 Introduction
IntroductionThe cybersecurity landscape in 2026 has taken a dangerous turn with the rise of Icarus Evil w0rm Cracked 2026. Once a premium malware toolkit reserved for skilled cybercriminals, it is now widely distributed in cracked form, removing both financial and technical barriers.
Table of Contents
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
You must be registered for see links
-
As a result, cyber threats are no longer limited to advanced attackers—anyone with basic knowledge can now launch powerful attacks.
What is Icarus Evil w0rm Cracked 2026?
Icarus Evil w0rm Cracked 2026 is a highly advanced malware that combines the capabilities of a Remote Access Trojan (RAT) with a self-propagating w0rm.
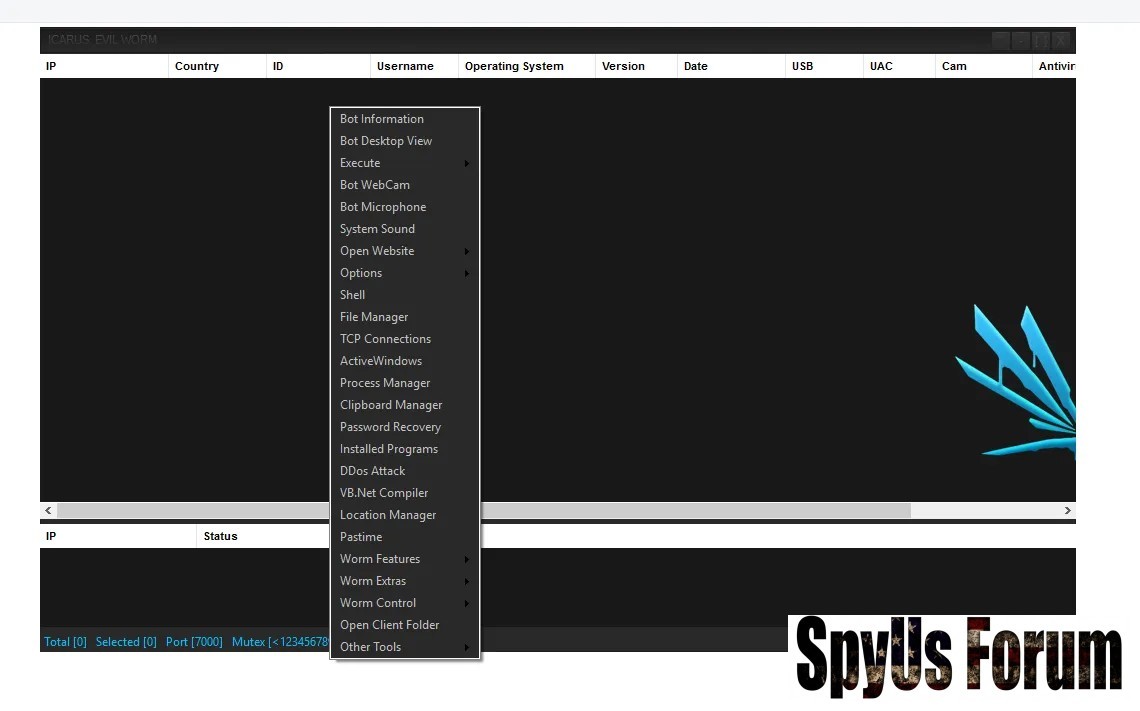
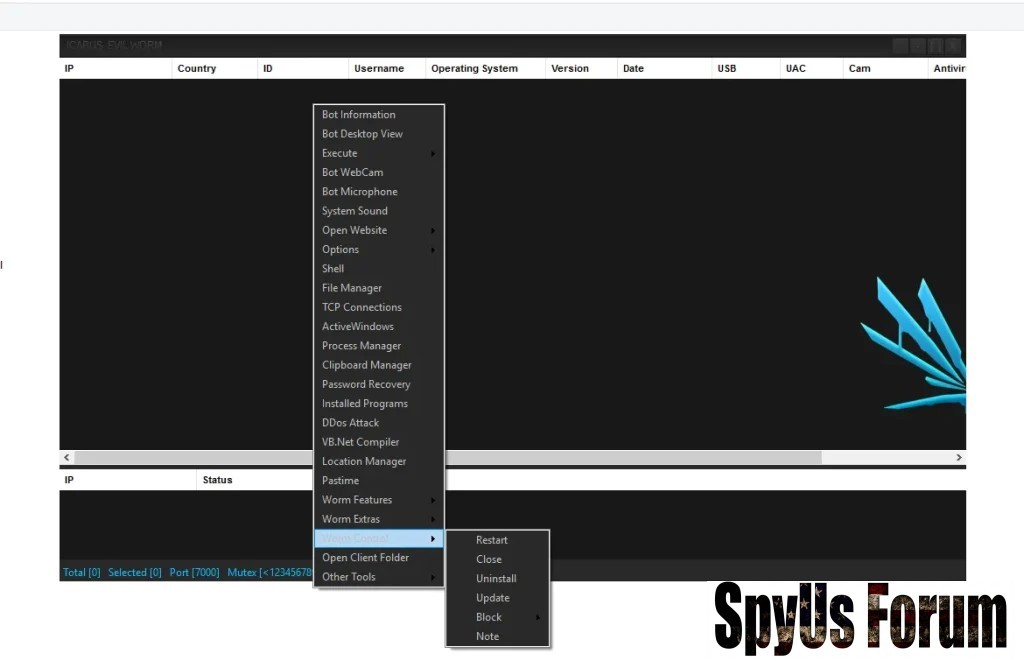
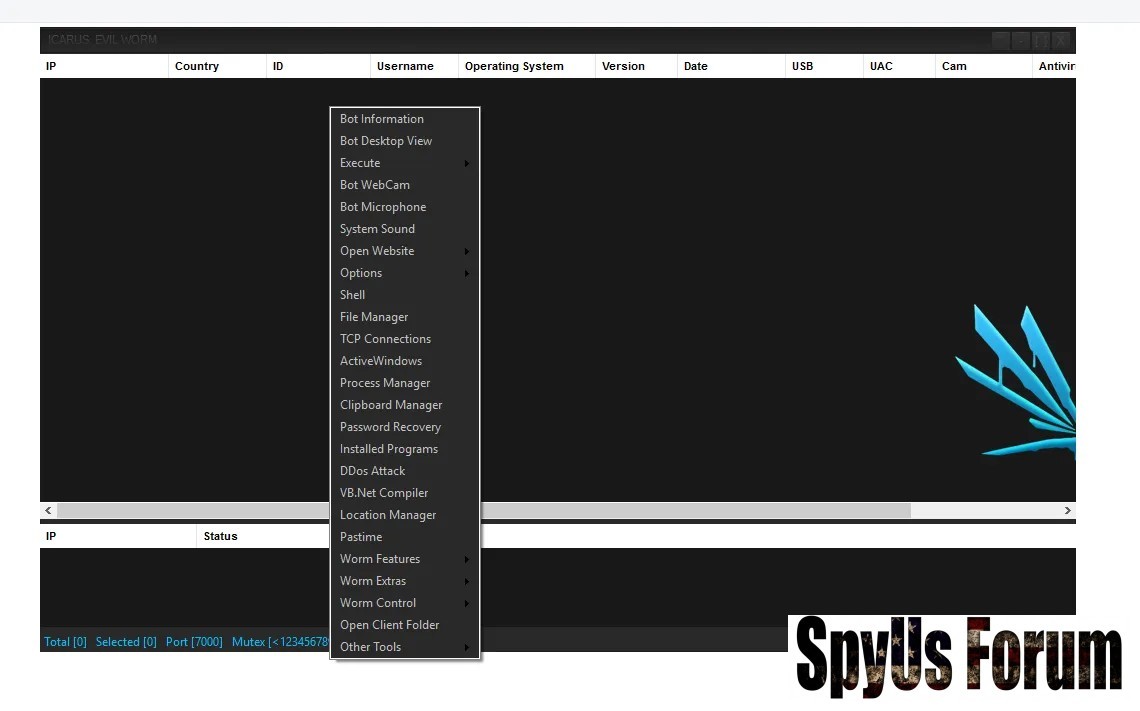
 Core Functionalities of Icarus Evil w0rm Cracked 2026 Explained
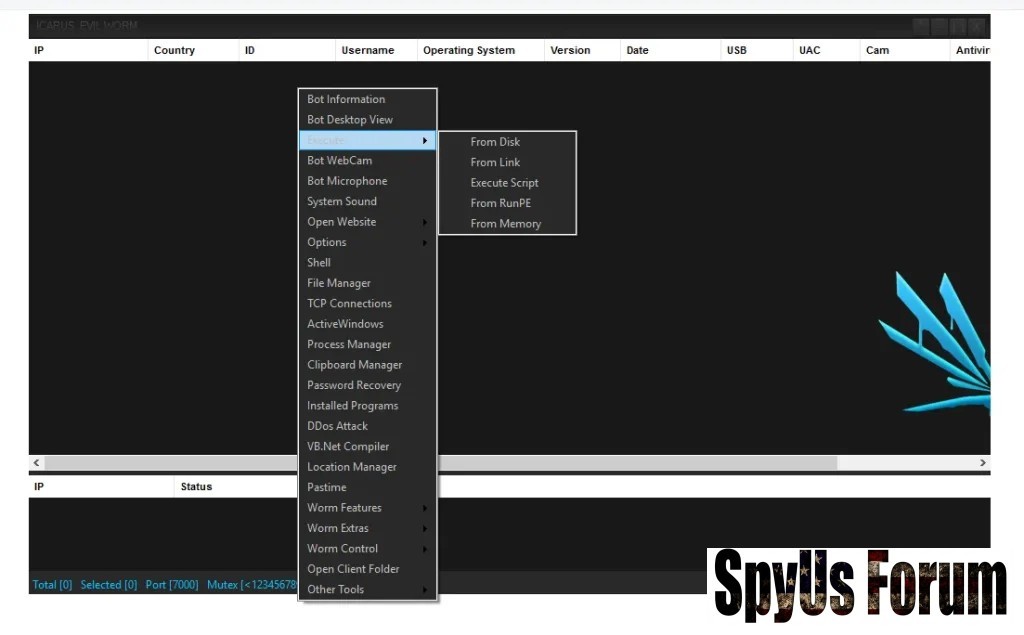
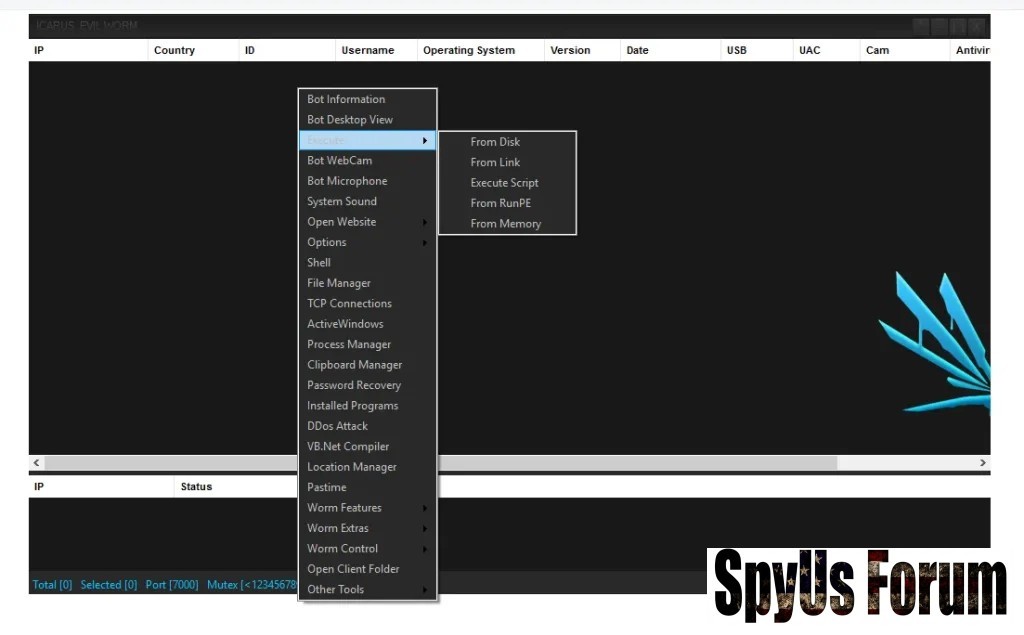
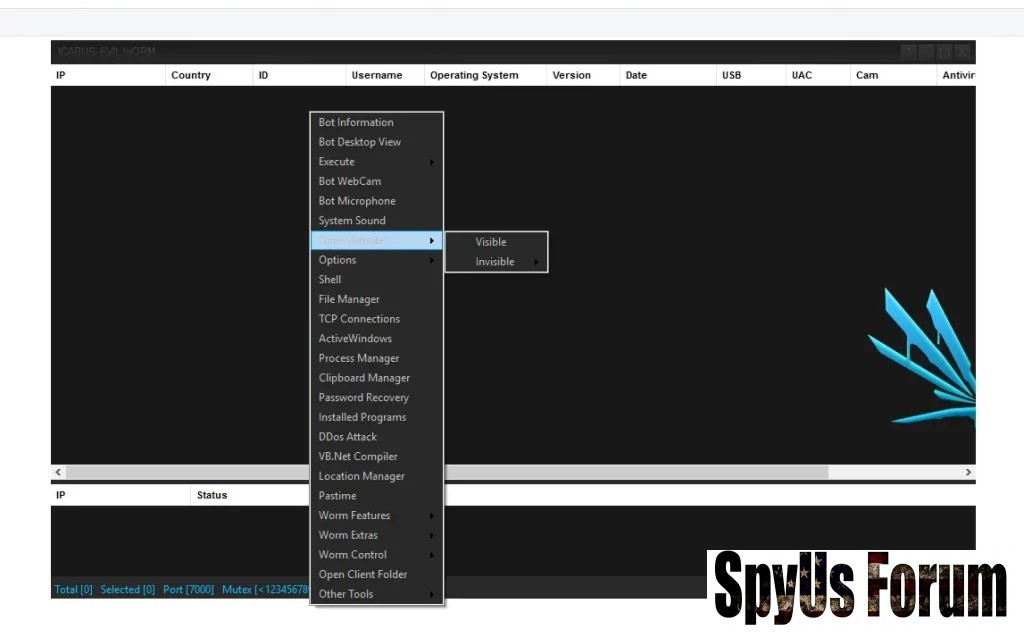
Core Functionalities of Icarus Evil w0rm Cracked 2026 ExplainedRemote System Control
- Gain full access to a victim’s computer
- Execute commands remotely
- Monitor user activity in real time
Surveillance & Monitoring
- Activate webcam secretly
- Record audio through microphone
Data Theft Capabilities
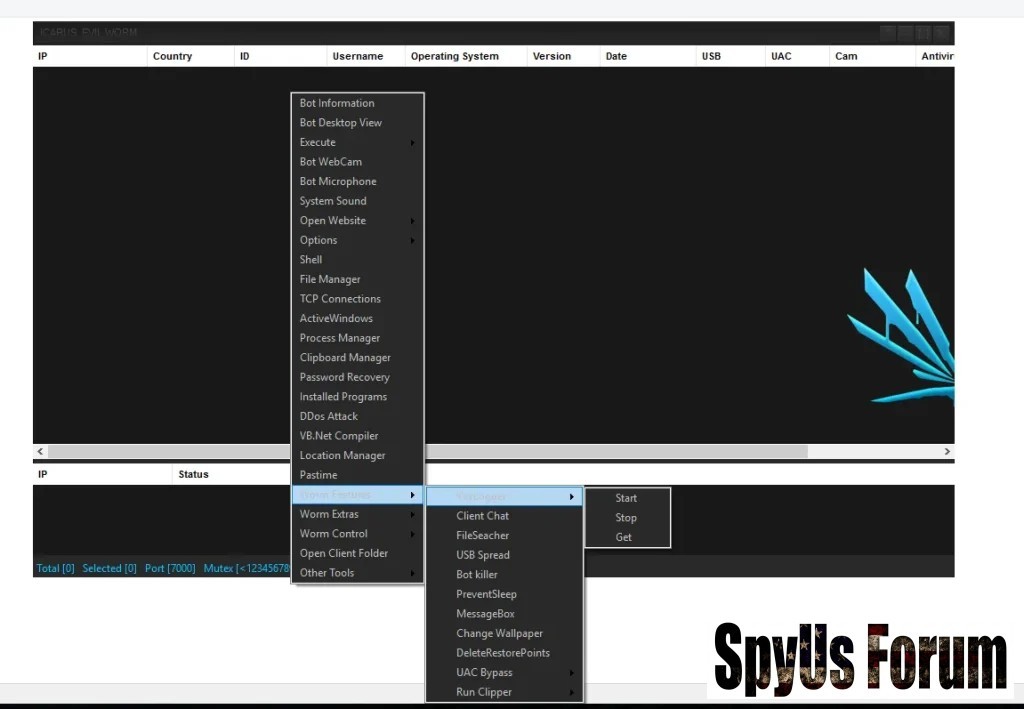
- Extract saved browser passwords
- Access personal and business files
- Capture login sessions and cookies
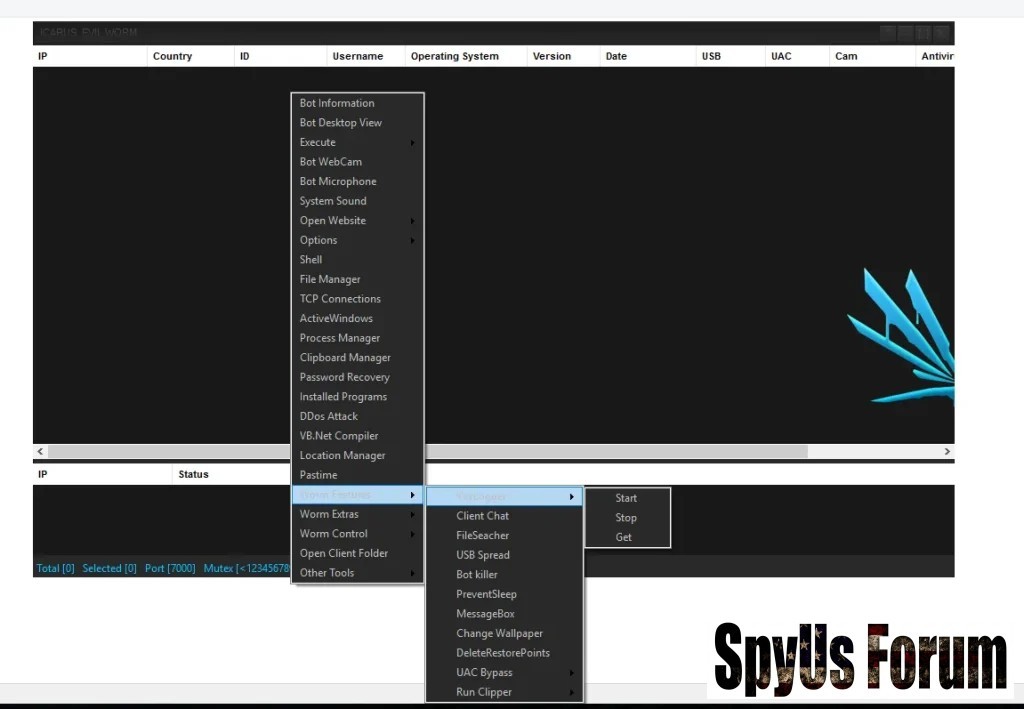
w0rm-Based Propagation
- Spread through USB drives
- Move across internal networks automatically
What is Icarus Evil w0rm Cracked 2026?
The Icarus Evil w0rm 2026 Cracked version is an unauthorized, modified release where all licensing protections have been removed.
 Why This Version is Especially Dangerous
Why This Version is Especially DangerousFree Public Distribution
Previously sold privately, it is now freely available on various platforms.
This dramatically increases the number of potential attackers.
Beginner-Friendly Usage

- Simple interface
- Pre-configured attack modules
Full Feature Unlock
All advanced features are accessible without restriction.
This enables large-scale and highly damaging attacks.
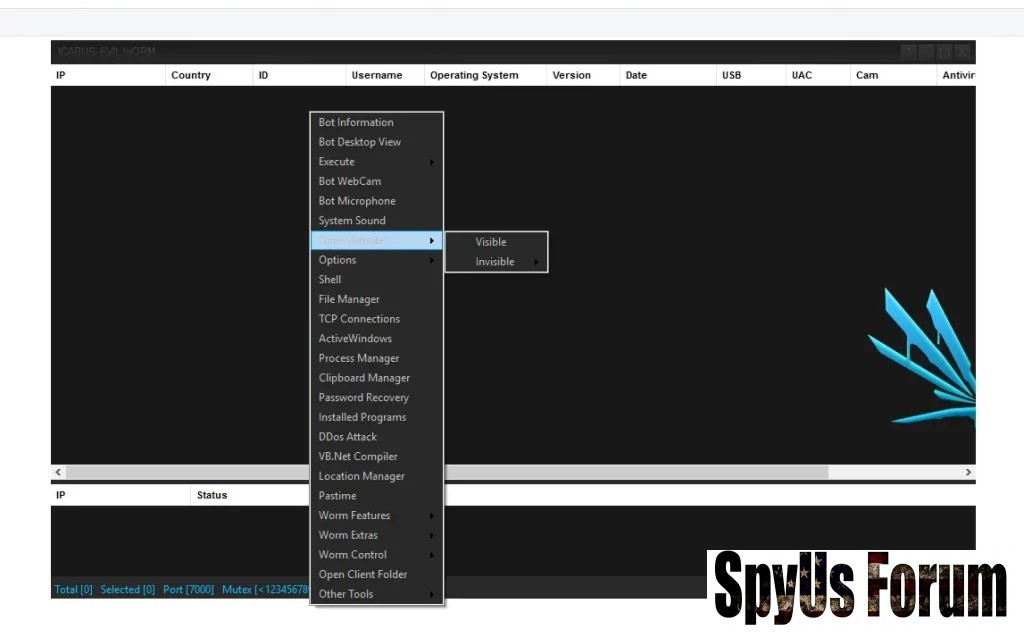
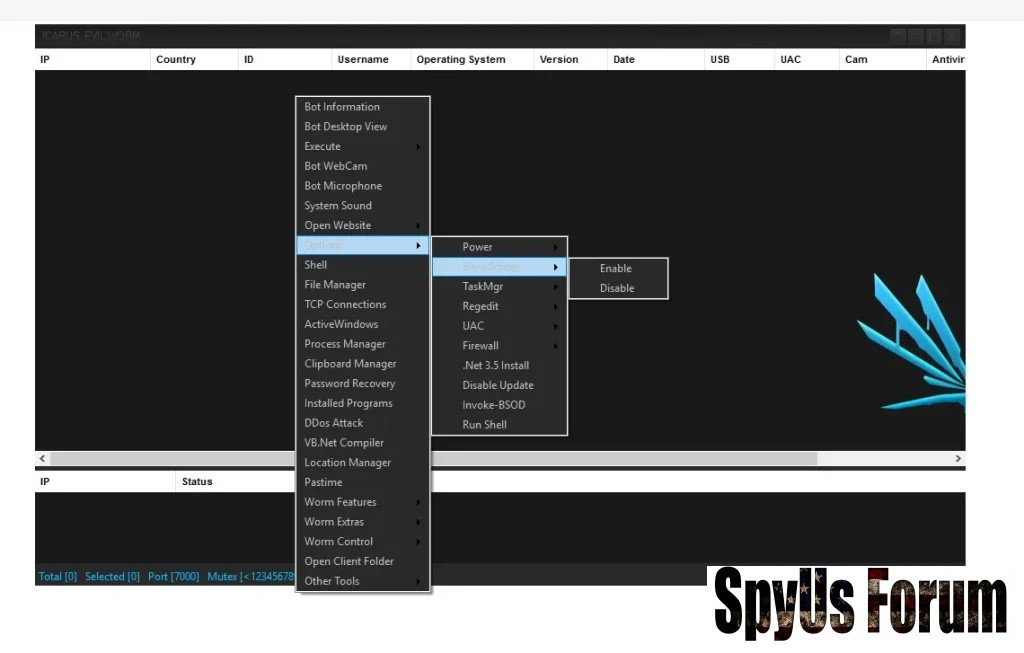
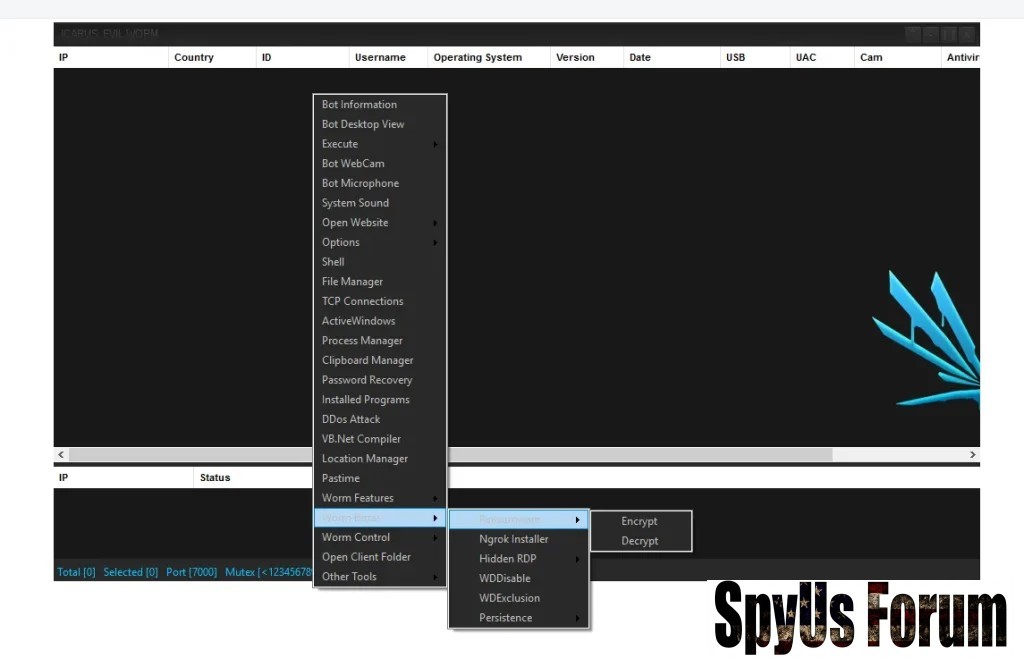
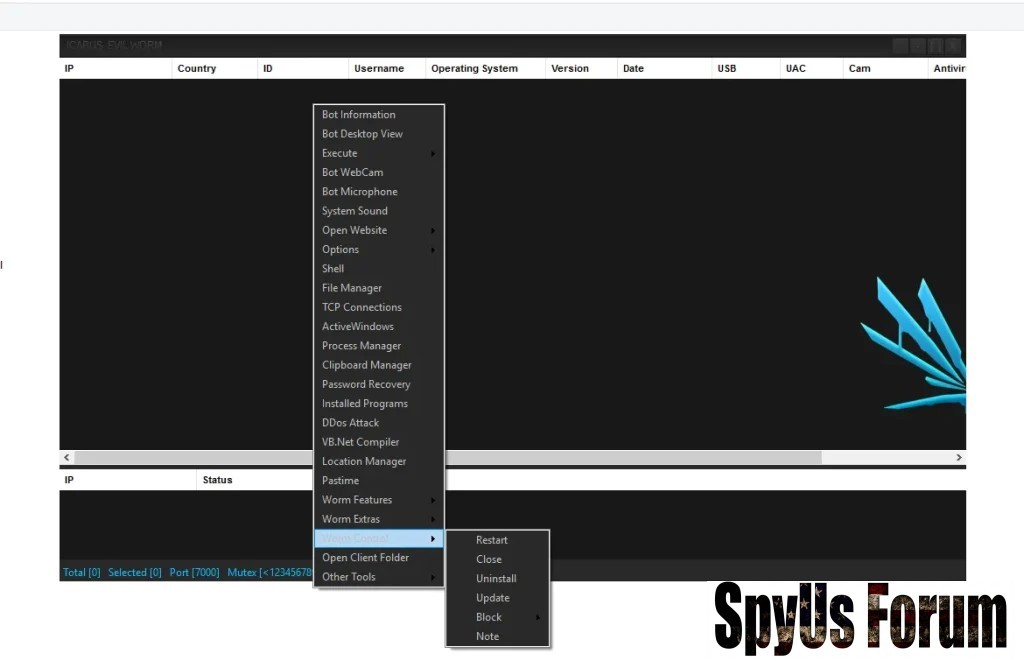
Advanced Features in Detail
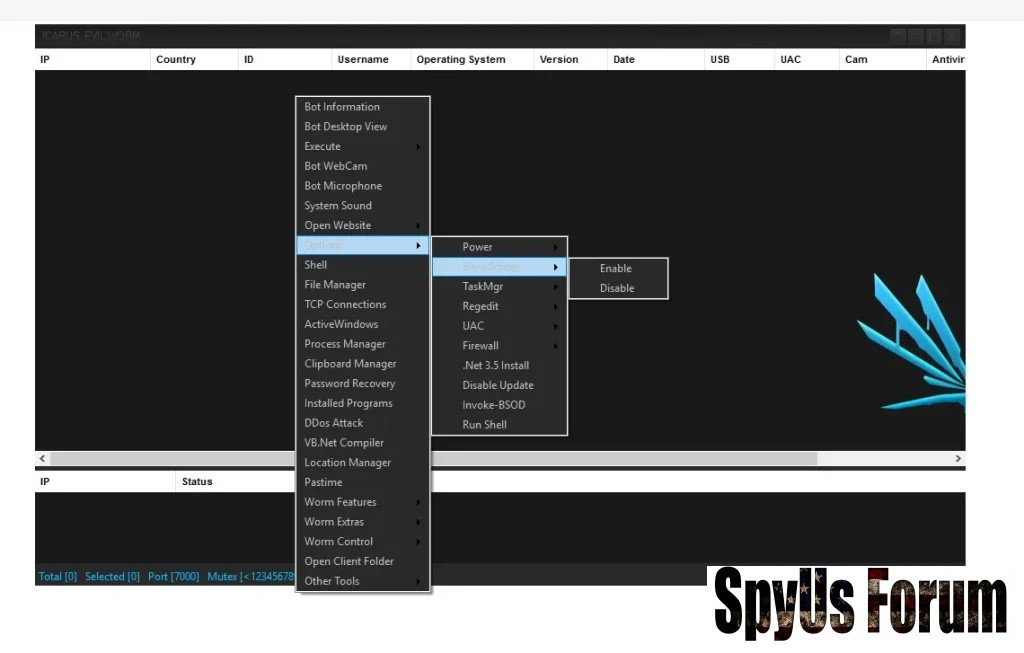
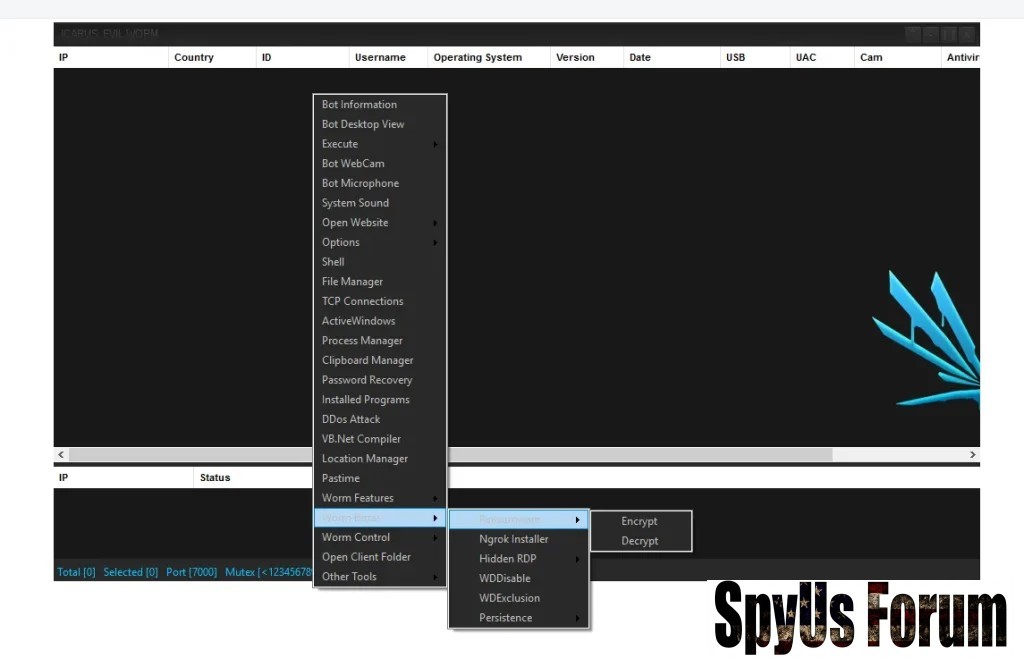
Persistence Mechanisms
- UAC Bypass
This feature allows the malware to gain administrative privileges without triggering security warnings. It ensures deep system access and makes removal difficult. - Prevent Sleep Mode
Keeps the infected system active, maintaining a continuous connection with the attacker’s control panel.
- USB Spread
Infects removable drives, allowing the malware to spread offline between multiple devices. - Network Propagation
Moves laterally across connected systems, targeting shared folders and weak security configurations.
- Delete Restore Points
Removes system recovery options, preventing users from restoring their system to a safe state. - DDoS Attack Module
Converts infected devices into bots that can be used in large-scale Distributed Denial-of-Service attacks.
- Clipboard Hijacking
Monitors copied data and replaces cryptocurrency wallet addresses, redirecting funds during transactions. - Password Recovery Tools
Extracts stored credentials from browsers and applications, enabling unauthorized access to accounts.
- Antivirus Bypass
Uses obfuscation techniques to avoid detection by security software. - Stealth Execution
Runs silently in the background, making it difficult for users to notice unusual activity.
Reduced Entry Barrier
Advanced hacking tools are now accessible to inexperienced users, increasing the number of cyber attackers globally.
Shift Toward Mass Attacks
Instead of targeting specific individuals, attackers now launch large-scale campaigns affecting thousands of users.
Hidden Risks for Attackers
Cracked versions often contain hidden backdoors, meaning attackers themselves can be monitored or compromised.
Real-World Impact in Icarus Evil w0rm Cracked 2026
The spread of Icarus Evil w0rm 2026 Cracked has led to:
- Increased phishing and malware campaigns
- Rapid growth of botnet networks
- Higher rates of identity theft
- Financial losses for individuals and businesses
Cybersecurity Protection Guide
Disable AutoPlay
Prevents automatic execution of malicious files from USB devices, reducing infection risk.
Use Application Control (AppLocker)
Restricts unauthorized applications from running, improving system security.
Keep Systems Updated
Regular updates patch vulnerabilities that malware often exploits.
Monitor Network Traffic
Detect unusual activity, especially on uncommon ports like Port 7000, which may indicate malware communication.
Install Advanced Security Software
Use antivirus solutions with real-time protection and behavioral detection features.
Download Icarus Icarus Evil w0rm Cracked 2026
Conclusion
The rise of Icarus Evil w0rm Cracked 2026 highlights a critical shift in cyber threats. By removing cost and complexity barriers, it has enabled widespread misuse of powerful malware tools.
For individuals and organizations alike, adopting strong cybersecurity practices is essential to minimize risk and protect sensitive data.
FAQs
What is Icarus Evil w0rm Cracked 2026?
It is a cracked version of a RAT-w0rm malware that allows attackers to control systems and spread infections.
Is it illegal in the US and Europe?
Yes, creating, distributing, or using malware is illegal and punishable under cybersecurity laws.
How does it spread?
Through USB devices, phishing emails, malicious downloads, and network vulnerabilities.
Why is the cracked version more dangerous?
Because it is freely accessible and easy to use, increasing the number of cyberattacks.
Can antivirus detect it?
Some versions can be detected, but advanced variants may evade detection, making prevention essential.
What are common signs of infection?
- Slow system performance
- Unknown background processes
- Unusual network activity
Attachments
-
 3bc8d9bb409dfe2b6643da14783027fc.jpg73.7 KB · Views: 0
3bc8d9bb409dfe2b6643da14783027fc.jpg73.7 KB · Views: 0 -
 3d6ed24435d66ae318b4d561baaa6fd3.jpg68.7 KB · Views: 0
3d6ed24435d66ae318b4d561baaa6fd3.jpg68.7 KB · Views: 0 -
 ae47fd6fdd8d3f10cd1e49933b1ab0a4.jpg75.7 KB · Views: 0
ae47fd6fdd8d3f10cd1e49933b1ab0a4.jpg75.7 KB · Views: 0 -
 b0ee65a5ed481b746cf50d7a516fd56e.jpg78.9 KB · Views: 0
b0ee65a5ed481b746cf50d7a516fd56e.jpg78.9 KB · Views: 0 -
 40290a741aeeaaf46a4fbf752f1e333e.jpg73.5 KB · Views: 0
40290a741aeeaaf46a4fbf752f1e333e.jpg73.5 KB · Views: 0 -
 255ef141d34fe0205710bc92a38e0420.jpg68.8 KB · Views: 0
255ef141d34fe0205710bc92a38e0420.jpg68.8 KB · Views: 0 -
 c5f5f2b68c4fbb75526dcd79bb8483e8.jpg65.9 KB · Views: 0
c5f5f2b68c4fbb75526dcd79bb8483e8.jpg65.9 KB · Views: 0 -
 dc58ceded2352ad9a87dde5473dd07c7.jpg84.3 KB · Views: 0
dc58ceded2352ad9a87dde5473dd07c7.jpg84.3 KB · Views: 0

