Introduction to Bawless RAT 2026 Cracked
Introduction to Bawless RAT 2026 CrackedBawless RAT 2026 Cracked is a Remote Access Trojan (RAT) modified to bypass licensing restrictions. It provides unauthorized access to premium features, allowing attackers to remotely control systems, log keystrokes, steal passwords, and deploy ransomware.
Table of Contents
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
Semantic LSI Integration:
- RAT malware for Windows 10/11
- Remote desktop hacking tool
- Cybersecurity threat analysis
Technical Specifications & Architecture
FeatureDescription
PlatformWindows (All modern versions)
Architecture64-bit compatible
Connection ProtocolTCP/IP with custom ports
Default Test IP127.0.0.1
Payload TypeExecutable (Server.exe – configurable)
PersistenceStartup registry entry, scheduled tasks
Semantic Keywords: Windows RAT malware, TCP/IP malware, RAT payload analysis
Dashboard & Client Management Features
 Client Monitoring
Client Monitoring- Real-time client list & geolocation tracking
- Hardware ID fingerprinting
- Group and team organization for multi-target control
- Active session timestamp logging
- Username & OS detection
- Privilege level identification
- Webcam availability & monitoring
- Network usage metrics (sent/received bytes)
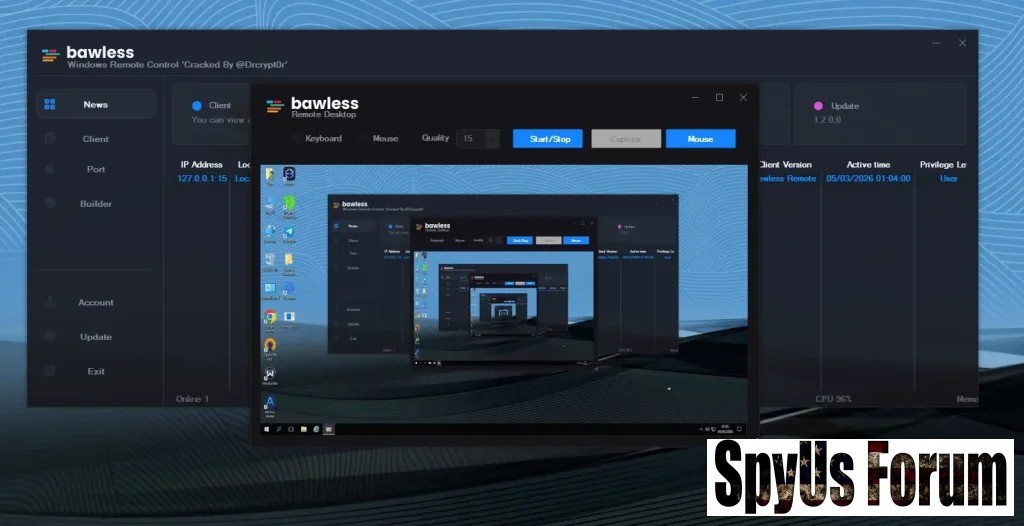
Remote Control & Surveillance Capabilities
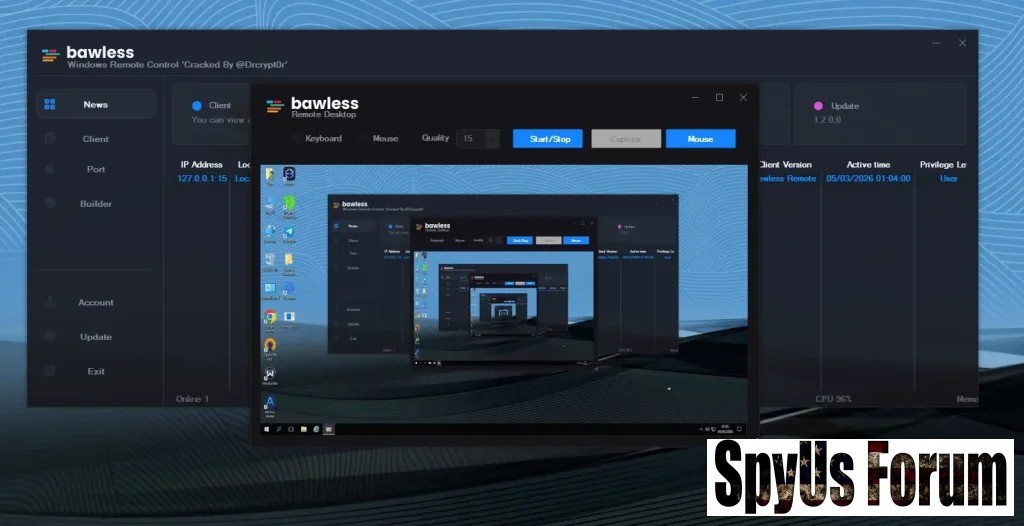 Remote Administration Features
Remote Administration Features- Remote Desktop Access
- File Manager (Upload/Download/Delete)
- Registry Editor (Regedit)
- Process Manager
- Command Prompt (CMD execution)
- Keystroke logging (keylogger)
- Browser activity logging (online keylogger)
- Password recovery from apps & browsers
- Webcam capture and remote activation
- Ransomware & file encryption
- Forced website redirection
- System profiling for targeted attacks
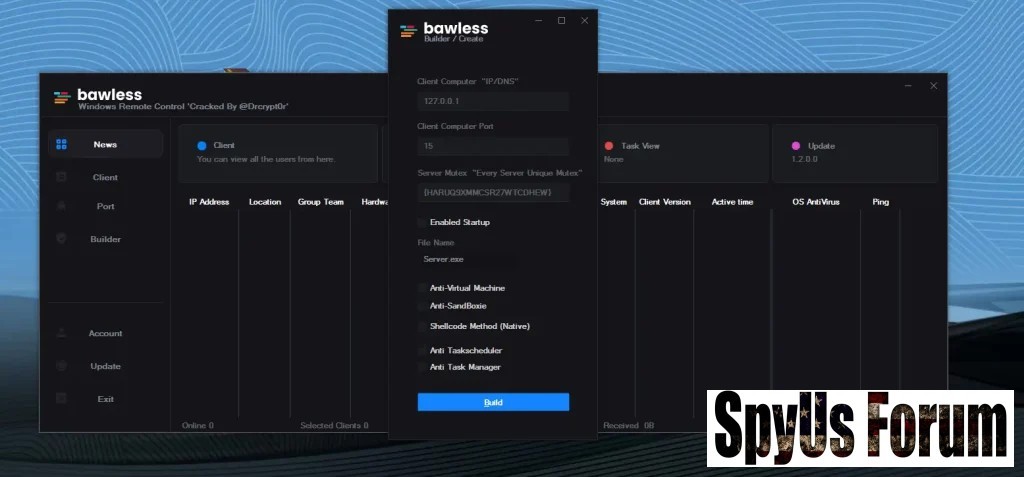
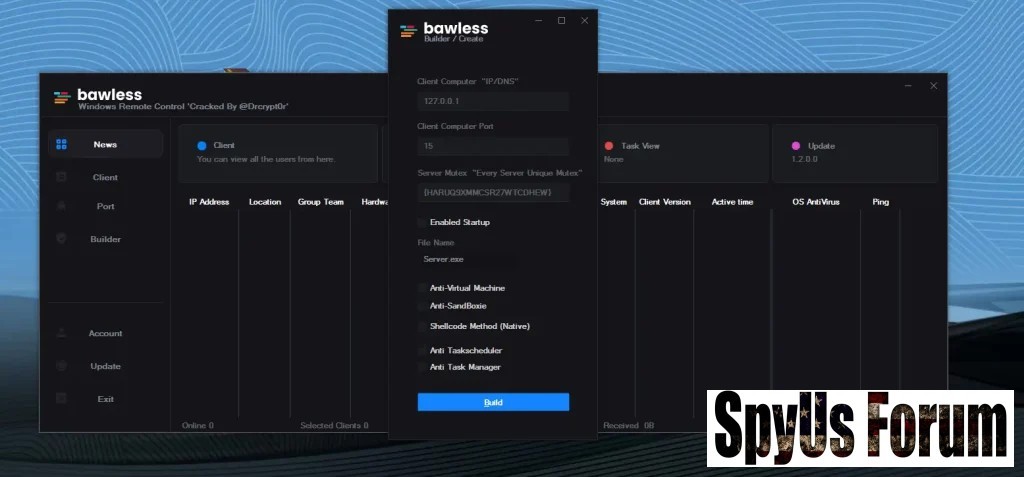
Builder Configuration & Stealth Features {#builder-stealth}
Connection Customization
- Custom IP/DNS & port selection
- Server identifier strings
- Executable file renaming
- Anti-Virtual Machine detection
- Sandbox evasion
- Task Manager and Task Scheduler interference
- Native shellcode injection
Persistence & Targeting Mechanisms {#persistence}
- Startup persistence via registry and scheduled tasks
- Multi-client targeting & group assignments
- Long-term system compromise
Security Risks & Enterprise Threats {#security-risks}
Bawless RAT 2026 Cracked poses major threats:
- Full administrative access
- Credential harvesting & keylogging
- Ransomware deployment
- Anti-analysis evasion
- Persistence after reboot
Detection Indicators & Monitoring {#detection}
Security professionals should monitor:
- Suspicious executables (Server.exe variants)
- Unusual outbound TCP/IP connections
- Unexpected startup entries
- High CPU & memory usage without active applications
- Unauthorized webcam activation
Download Bawless RAT 2026 Cracked
Prevention & Protection Strategies {#protection}
Individual Measures
- Avoid cracked downloads
- Keep Windows updated
- Enable firewall and endpoint security
- Use strong passwords & multi-factor authentication
- Deploy EDR solutions
- Monitor outbound traffic & unusual system activity
- Conduct phishing awareness training
- Implement Zero Trust network access
FAQ
Q1: What is Bawless RAT 2026 Cracked?
A: A Windows RAT malware modified to bypass licensing, providing unauthorized remote access and spying capabilities.
Q2: Is it legal?
A: No, distributing or using cracked RATs is illegal and considered cybercrime.
Q3: How does it infect systems?
A: Through phishing, trojanized downloads, cracked software, and malicious installers.
Q4: Can detect it?
A: Modern antivirus and EDR tools can detect behavior anomalies if definitions and rules are up-to-date.