 XWorm V6.0 Cracked Explained: Complete Features, Builder Plan & Cybersecurity Risks
XWorm V6.0 Cracked Explained: Complete Features, Builder Plan & Cybersecurity RisksIntroduction
In the rapidly evolving world of cybersecurity, XWorm V6.0 Cracked has become a notable concern. This version represents a modified Remote Access Trojan (RAT) where licensing restrictions have been removed, making it more accessible but significantly more dangerous.
Table of Contents
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
What is XWorm V6.0 Cracked?
XWorm V6.0 Cracked is an unauthorized version of a RAT that enables remote control over infected systems.
Core Functions:
- Remote Control → Access and operate systems remotely
- Surveillance → Monitor users via camera and microphone
- Data Theft → Capture passwords and sensitive information
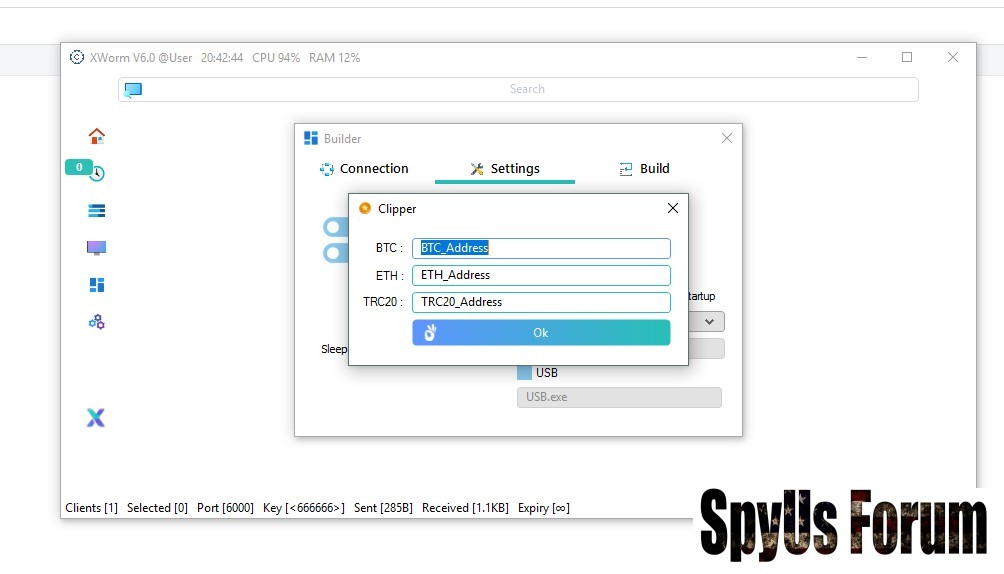
- Financial Fraud → Manipulate cryptocurrency transactions
- Security Bypass → Evade detection systems
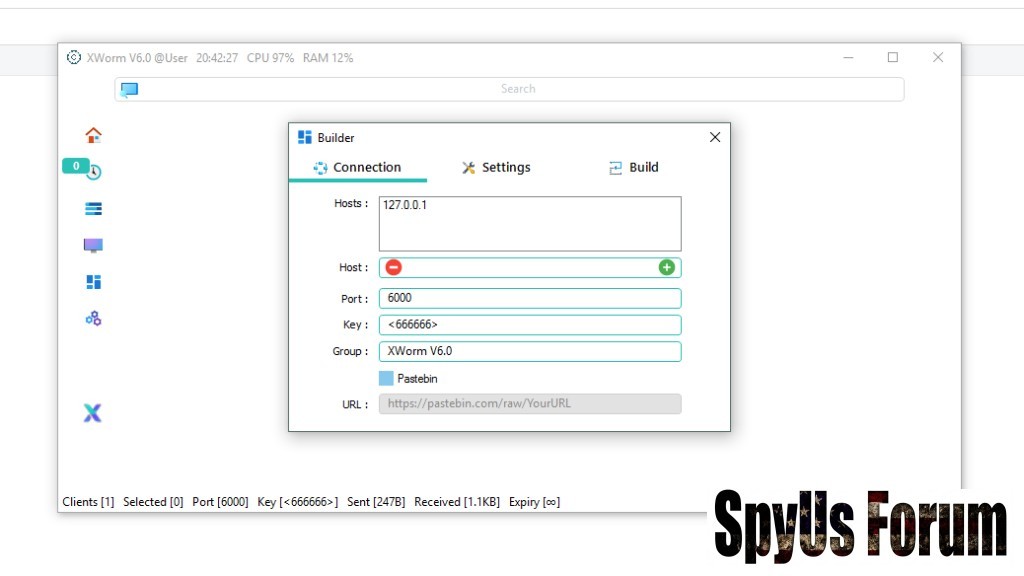
Builder Main Plan
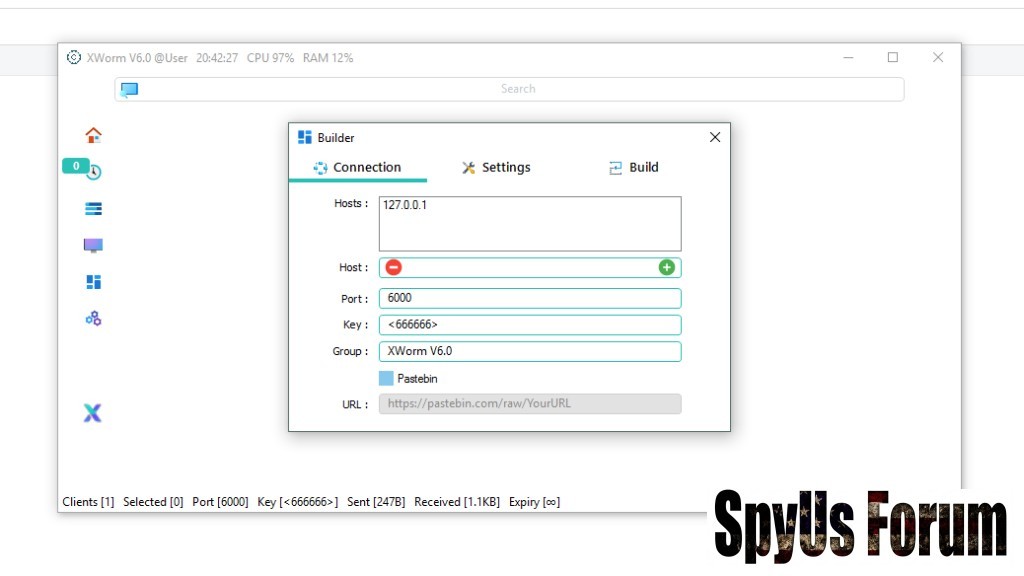 Connection Setup
Connection Setup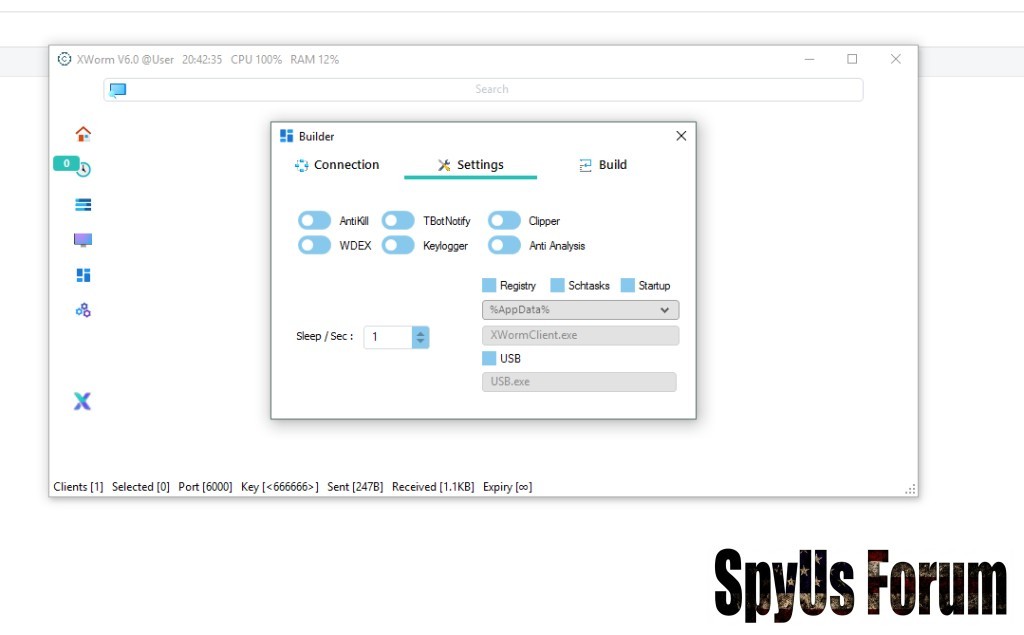
- Host → Defines the server connection for communication
- Port → Channel used for data transfer between attacker and victim
- Key/Password → Authentication required for access
- Group → Organizes infected systems into categories
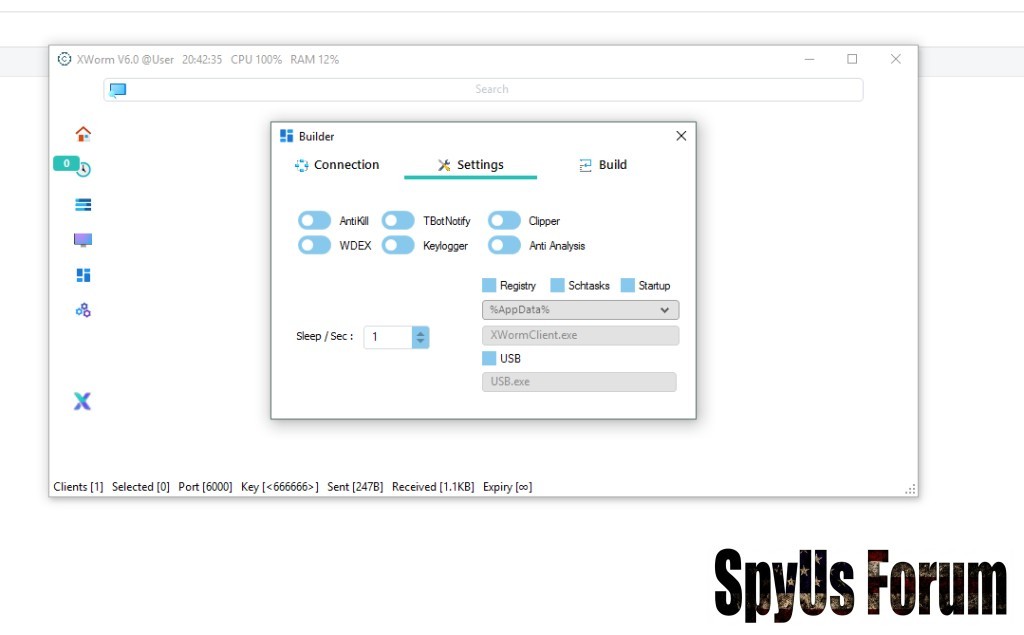
- Registry Entry → Ensures malware runs at system startup
- Scheduled Tasks → Re-executes malware automatically
- Startup Folder → Launches malware after user login
Installation Plan
- AppData → Hidden directory for stealth
- Temp Folder → Temporary storage often ignored
- LocalAppData → Blends with legitimate apps
- ProgramData → Shared system location
- UserProfile → Maintains user-level persistence
- USB Spread → Infects other systems via removable drives
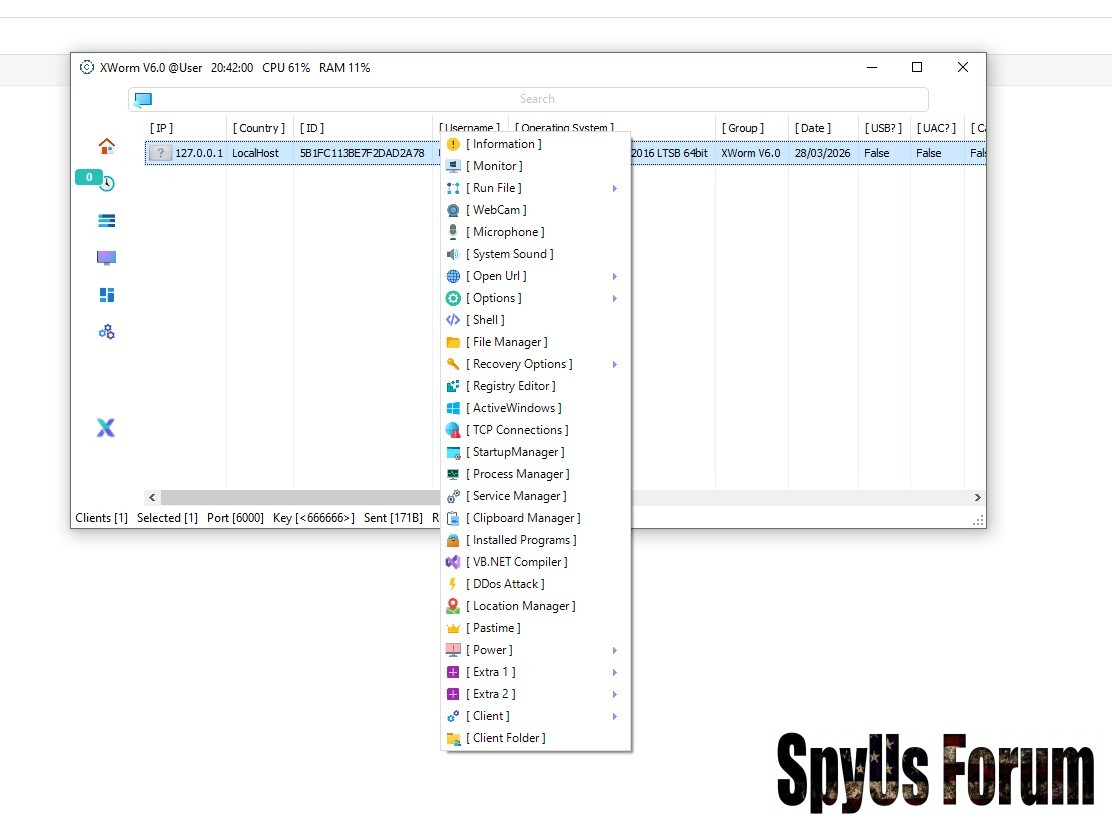
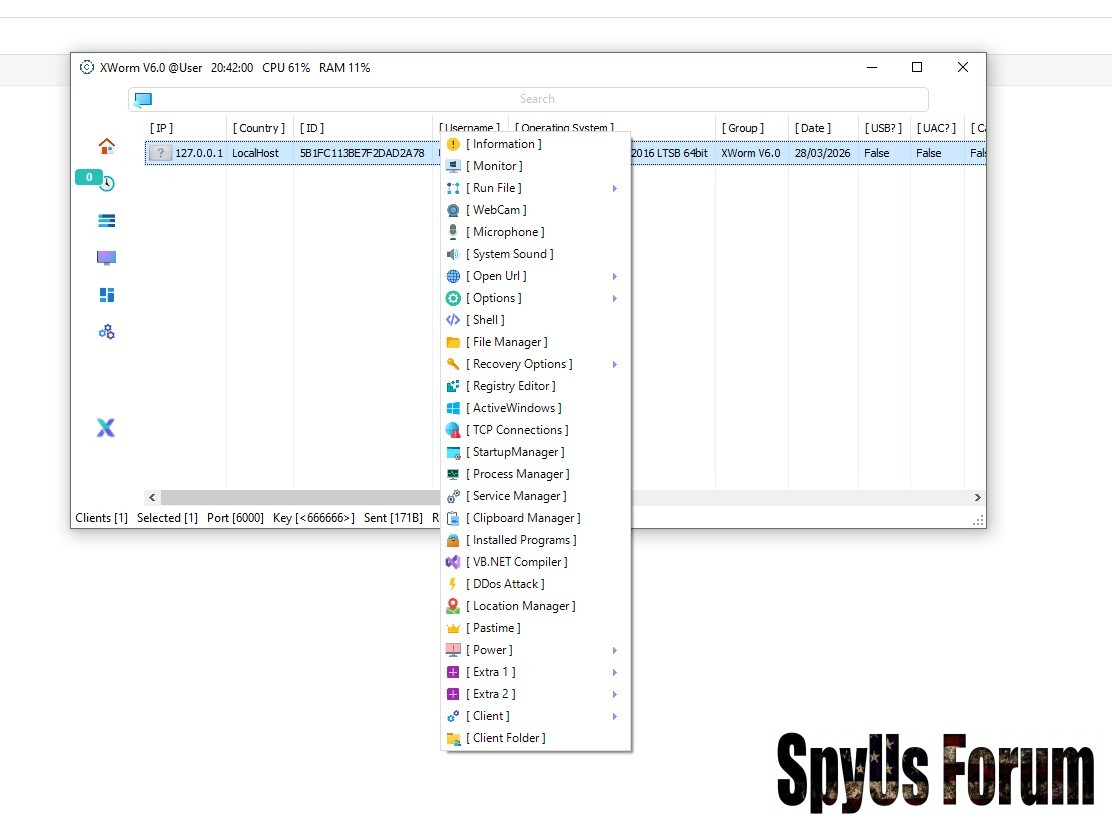
Surveillance Features
- Webcam Access → Captures images and videos remotely
- Microphone Recording → Records conversations and ambient sound
- System Audio Capture → Records internal device audio
- Keylogger → Logs keystrokes including passwords and messages
- Active Window Tracking → Monitors user activity and open applications
- Location Tracking → Estimates user location using network data
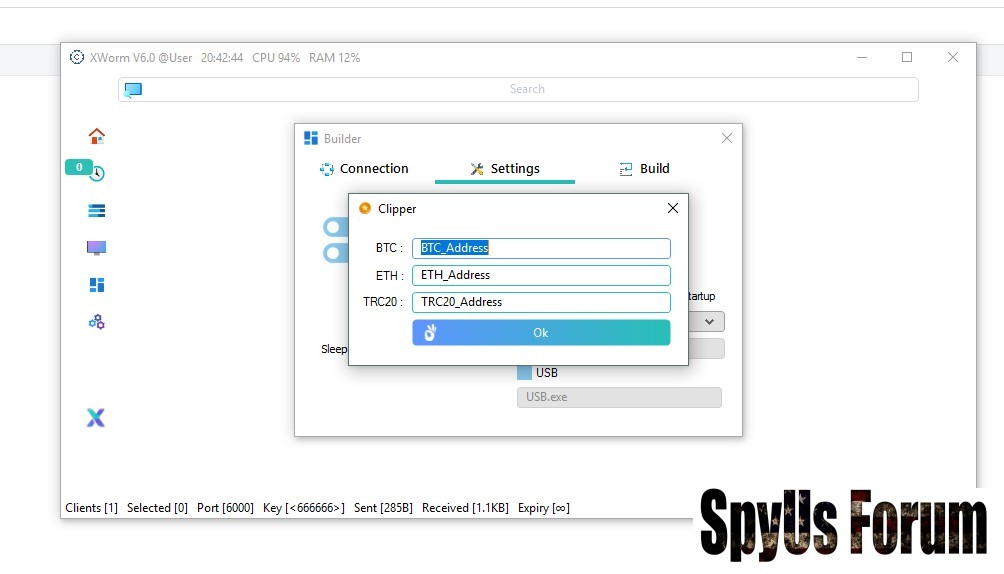
- Clipboard Hijacking (Clipper) → Replaces copied cryptocurrency wallet addresses to redirect funds
- File Manager → Access, modify, and delete files
- Registry Editor → Change system configurations
- Process Manager → View and terminate running processes
- Service Manager → Control background system services
- DDoS Capability → Use infected system in network attacks
- UAC Bypass → Gain elevated privileges without user consent
- Power Control → Shutdown, restart, or log off system
- AntiKill → Prevents termination of the malware
- Anti-Analysis → Detects sandbox or virtual environments
- Exclusion → Attempts to bypass security
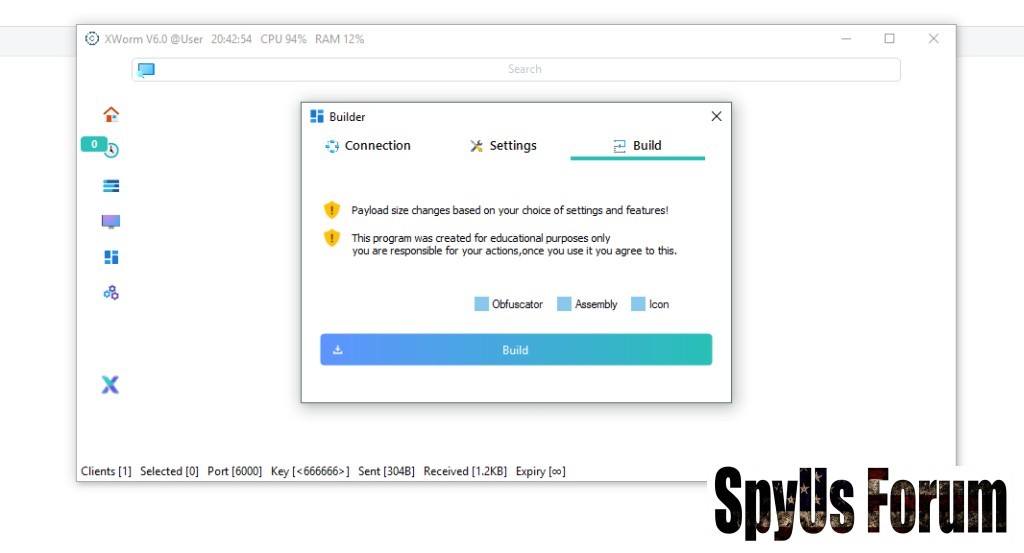
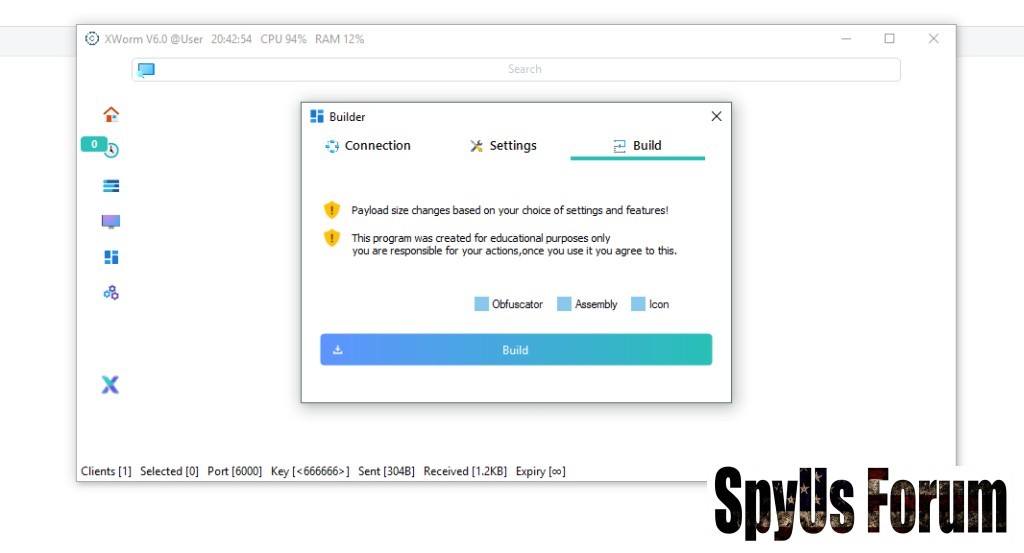
- File Binder → Combines malware with legitimate files
- Icon Changer → Disguises files as safe formats
- Downloader → Fetches additional malicious payloads
- Compiler → Builds malware directly from the interface
- Hidden malware or spyware
- Backdoor access for third parties
- No updates or official support
- Legal consequences
- Risk of self-infection
Threat Overview
- Easily accessible online
- Highly customizable
- Difficult to detect
- Capable of large-scale cyber attacks
- Avoid downloading cracked software
- Do not open suspicious files or links
- Use reliable solutions
- Disable unknown USB devices
- Keep operating system updated
Conclusion
XWorm V6.0 Cracked is a powerful yet highly dangerous RAT that combines surveillance, system control, and financial theft features.
The cracked nature significantly increases its risk, making it unsafe for both victims and users.
Staying informed and following cybersecurity best practices is essential for protection.
FAQs
What is XWorm V6.0 Cracked?
It is a modified version of a Remote Access Trojan used for remote control and data theft.
Is XWorm V6.0 Cracked safe?
No, it is unsafe, illegal, and may contain hidden malicious code.
How does it spread?
Through downloads, email attachments, and infected USB drives.
Can it harm the installer?
Yes, cracked versions may include hidden backdoors and spyware.
How to stay safe?
Avoid cracked software and use strong cybersecurity practices.