 1:
You must be registered for see links
Download Link 2:
You must be registered for see links
Download Link 3:
You must be registered for see links
Download Link 4:
You must be registered for see links